MatteoC
@MatteoC68006921
Webapp pentester from 3 years, bug bounty hunter. if you are a newbie, ask me whatever you want about offensive security. OSCP CRT CPSA
ID:1450791636670287873
20-10-2021 11:51:12
788 Tweets
194 Followers
771 Following


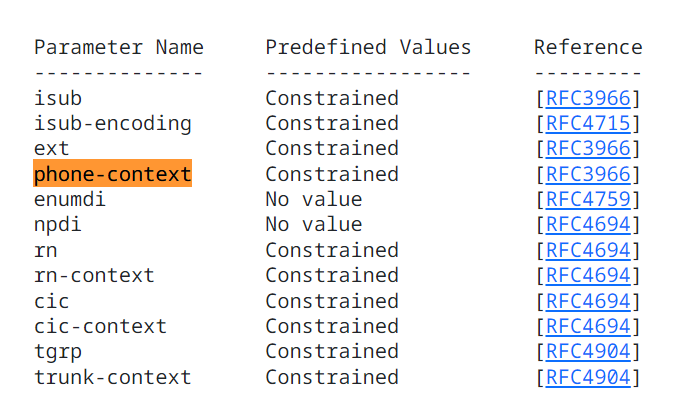
Inti De Ceukelaire Brute Logic Same for phone numbers, ;ext=, ;phone-context= etc are considered 'valid' parts of a phone number. :)
datatracker.ietf.org/doc/html/rfc53…

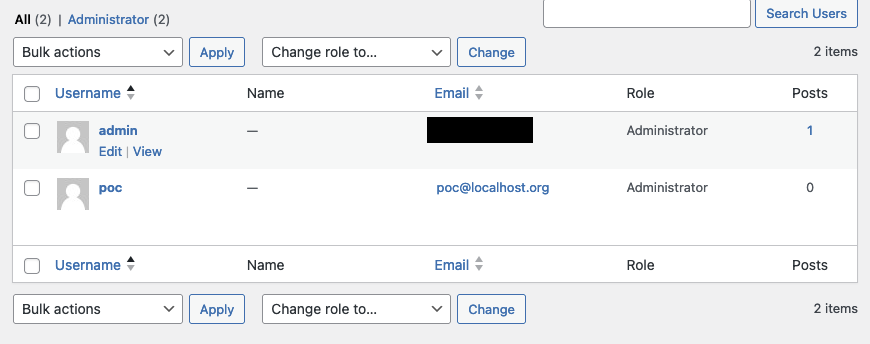
Today, I took a few minutes to analyze the #WordPress Automatic Plugin CVE-2024-27956 (Unauthenticated Arbitrary SQL Execution) #security #vulnerability . Turns out it is super easy to exploit.
Here is a basic PoC:
Since 'q' is passed directly into a $wpdb->get_results() call,…


Yay, I was awarded a $5,600 bounty on HackerOne! #TogetherWeHitHarder #bugbounty
🧵1/n So I found Admin Panel Takeover via Improper Authentication
Recon: Using Censys, I found an IP belonging to the org. I used masscan and discovered an unusual open port.



They just marked my submission as 'resolved', unluckily for them i can still reproduce the bug in the same way 🤔. They didn't ask for a retest, should i make a new submission and get another bounty or simply reply friendly to the same submission? #intigriti #BugBounty

CVE-2024-0333
Take a deep dive into CVE-2024-0333 explained by Malcolm Stagg, a Google Chrome vulnerability enabling malicious extension installation in the InfoSec Writeups 107th Weekly Newsletter!
weekly.infosecwriteups.com/iw-weekly-107/



IDOR + ATO Account Takeover via Reset Password
- a logged in area;
- intercept password change request;
- change username to another;
- if u have successfully changed user pass, u have an IDOR + ATO;
Impact: Critical
#bugbounty #bugbounty tips #bugbounty tip