Ah Med
@a_web_plus
Sec|Telco|RF enthusiast
ID: 757643112017780736
25-07-2016 18:26:09
647 Tweet
1,1K Followers
1,1K Following












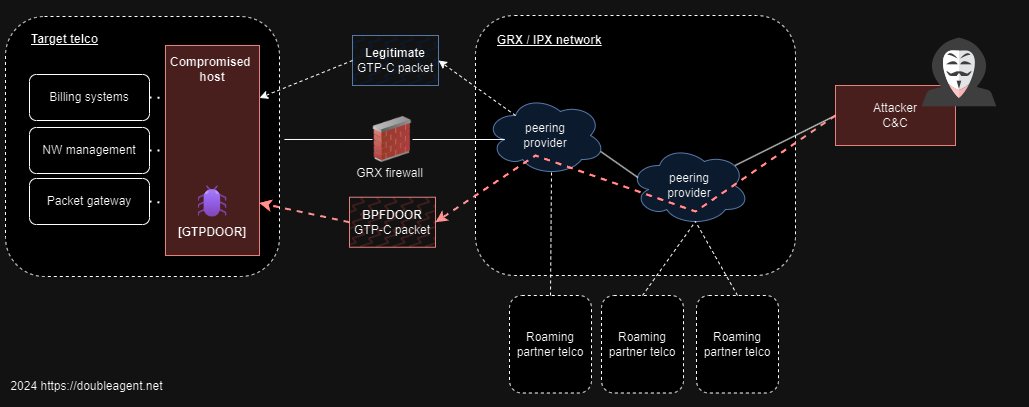
“A fix is long overdue for … the technical vulnerabilities at the heart of the world’s mobile communications networks.” profdeibert and Gary Miller from The Citizen Lab on the security deficiencies associated with cell phone “roaming.” lawfaremedia.org/article/when-y…

1/11 Today, we’re releasing details of a small but interesting mobile #vulnerability called MMS Fingerprint, reportedly used by #NSOGroup. How this might work, and how we found it, is a bit unusual. enea.com/insights/dusti… Enea AB Joseph Cox Ryan Gallagher Catalin Cimpanu Lorenzo Franceschi-Bicchierai





Last month with Ryan Gallagher we published an investigation into the shady SMS market and its implications for security. For those who want to go deeper Gabriel Geiger and I have written a more technical briefing medium.com/@lighthouserep…

🚨 Many telco vulns never get CVEs. Vendors delay, ignore, or silently patch. Operators? Left in the dark. At P1 Security, we follow a 180-day disclosure policy—document and publish in our private VKB when silence persists. 🔗 p1sec.com/blog/responsib… #CVE #TelecomSecurity #VKB