5BC
@5bcctf
ID: 1056977842385358848
29-10-2018 18:35:30
22 Tweet
150 Followers
4 Following










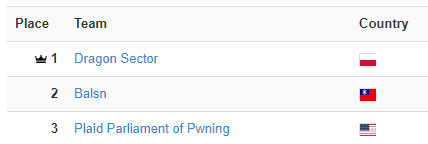
2nd time at the 2nd place at #GoogleCTF, an honor, thank you Google VRP (Google Bug Hunters) for another awesome CTF, see you next year.

Congratulations to # ./pasten and thank you again Google VRP (Google Bug Hunters)

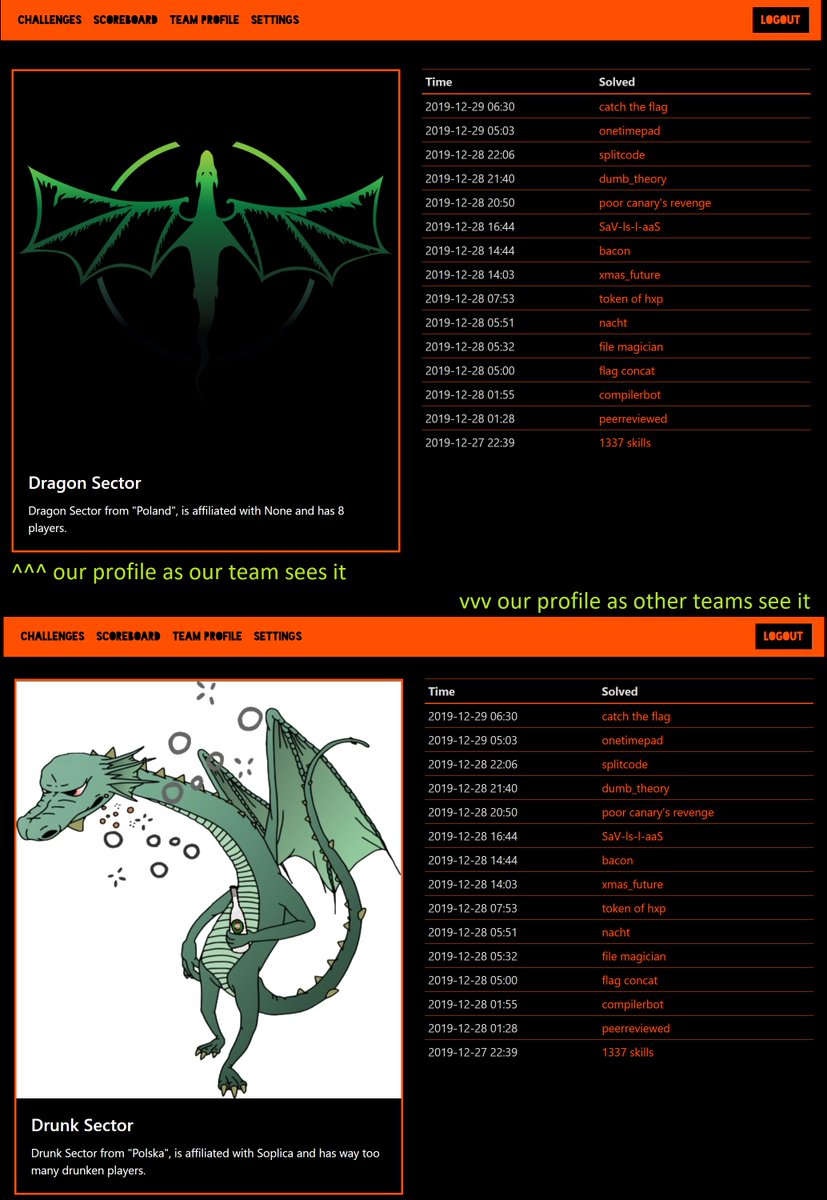
<Yves Hauser> congrats to Drunk Sector for finding out about their team name only 40 hours into the competition! I don't even 🤣🤣🤣 #TrolledAtCCCCTF #IDontEven #Potatos






What an honor, 2 of our best giving an awesome talk about #fuzzing at the amazing BlueHat IL conference