Jenny Jun
@jenny__jun
Assistant Professor, @NunnSchoolGT | Non-Resident Fellow, @CSETGeorgetown | @ColumbiaPoliSci PhD | Cyber conflict, AI, North Korea, IR | @Georgetown BS, SSP
ID: 1509180185773588480
http://jenny-jun.github.io 30-03-2022 14:46:31
30 Tweet
208 Followers
170 Following




🚨🚨 We are hiring a Deputy Director to help determine the direction of our research + carry out analysis and engagement on open source software, cloud and/or cyber safety. This position is housed in DC with the option for full-time remote work in the US. atlanticcouncil.org/job-opportunit…


For scholars studying cybersecurity: Center for Peace and Security Studies (cPASS) and the Cyber Escalation Lab at UCSD announced a Call for Papers for a two-day workshop titled "Cyber Escalation in Conflict: Bridging Policy, Data, and Theory." For more information, please visit: cpass.ucsd.edu/cyber/index.ht…

"Bob Jervis made important contributions to research on cyber conflict because he knew that, although it was fought using new kinds of tools, it was still conflict" Honored to share reminiscences & contributions from Bob Saltzman Institute of War and Peace Studies tnsr.org/roundtable/rem…



We had a lovely Columbia University Political Science cohort reunion yesterday after 2+ years. So good to see you all! Lily Yao Jenny Jun Norashiqin Toh @adamparkernyc Daniel Thomas Noah Zucker


🚨🚨 JOB ALERT 🚨🚨 The Atlantic Council's Cyber Statecraft is looking for an Associate Director to help drive the team's research agenda and carry out vigorous analysis and external engagement, focusing on the cybersecurity of digital systems. atlanticcouncil.org/job-opportunit…





Today, Natalia Slavney and I published new research on the penetration of cellphones in North Korea. Using data from the 38 North Digital Atlas, we came up with a coverage map of the network based on over 1,000 identified base stations. (1/3) (map by Ryan Kleissler)




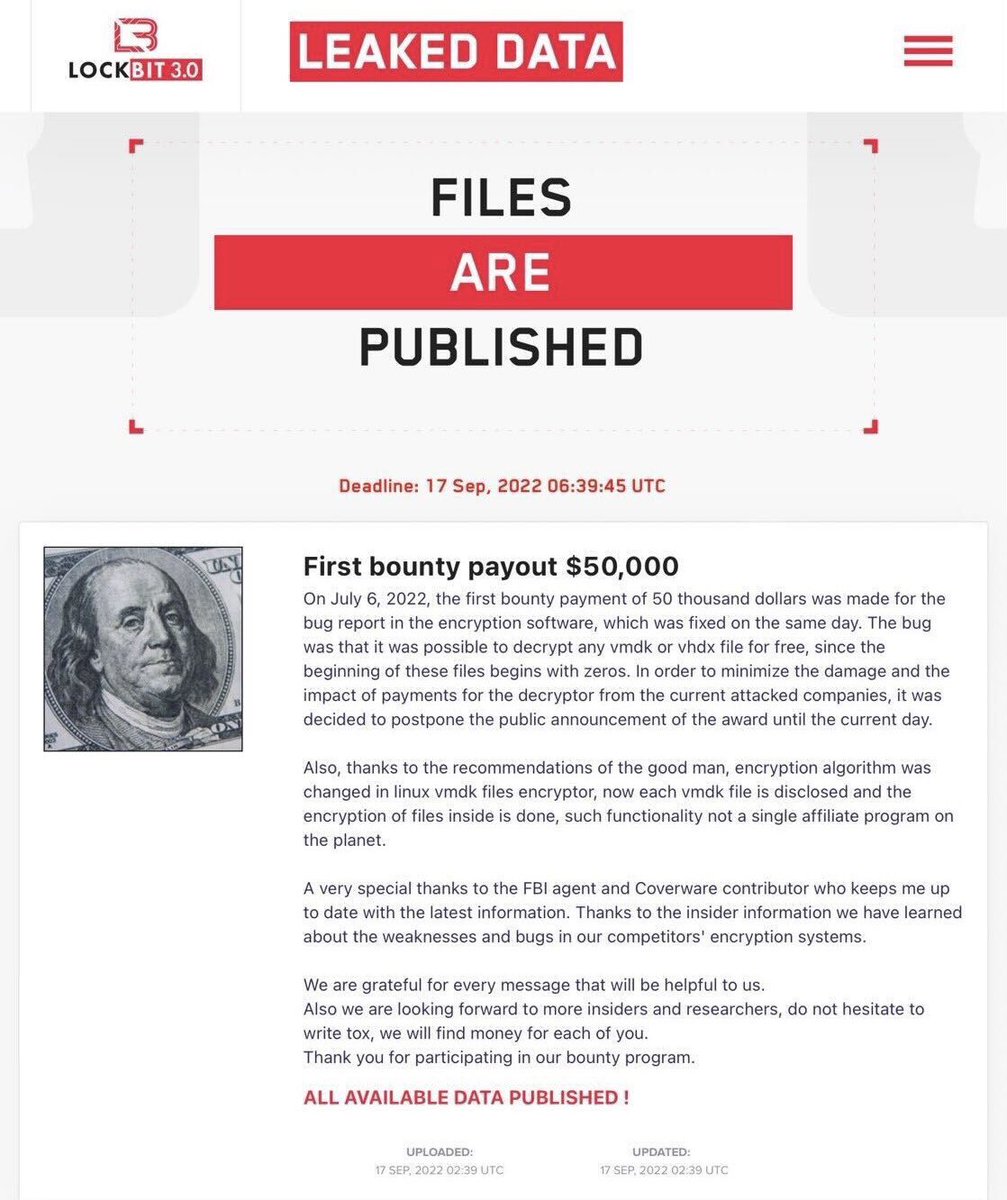
![Seongsu Park (@unpacker) on Twitter photo [Securelist] A comprehensive report on common TTPs of modern ransomware groups came out! It contains technical details, attribution, and Sigma rules. Highly recommend reading it:
securelist.com/modern-ransomw… [Securelist] A comprehensive report on common TTPs of modern ransomware groups came out! It contains technical details, attribution, and Sigma rules. Highly recommend reading it:
securelist.com/modern-ransomw…](https://pbs.twimg.com/media/FV-gipSVEAE177N.jpg)