WILHELM SVENSON.DEFI ♻️
@wsvenson_defi
CRYPTO BLOCKCHAIN RECOVERY Experts 💻🕹️ System and Networks Administrator with Personalized services for conscientious Work, Scam Refunds IT & IC3 Security.
ID: 1542895988888707074
https://t.me/CYPHER_KEVMITNICK 01-07-2022 15:40:54
65,65K Tweet
8,8K Followers
7 Following


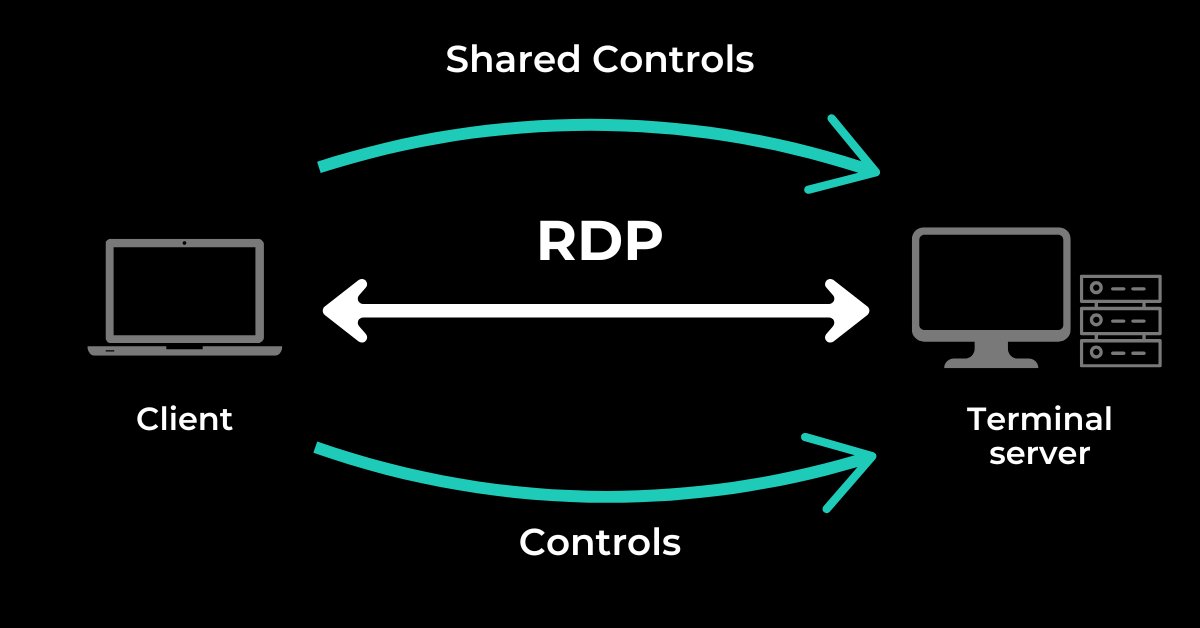
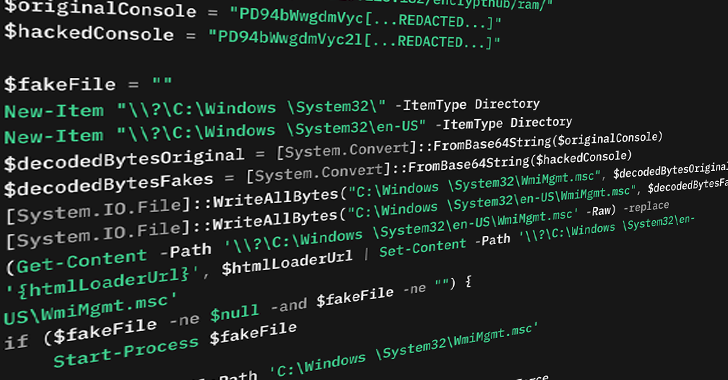
Cybercriminals are leveraging fake CAPTCHA images in phishing PDFs to distribute the dangerous Lumma Stealer malware. 260 unique domains and 5,000 phishing PDFs, mostly hosted on Webflow, are part of this ongoing campaign. Learn more about the tactics: thehackernews.com/2025/02/5000-p…








Easily my favorite Michael Saylor moment from the summit no one is talking about “Glad I’m wearing my orange tie” #Bitcoin



Kindly send me a message Carlos Mayans

Kindly dm privately Carlos Mayans