Cr4zy_Z3R0o
@z3_roo
ID: 1453397749483905024
27-10-2021 16:26:57
218 Tweet
221 Followers
264 Following




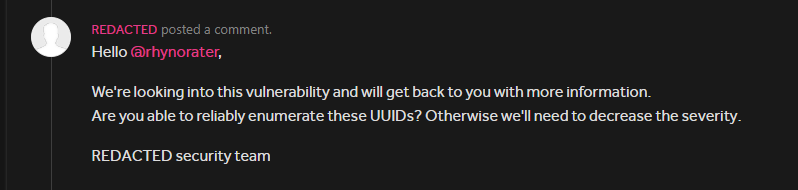
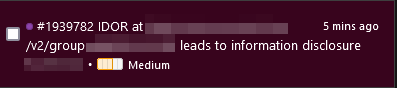
Day 16: Collab with Cr4zy_Z3R0o Time spent: 1 hour 🚨 Bugs found: 1 Bug: 🔥IDOR leads to Info Disclosure🔥 #30daysofbugbounty

Becoming a pro in finding client-side bugs is simple. Not easy, but simple. 1. Go through a JS tutorial and understand the basics. 2. Ready everything on this blog 8x until you understand it: ysamm.com 3. Read JS for Hackers by Gareth Heyes \u2028 4x Then go hack stuff







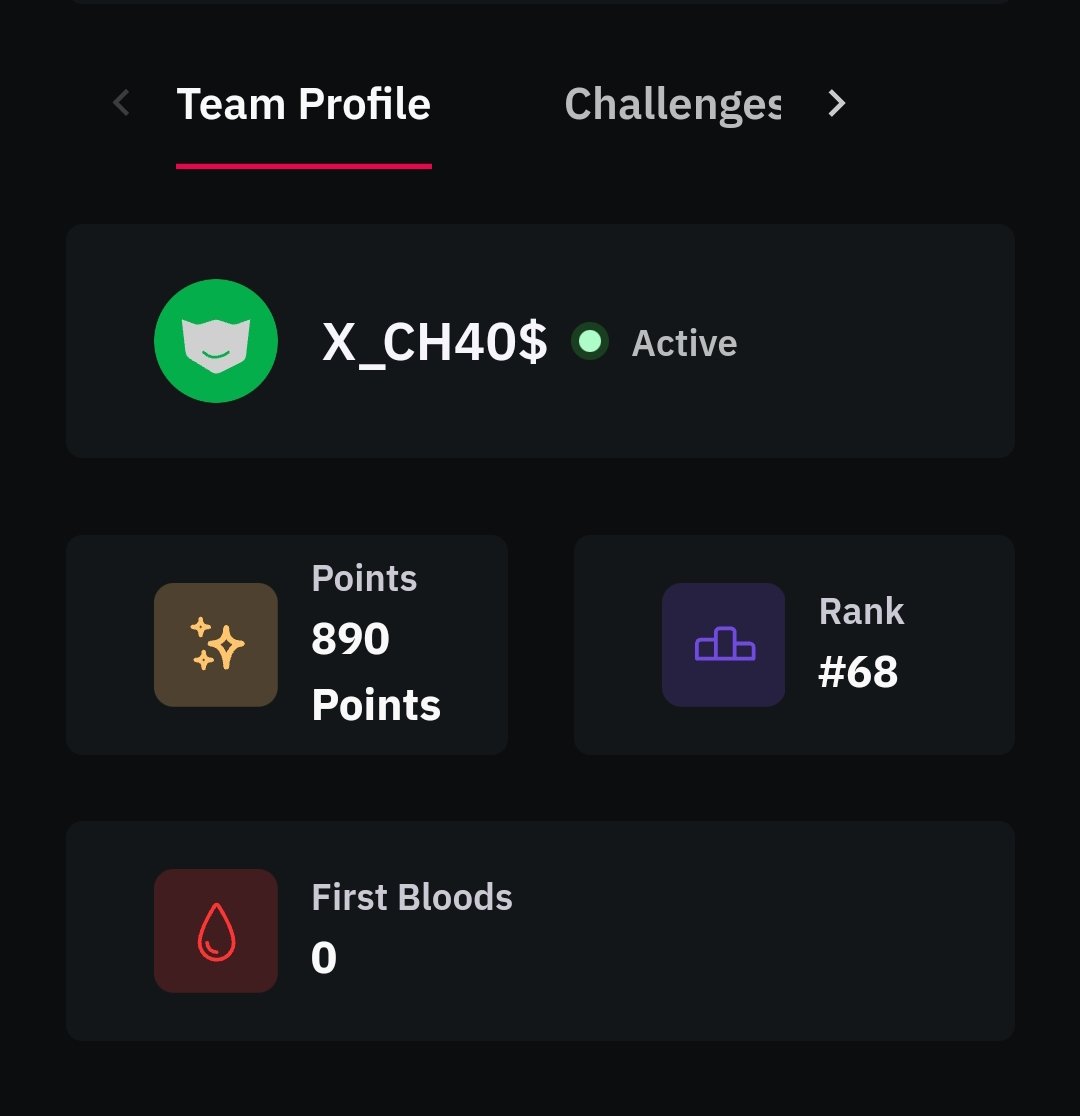
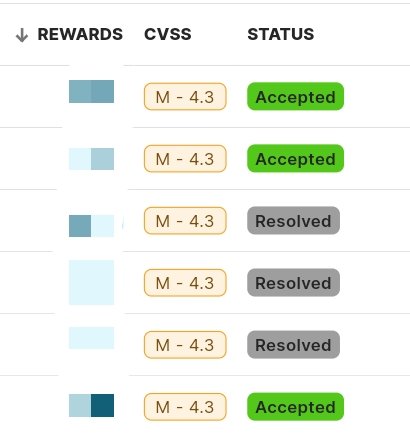
Just got a reward for a vulnerability submitted on YesWeHack ⠵ -- Improper Access Control - Generic (CWE-284). #YesWeRHackers #bughunting #bugbounty




Ben Sadeghipour Pick a niche, become an expert, find bugs maybe even 0days or reverse n-days, and write blogs. Even if you don’t hit those $100k bounties, it’ll be a stepping stone toward a $100k job. What niche? How to pick? Examples? infosec being so vast from web3 sec to web2, mobile,

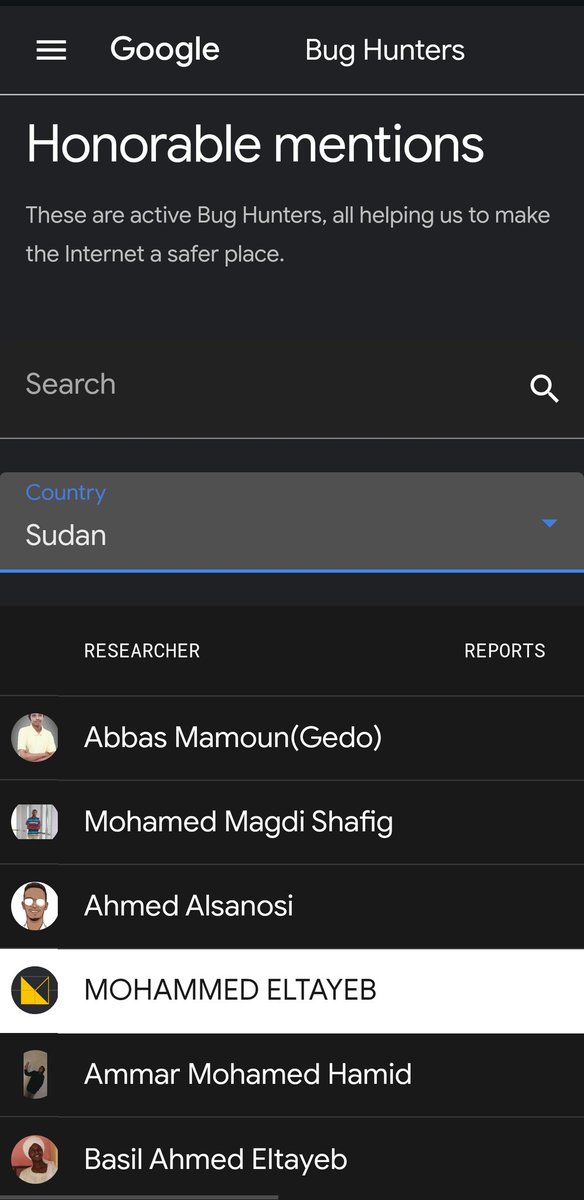
Thrilled to be added to Google’s Honorable Mentions after finding a couple of bugs! It was a great new experience for me. Big thanks to Google VRP (Google Bug Hunters) team for the recognition. #BugBounty #bugbountytips