Defimon Alerts
@defimonalerts
Real-time security alerts for DeFi
⚠️ Alerts: t.me/defimon_alerts
💎 Signals: t.me/+m9BMRKlMuW5iM…
ID: 1981269826497892352
http://defimon.xyz 23-10-2025 08:01:59
170 Tweet
508 Followers
7 Following







🚨 Singularity Finance - Loss ~$413K (2026-04-26) Type: Oracle Misconfiguration / Share Inflation The dynBaseUSDCv3 vault on Base prices its non-USDC reserves via UniswapV3Oracle. On 2026-01-19 the protocol admin registered the six yield-token oracle routes with a Uniswap V3 fee








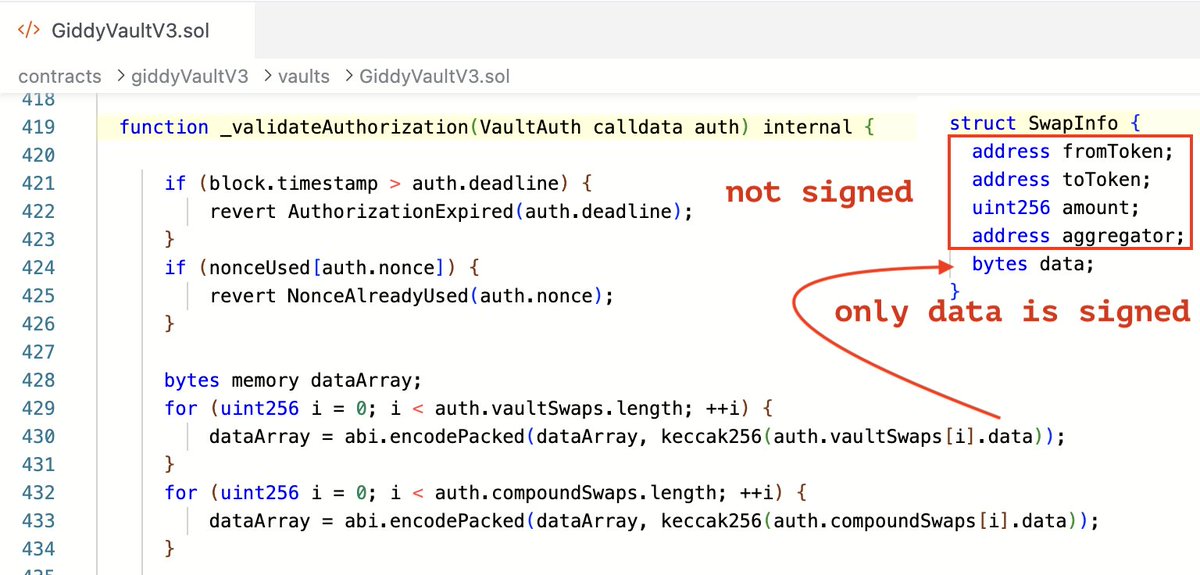
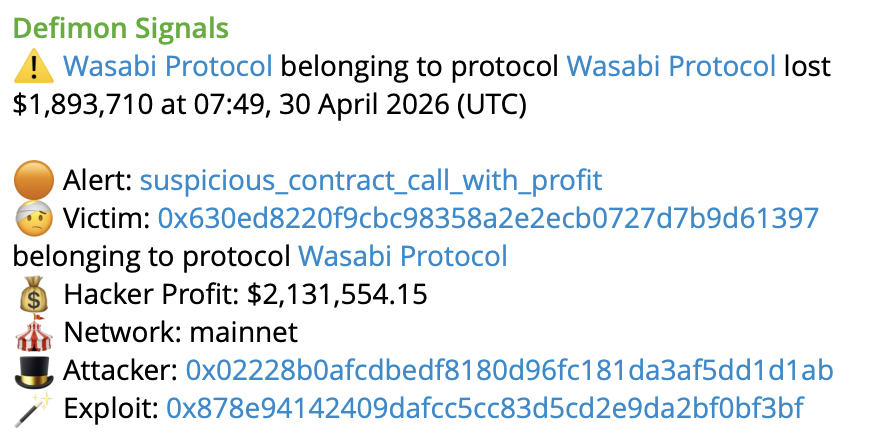
🚨 Wasabi Protocol 🟢 - Loss $4.5M (2026-04-30) Type: Compromised Admin Key The protocol admin EOA granted ADMIN_ROLE to the attacker's exploit contract which suggests a compromised private key. In the first drain tx the attacker called strategyDeposit() on 7 Wasabi vaults



We've just returned to Wasabi Protocol 🟢 around 8000$ rescued in various tokens from the recent incident. In the course of the attack a WasabiLongPool contract on Base was upgraded by the malicious actor to drain the funds. After the implementation was upgraded our AI whitehat