Itamar
@_r1fl
ID: 712015474679132160
21-03-2016 20:38:12
103 Tweet
126 Followers
542 Following


The slides for the offensivecon talk “Bug Hunting S21's 10ADAB1E FW” of ffmenarini and myself can be found here: dropbox.com/s/2f14ga52jguu… Enjoy! We are still around at the conference so stop by and say hi.

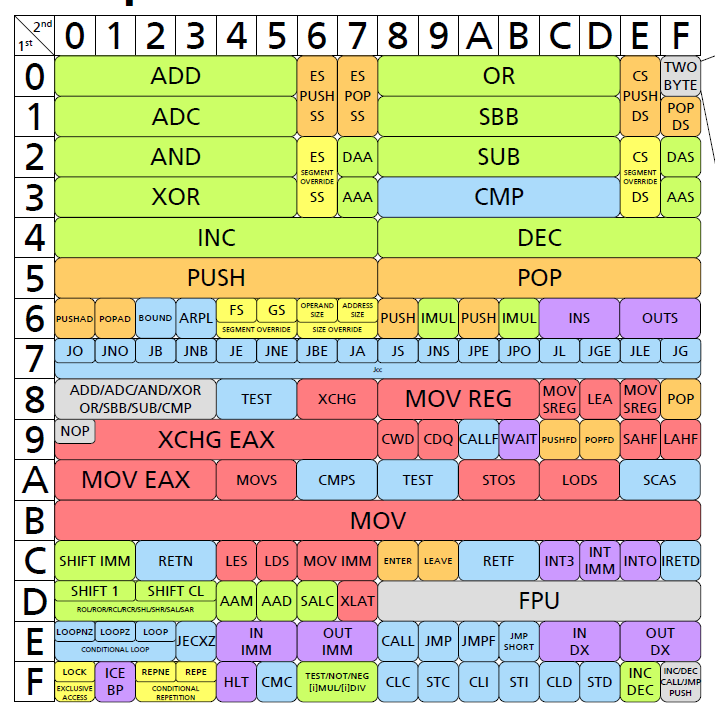
Okay Brandon Falk just blew my mind with this knowledge that x86 is an octal machine. How is this not more commonly understood. The opcode mods use values that are obvious enums when you see them displayed as octal. gist.github.com/seanjensengrey…








Log4Harmony: we've heard that vulns in Android log device drivers are cool, so here are some UAF, race condition, and KASLR leak bugs in Huawei's hwlog from Gyorgy Miru (Gym), reachable from untrusted and isolated app: labs.taszk.io/blog/post/78_h… labs.taszk.io/blog/post/77_h… labs.taszk.io/blog/post/79_h…



The quantum state of Linux kernel garbage collection CVE-2021-0920 (Part I) 1ce0ear published an article describing the root cause of a race condition in the garbage collection for SCM_RIGHTS. This bug is used for Android exploitation in the wild. googleprojectzero.blogspot.com/2022/08/the-qu…

Attacking Titan M with Only One Byte Code execution and exfiltration of encryption keys from Google Pixel phone's Secure Element now being presented by Damiano Melotti and Maxime Rossi Bellom at Black Hat #BHUSA Full details are now public in their blog post: blog.quarkslab.com/attacking-tita…

Here are the resources for my talk "Racing Against the Lock: Exploiting Spinlock UAF in the Android Kernel" at offensivecon today. Write-up: 0xkol.github.io/assets/files/R… Slides: 0xkol.github.io/assets/files/O… PoC for CVE-2022-20421: github.com/0xkol/badspin #OffensiveCon2023