ULTRAFRAUD
@ultrafraud
Underground bon vivant hunting for #malware
ID: 1519011129896411136
26-04-2022 17:51:15
217 Tweet
1,1K Takipçi
30 Takip Edilen





Active #Doenerium stealer dressed up as AnyDesk Software 🏴☠️ /anydesks.co/en/downloads/AnyDesk.exe 229037ea33eb267cc08621c8967ab4022f811461f716592ae95be23a8191bfe6 C2 /doenerium.kqnfkpoccicxiudstqonfotuwsrhuxkwhqjjfsbjhonoubrccy.nl




Another great analysis from Bridewell BridewellCTI 💣 Thank you guys Joshua Penny Yashraj Solanki for credits. #EasyStealer








Interesting loader disguised as CreateStudio Pro, dropping an obfuscated Python payload via PythonAnywhere 🐳 /download-createstudioo.com /kingkh.pythonanywhere.com ↪️/kingkh.pythonanywhere.com/SRC/test.zip




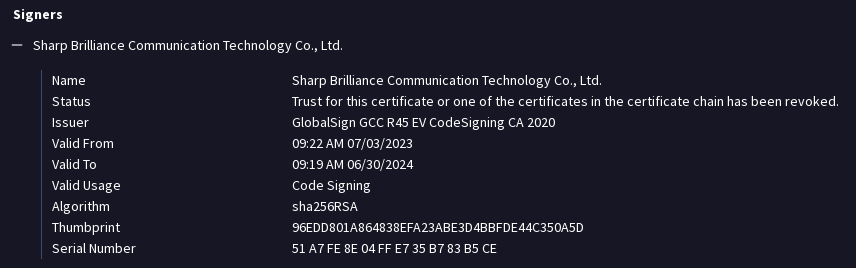
#100DaysofYARA Day83: Suspicious files attempting to impersonate Google Update Utilities github.com/RustyNoob-619/… Thanks to ULTRAFRAUD for sharing the signed malware sample which allowed me to build this YARA



![Germán Fernández (@1zrr4h) on Twitter photo Watch out for this #DarkGate campaign, quite possibly through Malvertising and using signed MSI files with very low (or zero) detection.
#SIGNED "PFO GROUP LLC"
Other sites on 154.56.47.156:
https://openvpnhub[.]com/
https://angryipscanner[.]net/
https://www.putty-ssh[.]com/ Watch out for this #DarkGate campaign, quite possibly through Malvertising and using signed MSI files with very low (or zero) detection.
#SIGNED "PFO GROUP LLC"
Other sites on 154.56.47.156:
https://openvpnhub[.]com/
https://angryipscanner[.]net/
https://www.putty-ssh[.]com/](https://pbs.twimg.com/media/F5-Hzu6XsAA2qmQ.jpg)