DevSec Hardening FW
@devsecio
Security & DevOps
ID: 2993066051
http://dev-sec.io 22-01-2015 21:50:01
144 Tweet
796 Followers
34 Following



Chad Loder @yaylinux InSpec and Chef are free for non-profit orgs and you can get some free scanning and remediation content for it from DevSec Hardening FW Happy to provide links and info if this is of interest

chef-ssh-hardening 2.8.0 is released github.com/dev-sec/chef-s… DevSec Hardening FW

Nick Hutton Progress Chef Open Policy Agent Red Hat Ansible Mark Phillips DevSec Hardening FW has a bunch of templates already that can be used off the shelf to Check compliance and apply the hardening.

Help us to improve our open source #security automation! We participate in Hacktoberfest with our Red Hat Ansible Progress Chef Shadow Puppet and #inspec projects. See dev-sec.io/blog/2019-10-0… for more details.


Teaching #DevOps best practices and supporting tools. 🦊 GitLab Test Kitchen DevSec Hardening FW Red Hat Ansible Progress Chef Perforce Puppet cinc HashiCorp, an IBM Company


chef-ssh-hardening v2.9.0 with EL 8 support is released github.com/dev-sec/chef-s… DevSec Hardening FW

Erlauben Eure AWS Security Groups den uneingeschränkten SSH Zugriff? Testen bitte! centrias.de/blog/security-… #inspec #aws /cc Christoph Hartmann & DevSec Hardening FW



Watch Michée Lengronne talk about #devsecops! It covers vault, ansible and our devsec automation. twitch.tv/videos/7692367… 🇫🇷


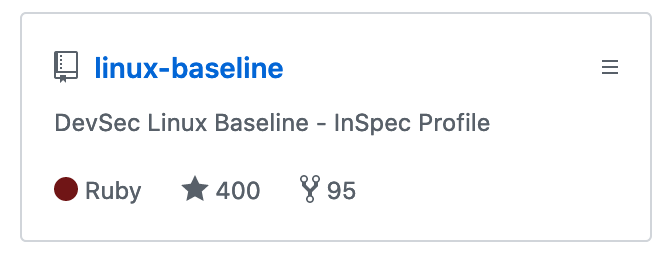
Because Progress Chef #Inspec changed 'attribute' for 'input', we modified DevSec Hardening FW profiles accordingly. Tell us if it breaks your builds. github.com/dev-sec/cis-di… github.com/dev-sec/linux-… github.com/dev-sec/ssh-ba… github.com/dev-sec/cis-ku…

As announced yesterday, every DevSec Hardening FW Progress Chef #Inspec profiles migrated from `attribute` to `input` dropping support for Inspec v3 github.com/dev-sec