ThreatHuntersForge
@huntersforge
Data Science, Threat Hunting & Open Source Projects 🍻 Founders: @Cyb3rward0g @Cyb3rPandaH
ID: 1177375313589940224
27-09-2019 00:12:09
21 Tweet
1,1K Followers
2 Following
Feel free to join the ThreatHuntersForge public slack 🤗💜 and let's continue building and empowering our community TOGETHER!! #ThreatHunting Roberto Rodriguez 🇵🇪 launchpass.com/threathunting 🏹⚔️🍻💜


Every time I think of something new I need I discover ThreatHuntersForge has it! #ATTACKcon


Jose Rodriguez 🇵🇪 & I had so much fun ATT&CK #ATTACKcon sharing our research w/ Project Jupyter notebooks , Binder Team , ThreatHunter-Playbook ⚔️ & @Mordor_Project #ThreatHunting Talk: youtube.com/watch?v=L3KxKA… Slides: speakerdeck.com/cyb3rward0g/re… BinderHub Demo: youtu.be/mQZFHbnDH4A

I always wondered how I could share #ThreatHunting detections via Project Jupyter notebooks in a more practical and interactive way so that anyone in 🌎 can reproduce the research! Thx to Binder Team 💜 ThreatHunter-Playbook @Mordor_Project it is now possible medium.com/threat-hunters…


I decided to write a book 😅! An online Interactive Book 💥! A book on the top of ThreatHunter-Playbook , Project Jupyter #notebooks and w/ Binder Team BinderHub links all put together w/ the amazing Jupyter Book project! #ThreatHunting Merry Christmas 🎄🎁 🍻 medium.com/threat-hunters…

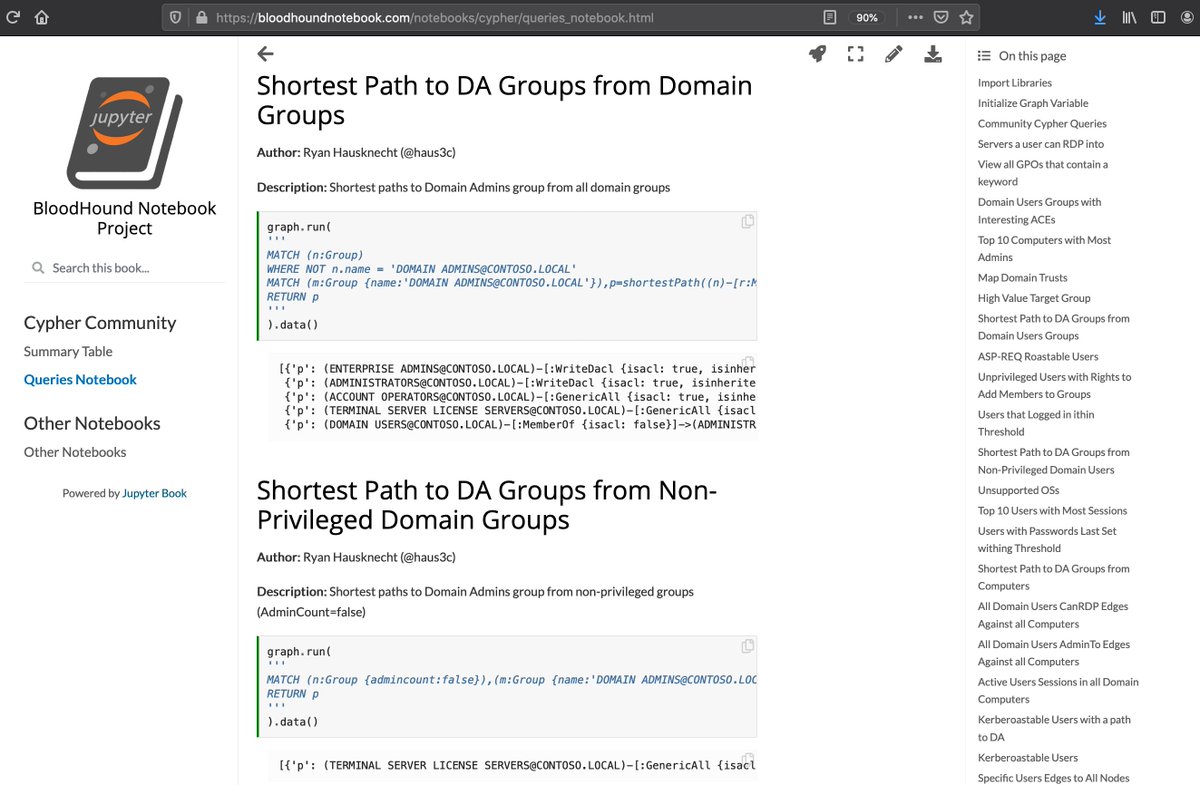
Looking for anything to do while you wait for 2020 🎉? I just created a Jupyter Book for the @Mordor_Project ! You can now explore mordor datasets w/ Project Jupyter #notebooks via BinderHub 🌎 Pre #ThreatHunting activities for 2020 🍻🤣! New Site: mordordatasets.com


Trying to revamp a project 🔥 & document interesting SACLs (Audit Rules) 😉 🍻 First attempt: 1) git clone github.com/GhostPack/Seat… 2) egrep -rhio '(SOFTWARE\\|SYSTEM\\).*\"' Seatbelt/Seatbelt/Commands/* 3) gist.github.com/Cyb3rWard0g/02… 4) github.com/OTRF/Set-Audit… (work in progress)

Thank you for sharing Adam Chester 🏴☠️ 💜 I took some time in the 🌞 to read a little bit about it. I'm sure there are + resources out there, but I put together these initial notes from a detection perspective. Maybe a SACL & sigma rules for the reg approach? 😈gist.github.com/Cyb3rWard0g/a4…


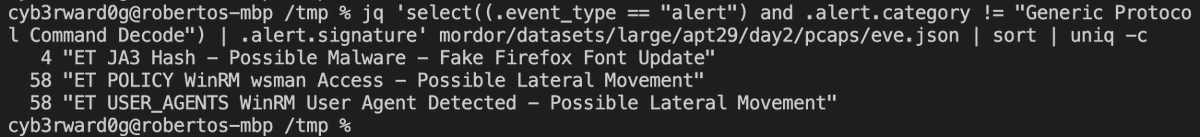
WE HAVE PCAPs 😈 a) Suricata IDS/IPS ➕ ET Rules! b) git clone github.com/hunters-forge/… && cd mordor/datasets/large c) find apt29/day*/pcaps -name '*.zip' -execdir unzip -P infected {} \; c) find apt29/day*/pcaps -name '*cap' -execdir suricata -r {} -k none \; TY Jason Trost 🙏


I started to document Win RPC interfaces & their respective methods 📋& ended up using sigpwn for the 1st time, integrating code from Adam Chester 🏴☠️ & @Sektor7Net research 😅 and using Project Jupyter notebooks & #GraphFrames 🔗 to analyze the results 🍻 medium.com/threat-hunters…

HOW to contribute a @Mordor_Project dataset in 2 mins ⏳w/ the help of Red Canary, a Zscaler company ART & then contribute to sigma after exploring the data! Open Threat Research ♻️ Clear, Exec & Collect: youtu.be/6iteEfbuwU8 😈 Data: mordordatasets.com/notebooks/smal… 🏹 Rule: github.com/OTRF/sigma/blo…