Paulos Yibelo
@paulosyibelo
security researcher, hacker, prev
@octagonnetworks , player @detectify🗺🦉/, I haxor everything I touch..
Disclaimer: I speak for my self
ID: 2843924471
https://www.paulosyibelo.com 25-10-2014 17:01:54
1,1K Tweet
5,5K Followers
394 Following



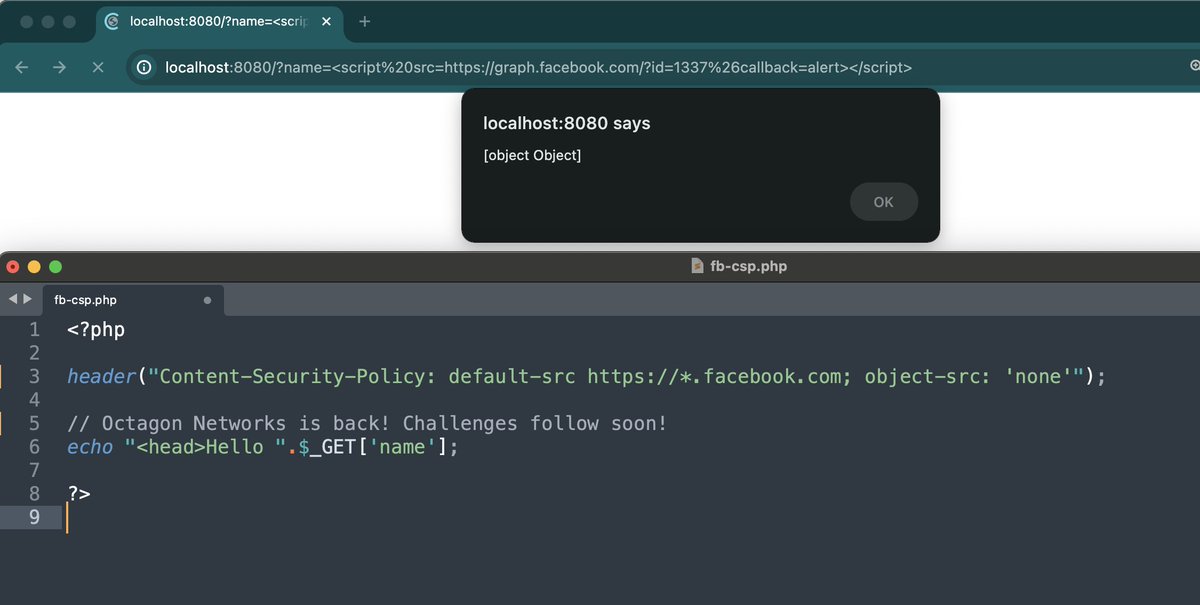
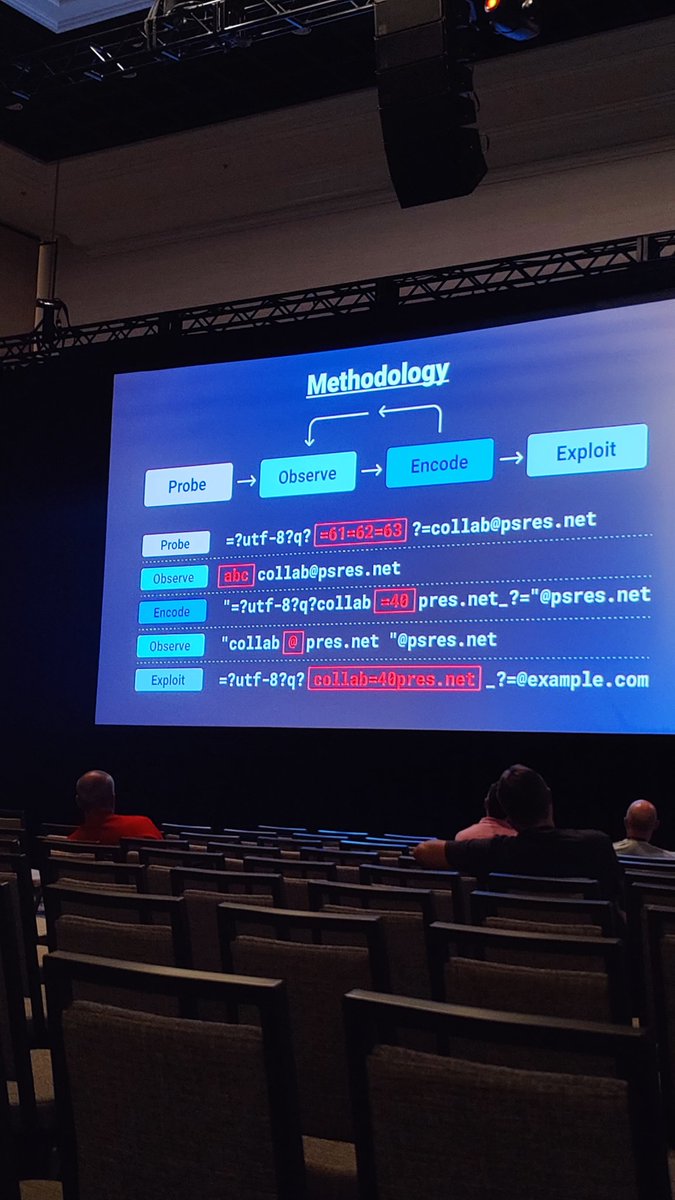
Can I just say Paulos Yibelo has been dropping some bangers lately. We'll mention them on the pod this upcoming Thursday, but both of these client-side techniques are really innovative and sick: paulosyibelo.com/2024/02/cross-… octagon.net/blog/2022/05/2…

Iconv, set the charset to RCE (part 2): Charles Fol exploits direct iconv() calls to hack the PHP engine, and its most popular webmail, @Roundcube (CVE-2024-2961). ambionics.io/blog/iconv-cve…


Introducing DoubleClickjacking 🧌: a widespread timing-based vulnerability class that slips between your first & second click — evading modern mitigations leading to account takeover vulnerabilities in almost all major websites. paulosyibelo.com/2024/12/double… #bugbountytips #infosec

Shoutout to Paulos Yibelo for this writeup and help him reach 0x38D7EA4C68000 followers on X. Read more 👉 s.mtrbio.com/zbpdwquyac




Inspired by Paulos Yibelo, I thought about what improvements I could make to trick users into pressing buttons that perform sensitive actions. Finding some vulnerable targets along the way! Read the details in my latest blog post below: jorianwoltjer.com/blog/p/hacking…

Double-Clickjacking, or "press buttons on other sites without preconditions". After seeing and experimenting with this technique for a while, I cooked up a variation that combines many small tricks and ends up being quite convincing. Here's a flexible PoC: jorianwoltjer.com/blog/p/hacking…