ActiSoft Technology
@actisoft_tech
Managed Security Services Provider to SME's.
We partner with you to protect your business so you can focus on growing your brand
ID: 930500759304704001
https://www.actisofttechnology.com/ 14-11-2017 18:20:43
3,3K Tweet
105 Followers
181 Following







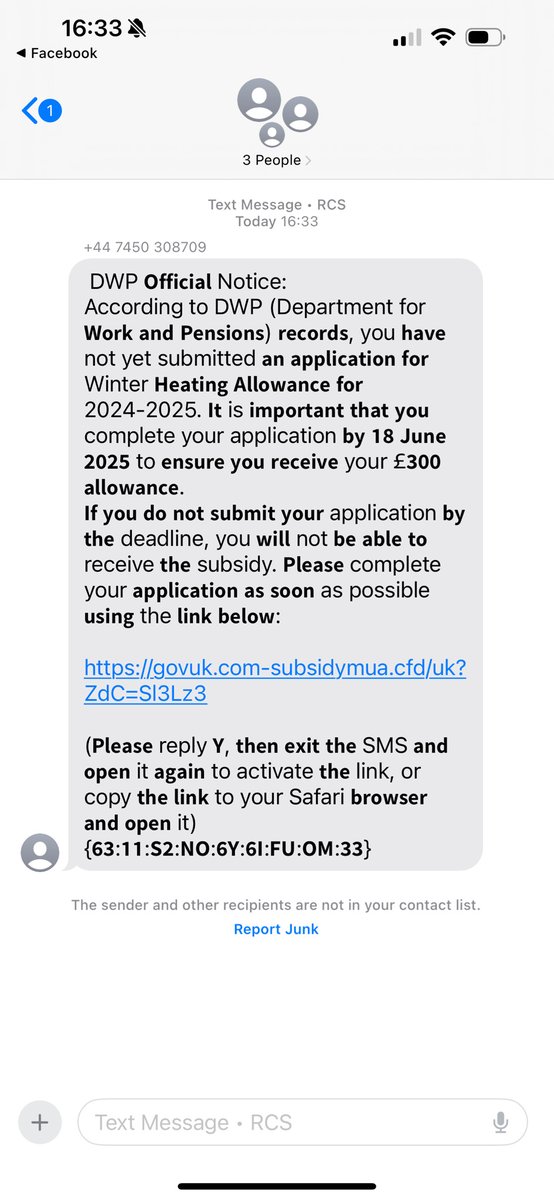
When you report a phishing email to [email protected] you get a reply with details of what they've achieved As of March 2025, the number of reports received stands at more than 40,916,893, with the removal of more than 214,614 scams across 387,536 URLs