Paolo Caminati
@caminatipaolo
OSEP | OSWE | OSCP | CRTO | eCPPT | eWPT
ID: 1160894634563973121
12-08-2019 12:43:44
128 Tweet
37 Followers
328 Following

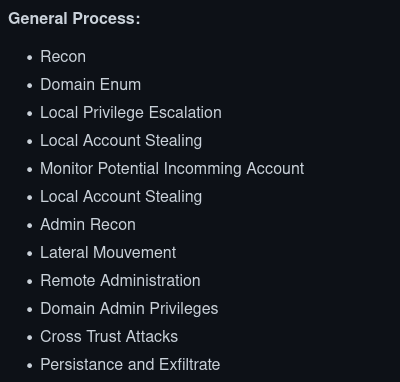
You know what time it is? ⏰It's Active Directory o'clock! I updated my AD Exploitation Cheat Sheet based on (among others) techniques discussed in the CRTO course. New: DPAPI & GPO Abuse Improved: LAPS, AppLocker/CLM, PowerView/Rubeus refs, many more 👇 casvancooten.com/posts/2020/11/…

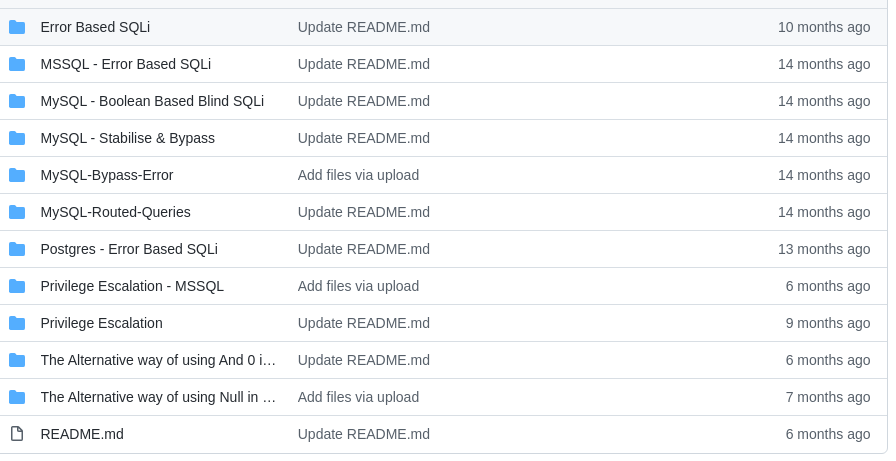
Active Directory Cheat Sheet:- github.com/fuzz-security/… Credit :- Emad Shanab - أبو عبد الله #HackENews #bugbounty #bugbountytips #cybersecurity #infosec



▶ Microsoft #ADCS - Abusing #PKI in Active Directory environment ◀ I've been bragging about it for months, this is the result of many weeks of work on lesser known compromise paths for #pentest by using enterprise PKI. Feedback is highly appreciated! riskinsight-wavestone.com/en/2021/06/mic…






Zero to Hero guide for Azure Device Code Phishing for Red Team engagements! Covers everything from creating a malicious Azure phishing infrastructure to achieving Azure Account Take-Over! Secrets to open OWA via Substrate! Credits: Steve Borosh Dr. Nestori Syynimaa 0xboku.com/2021/07/12/Art…


Yo, take a look at our blog at aptw.tf for the finest offensive cyber pasta recipes! With love and affection, your friendly neighborhood tortellini! Her0 Riccardo Mrsaighnal 0blio VincentDThe Electroxero Paolo Stagno (VoidSec) Paolo Caminati last



My write-up for the Blue Frost Security Windows Exploitation Challenge released during Ekoparty: voidsec.com/windows-exploi… Thanks Blue Frost Security for the challenge, I've enjoyed it very much



![David das Neves (@david_das_neves) on Twitter photo [Guide] AzureHound Cypher Cheatsheet
hausec.com/2020/11/23/azu…
[Repo] AzureHound
github.com/BloodHoundAD/A…
Docu: bloodhound.readthedocs.io/en/latest/data…
#PowerShell #MicrosoftAzure #BlueTeaming [Guide] AzureHound Cypher Cheatsheet
hausec.com/2020/11/23/azu…
[Repo] AzureHound
github.com/BloodHoundAD/A…
Docu: bloodhound.readthedocs.io/en/latest/data…
#PowerShell #MicrosoftAzure #BlueTeaming](https://pbs.twimg.com/media/E77bdroXIAQ8jV1.jpg)