Boston Cybernetics
@boscybernetics
Empowering People to Control Technology
ID: 900162779763666944
https://www.bostoncyber.org/ 23-08-2017 01:08:25
92 Tweet
546 Followers
1 Following

New to #Ghidra? Here's a detailed guide on Ghidra's primary components to help get you started with #reversing binaries. bit.ly/intro-ghidra Wanna dive deeper into Ghidra? Check out Jeremy Blackthorne & Evan Jensen interactive remote training at #Ringzer0 👏 bit.ly/ringzero-ghidra


Training ends so I spend 30 minutes hacking together part of what I learned for a proper sigpwn dark theme wrapping it all up tomorrow Boston Cybernetics Evan Jensen



The communications and devices that surround you are controlled by code, which was written by others. This is the new nature and we're all in it. You can be predator, you can be prey. eventbrite.com/e/vulnerabilit… Boston Cybernetics

.Boston Cybernetics is always trying to improve student efficiency. Here's a sample from our embedded class: a Jupyter Notebook attached to a remote Python kernel in IDA Pro to debug a MIPS binary with QEMU. We'll post the config and instructions to Github. Ilfak Guilfanov

Ever wanted to know how all those little gadgets work? How about how to hijack control of them? Train with us remotely at Infiltrate this October to learn reversing and exploitation on Linux and ARM. infiltratecon.com/conference/tra…

Ian is an expert in armchairs "Is it secure?" Always a fascinating question. Here's a high-level explanation and a more thorough discussion: Calculus of Cybersecurity: documentcloud.adobe.com/link/track?uri… Cyber Survivability Assessments: documentcloud.adobe.com/link/track?uri…


BCI will match your donation to Women In Security and Privacy (WISP). Pass it on: Trail of Bits RET2 Systems

Recorded video using Ghidra, Jupyter, and GDB to leak a stack canary, one lesson from the upcoming Modern Binary Exploitation, Jan 23 - 29 at ringzerø.training && @[email protected]. Details here: ringzer0.training/modern-binary-…. Video: youtu.be/Xt3eWaplMd0. Also my first YouTube upload, so thank god that's over.

Use preeny to start a suspended process, allowing a debugger to attach even when there's no natural breakpoints and use Jupyter with pwntools as an execution harness. Learn other useful techniques like these in Modern Binary Exploitation ringzer0.training/modern-binary-… ringzerø.training && @[email protected] [email protected]

What a week! I attended the Introduction to Reverse Engineering Class from Boston Cybernetics Institute Boston Cybernetics 😍 one of the sponsors of Day of Shecurity 😁 helping to get more #WomenInSTEM ! #infosec #cybersecurity #reverseengineering This is GOLD 🏆 RT for reach 🔥

I spent the most amazing week with smart women in Intro to Reverse Engineering sponsored by Boston Cybernetics and Day of Shecurity! Thanks to Jeremy Blackthorne for teaching such an awesome class! Learned new ways to break code! #codehegehogs

Women in security, join us! eventbrite.com/e/binary-rever… DM for password Day of Shecurity Boston Cybernetics CyberSN Secure Diversity #womenintech #CyberSecurity

@ women in tech Are you interested in binary reversing and exploitation? This is a FREE introductory class being offered March 7-March 11 by Boston Cybernetics. DM for pw. eventbrite.com/e/binary-rever…

Thanks to Boston Cybernetics and Day of Shecurity for a great class, Binary Reversing and Exploitation Course! Kayla0x41 is an amazing instructor! #womenincybersecurity #womenwhoreverse #reverseengineering


Come to REcon 2023 in Montreal and learn Reversing With GHIDRA with Jeremy Blackthorne recon.cx/2023/trainingr… #ghidra #recon2023 #CyberSecurity



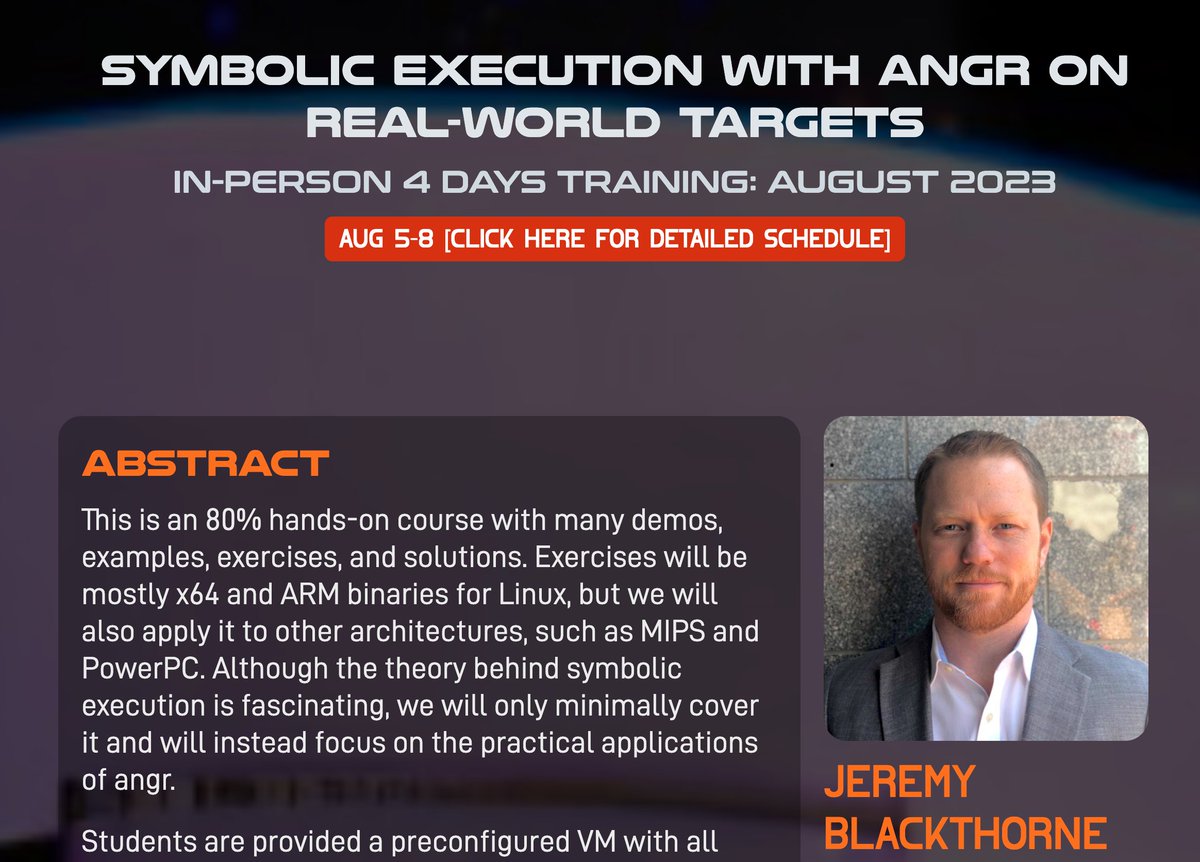
Have you still been putting off learning symbolic execution? Come to my training in Vegas. I'll get you started. ringzer0.training/trainings/symb… ringzerø.training && @[email protected] U.S. Cyber Command RPISEC