Keysight ATI
@keysight_ati
Updates, news and commentary from Keysight's Application & Threat Intelligence team (formerly Ixia ATI)
ID: 14399906
http://www.ixiacom.com 15-04-2008 19:14:30
6,6K Tweet
3,3K Followers
2,2K Following



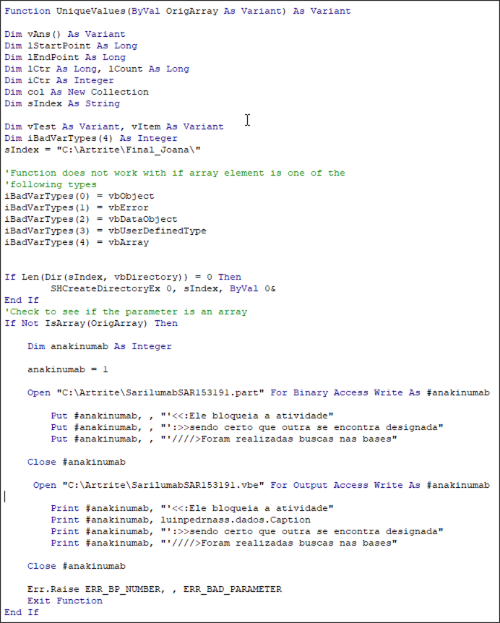
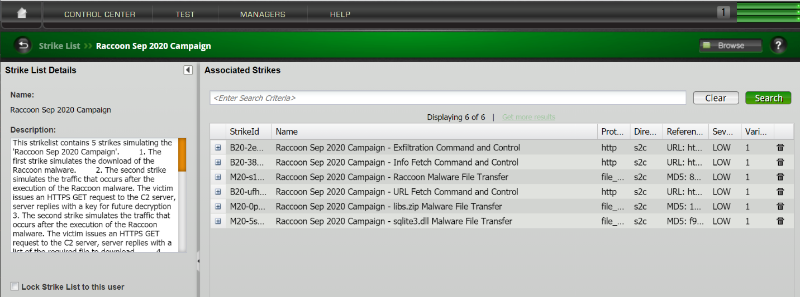
Raccoon #malware is designed to attack individual users and exfiltrate specific user info including host and browser info. The Keysight ATI team adds Raccoon malware kill chain to #BreakingPoint attack campaigns. Learn more: hubs.ly/H0y_CPC0 #NetworkSecurity #InfoSec
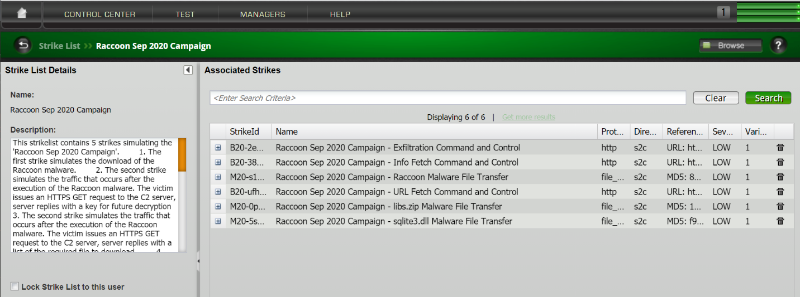
Raccoon #malware is designed to attack individual users and exfiltrate specific user info including host and browser info. The Keysight ATI team adds Raccoon malware kill chain to #BreakingPoint attack campaigns. Learn more: hubs.ly/H0y_DPP0 #NetworkSecurity #InfoSec






Ransomware never sleeps and one in particular -- #RUYK -- has been giving #HealthIT a headache. Keysight Network Visibility Test & Security Mike Hodge breaks down the troublesome #ransomware and discusses how you can determine if your firewall is protecting you in his new blog: bit.ly/35QDXoR




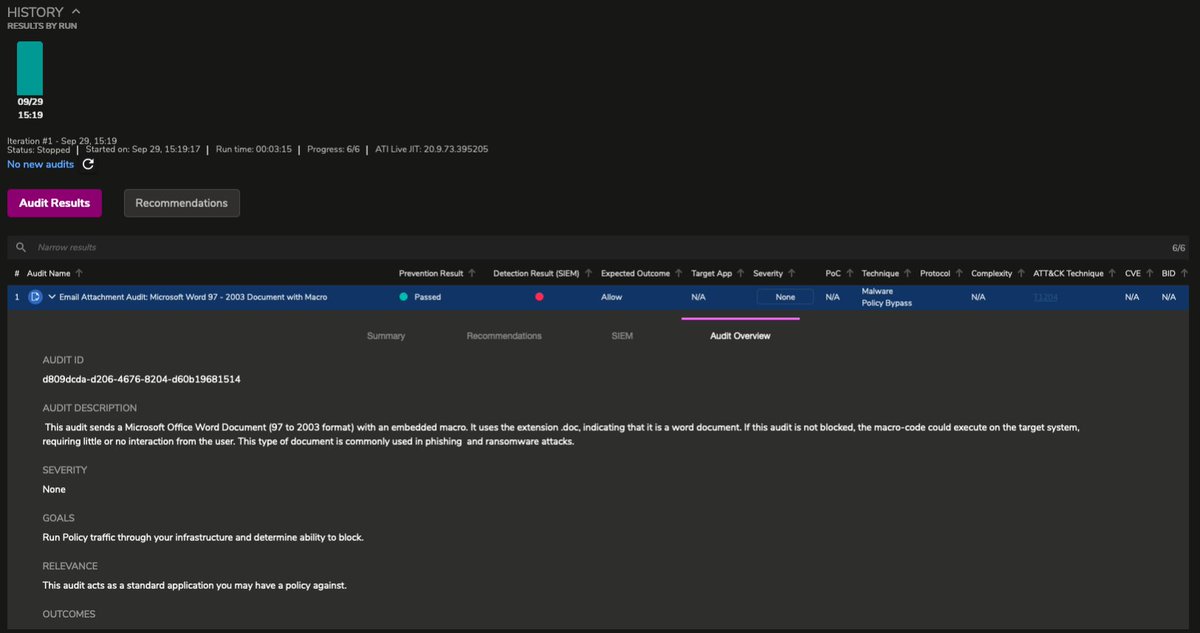
The impact of #FireEyeBreach may reach far beyond FireEye and its customers. Mike Hodge of Keysight Network Visibility Test & Security discusses the #CVE involved in the breach and how breach and attack simulation #BAS tools can help you find out if you’re vulnerable. bit.ly/2W3tmB9 #NetworkSecurity

The impact of #FireEyeBreach may reach far beyond FireEye and its customers. Mike Hodge of Keysight Network Visibility Test & Security discusses the #CVE involved in the breach and how breach and attack simulation #BAS tools can help you find out if you’re vulnerable. bit.ly/2W3tmB9 #NetworkSecurity


The impact of the #FireEyeHack and #SolarWindsHack reaches far and worldwide. Mike Hodge of Keysight Network Visibility Test & Security discusses how breach and attack simulation #BAS tools can help you discover if you may be vulnerable to hacks. bit.ly/2W3tmB9 #SecOps



The Keysight ATI team continues to follow the emerging story involving the #FireEyeHack and #SolarWindsHack. Chuck McAuley details how we’re updating our tools with #RedTeam testing and endpoint testing with #NJRat #Trickbot and #Sunburst bit.ly/3pgVoFO #SecOps

.Keysight Network Visibility Test & Security Releases Fourth Security Report Highlighting Three Critical Areas of Concern to #NetworkSecurity. Threats include #phishing trends due to #pandemic, #ransomware and critical security supply chain weaknesses bit.ly/3avFUZv