3ll137thy
@3ll137thy
ID: 1238005226407366657
12-03-2020 07:34:05
196 Tweet
11 Followers
213 Following





If you're into OSINT, Kase Scenarios is releasing Project Sandshark on March 27th! I had the opportunity to beta test Sandshark and earn their awesome badge! Project Sandshark is different from their other OSINT scenarios since it's 100% report based. You're given the






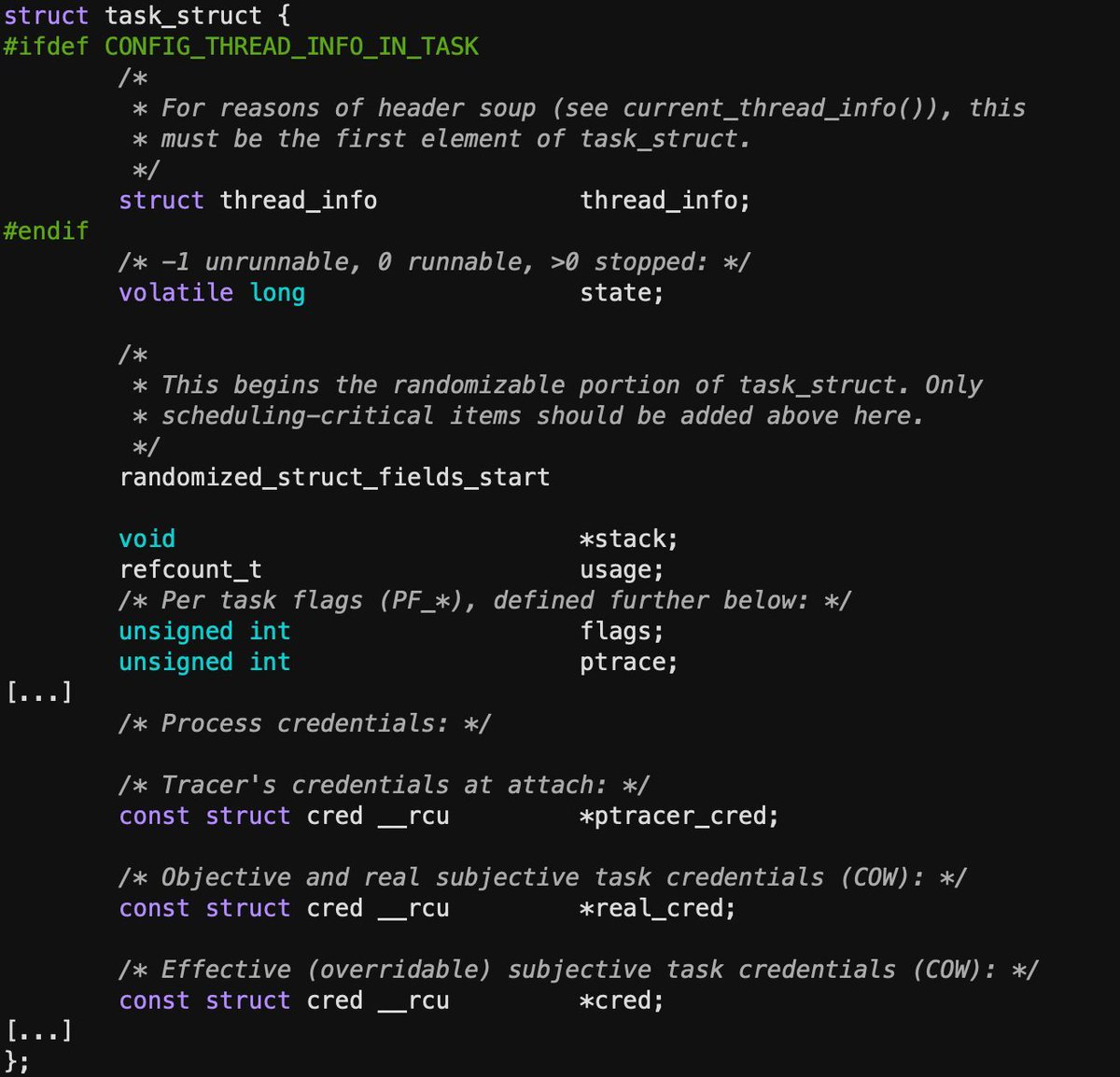
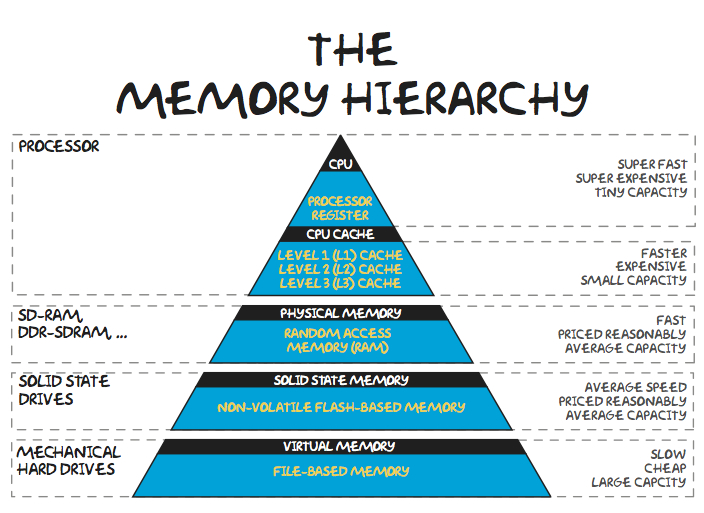
The tenth article (35 pages) of the Malware Analysis Series (MAS) is available on: exploitreversing.com/2025/01/15/mal… I would like to thank Ilfak Guilfanov Ilfak Guilfanov and Hex-Rays SA for their constant and uninterrupted support, which have helped me write these articles. I promised to write a