
ElAnanyAli
@abdallaeg1
Guardian of the digital realm, slayer of cyber dragons, and occasional breaker of firewalls.
ID: 1267136501772619777
31-05-2020 16:51:10
125 Tweet
221 Followers
741 Following



🚨🇷🇺🇮🇱 Putin isn’t an “EVIL TERRORIST,” but ISRAEL IS! Follow The Saviour (source)


Israeli troops shoot & injure a young Palestinian girl for looking out her bedroom window: israelis? what planet? not ours | Jessica Hayes


@Ebn_ElQonsol202 أحمد الطيب الجامعة العربية للإنصاف لها "موقفاً" كبيراً يسع أكثر من مائة سيارة أمام المبنى - جلال عامر












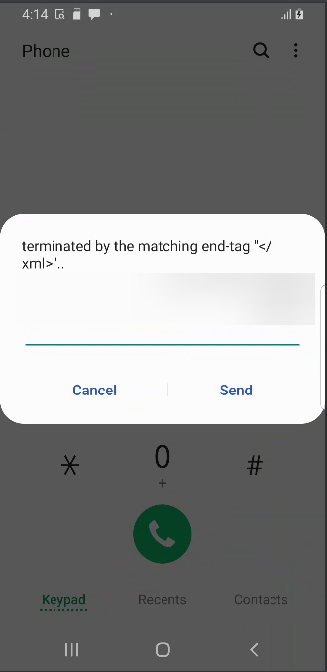


![ElAnanyAli (@abdallaeg1) on Twitter photo A real-world example I found in the wild:
In this code, accountId is an array, but parseInt([1111, 2222]) → 1111, leading to incorrect auth checks! This could let unauthorized users access data.
#bugbountytips #BugBounty #JavaScript #InfoSec A real-world example I found in the wild:
In this code, accountId is an array, but parseInt([1111, 2222]) → 1111, leading to incorrect auth checks! This could let unauthorized users access data.
#bugbountytips #BugBounty #JavaScript #InfoSec](https://pbs.twimg.com/media/GmuyG1DXsAA0yNQ.jpg)