Brandon Dalton
@partyd0lphin
🌉 Senior macOS Researcher @CrowdStrike
ID: 633109376
https://swiftly-detecting.notion.site/ 11-07-2012 18:23:54
379 Tweet
850 Followers
184 Following





Thrilled to announce my new Project Zero blog post is LIVE! 🎉 I detail my knowledge-driven fuzzing process to find sandbox escape vulnerabilities in CoreAudio on MacOS. I'll talk about this and the exploitation process next week offensivecon! googleprojectzero.blogspot.com/2025/05/breaki…

You can the slides for my today’s BSidesBUD 🇭🇺 talk (Apple Disk-O Party) on my site: theevilbit.github.io/talks/



🔺iPhone models announced today include Memory Integrity Enforcement, the culmination of an unprecedented design and engineering effort that we believe represents the most significant upgrade to memory safety in the history of consumer operating systems. security.apple.com/blog/memory-in…


Excited to hear more at OBTS! Brandon Dalton :)


📦 UNBOXING: Next-Gen Mac Monitor — live at #OBTS 🍏 Brandon Dalton Brandon Dalton First look: smells like fresh ES events and SwiftUI gloss. 😮💨✨ Inside the box: •Plug-and-play access to Apple Endpoint Security stream (no agent spelunking) •Dynamic subscriptions, filters,

Brandon (Brandon Dalton) from @crowdstrike talked about many improvements and features in his most awesome opensource tool (Mac Monitor) - ( aka Procmon for OSX ) - & even pushed out version 2 in real-time at #OBTS! Check it out if you haven’t already! github.com/Brandon7CC/mac…

Christine christine 🌸💐🌺🌷🌹🪻🍃🌱🌿🪴✨ and JBO (Jonathan Bar Or (JBO) 🇮🇱🇺🇸🇺🇦🎗️ ) (& Alexia Wilson) from Microsoft showed #OBTS how Spotlight just got too bright. 😬 They found a macOS TCC bypass (#CVE-2025-31199) that abuses Spotlight to get your private data - locally and remotely - and showed how to detect!
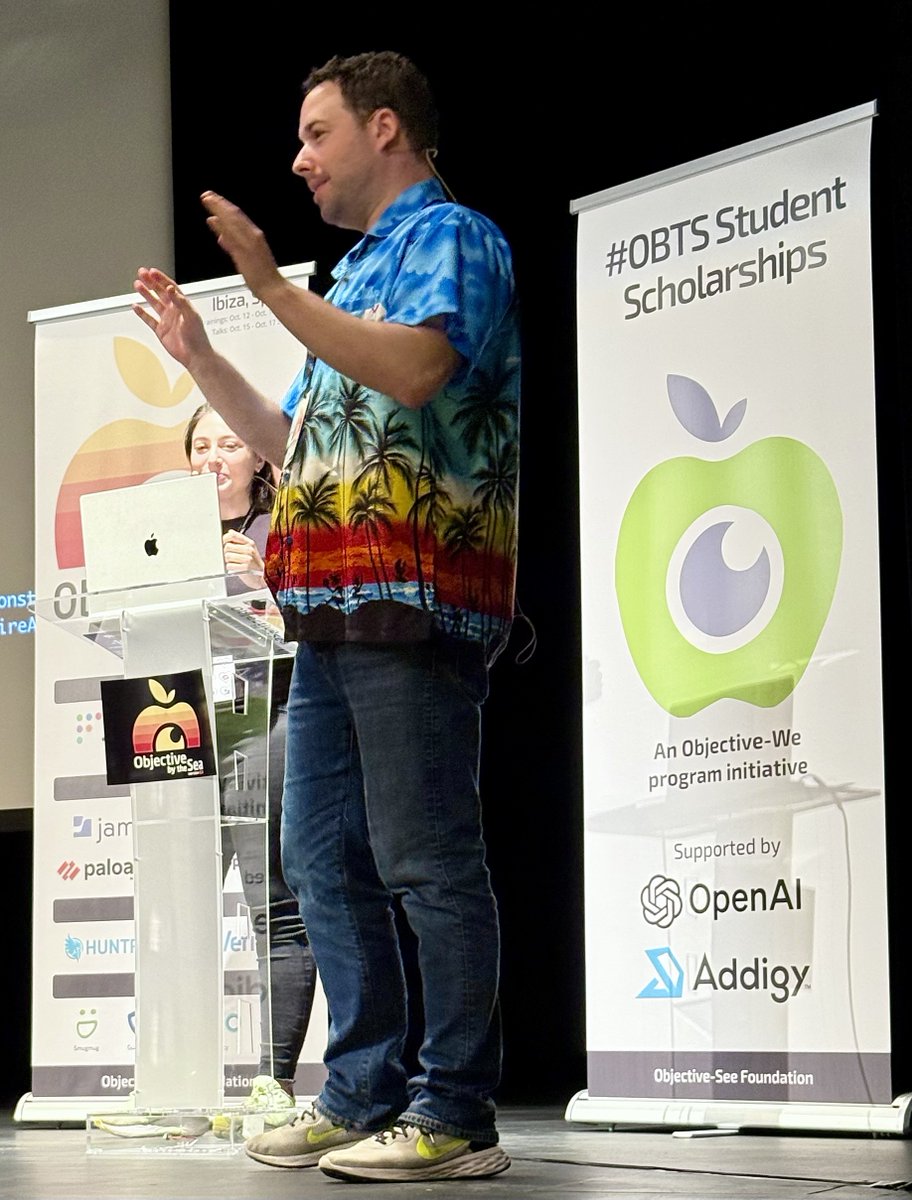

#OBTS v8 was so fun. Met many folks I interacted with in the past, and a lot of new folks, everyone very smart and passionate. Special thanks to Patrick Wardle for bringing the community together. 🍎