Thomas Segura
@thomassegura13
Tech Content Writer
Clojure lover - unleash the power of the λ 🪄 🧙
ID: 1404808511146627083
15-06-2021 14:30:31
130 Tweet
75 Followers
433 Following

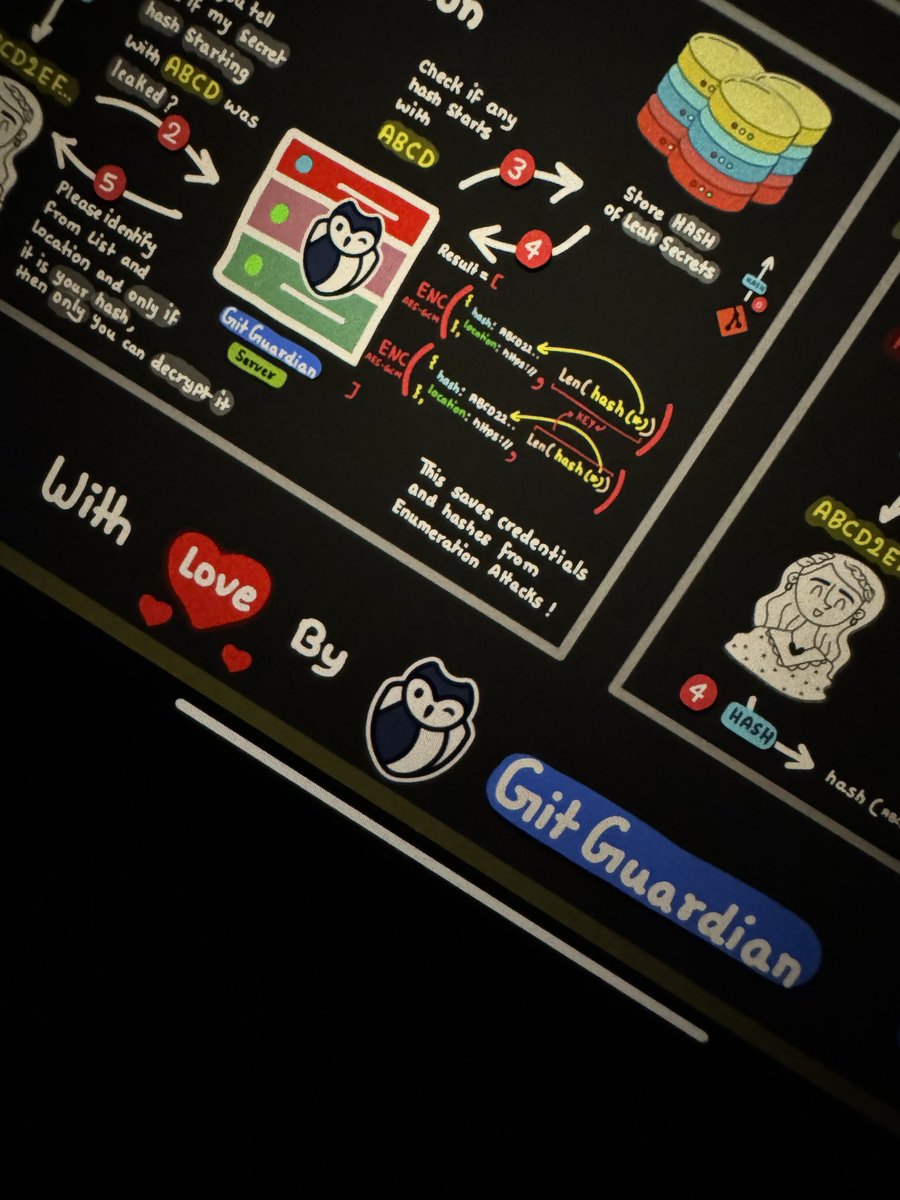
New one coming and that is in collaboration with GitGuardian I hope you all will like it !! 🤟🏻🫶✌🏻



Les craintes concernant le Cyber Resilience Act de l'UE sont-elles justifiées ? Une tribune proposée par Thomas Segura, spécialiste cybersécurité de GitGuardian. 👇 maddyness.com/2024/02/12/les…

Really good analysis by Thomas Segura & @[email protected] Dwayne McDaniel of GitGuardian on how stolen @Okta authentication tokens led to the Cloudflare breach. Breach illustrates the threat of secrets sprawl: sensitive data spread across many platforms w/o adequate #infosec. cybersec.gitguardian.com/s/the-secret-s…



Nearly 2 out of 3 AWS organizations are still using long-lived credentials for authentication in their CI/CD pipelines. Read Datadog, Inc.’s DevSecOps study to learn more: datadoghq.com/report/facts/s…




Préoccupations de #sécurité et de #confidentialité de #GitHub #Copilot : comprendre les risques et les meilleures pratiques itsocial.fr/cyber-securite… Thomas Segura GitGuardian


Book I co-authored for GitGuardian is here!

COMPUTER WEEKLY GitGuardian gives 'voice' to AppSec on hard-coded secrets computerweekly.com/blog/CW-Develo… ComputerWeekly GitGuardian