OSVDB
@osvdb
Open Sourced Vulnerability Database (OSVDB), now shuttered. Now random vulnerability-related Tweets and discussion.
ID: 19133882
http://osvdb.org/ 18-01-2009 02:50:05
5,5K Tweet
6,6K Takipçi
17 Takip Edilen





I wanted to fully test this “Responsible Disclosure” theory so I submitted a one click RCE in Microsoft Teams to #msrc on Sep 01, 2018. It is still open. The disclosure policy of Tavis Ormandy and others gets bugs fixed. This does not.


There's a "security.txt" proposal to IETF (the RFC ppl) for a robots.txt-like way for researchers to contact website owners about vulns. Comment needed ASAP, and anybody can comment via email! Personally I'm for security.txt (RFC 9116). Make vuln reporting easier! mailarchive.ietf.org/arch/msg/ietf-…





At Google Project Zero, the team spends a *lot* of time discussing and evaluating vulnerability disclosure policies and their consequences. It's a complex and controversial topic! Here's P0's policy changes for 2020 (with our rationale for the changes): googleprojectzero.blogspot.com/2020/01/policy…

Massive Oracle Patch Reverses Company's Trend Toward Fewer Flaws ow.ly/wGef50xYyFz by Rob Lemos (@roblemos just about everywhere) #Oracle #patching #vulnerabilities #software

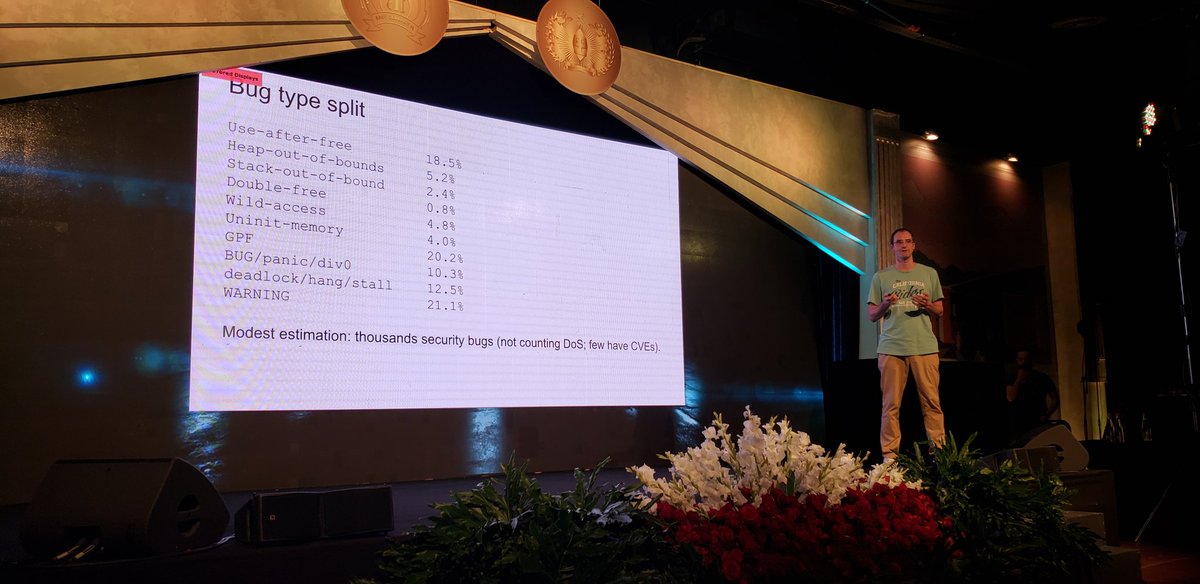
Dmitry Vyukov "modest estimation, syzkaller have found more than 1000 security vulnerabilities"