ivx 👾💀
@0xcrypto
Hobbyist by profession.
Mastodon: infosec.exchange/@0xcrypto
ID: 4654449558
https://eval.blog 26-12-2015 09:48:41
470 Tweet
253 Followers
252 Following


It's confirmed! Ken Gannon / 伊藤 剣 (@yogehi) of Mobile Hacking Lab, and Dimitrios Valsamaras (Dimitri Os) of Summoning Team (SummoningTeam) used five different bugs to exploit the #Samsung Galaxy S25. They earn $50,000 and 5 Master of Pwn points. #Pwn2Own


There's been a lot of valid outrage about #SancharSaathi. Will they pull back? Is it just a false promise? We don't know. Hence, I created a thread on removing apps like these & other bloatware from your devices. P.S. Donate to Internet Freedom Foundation (IFF)!








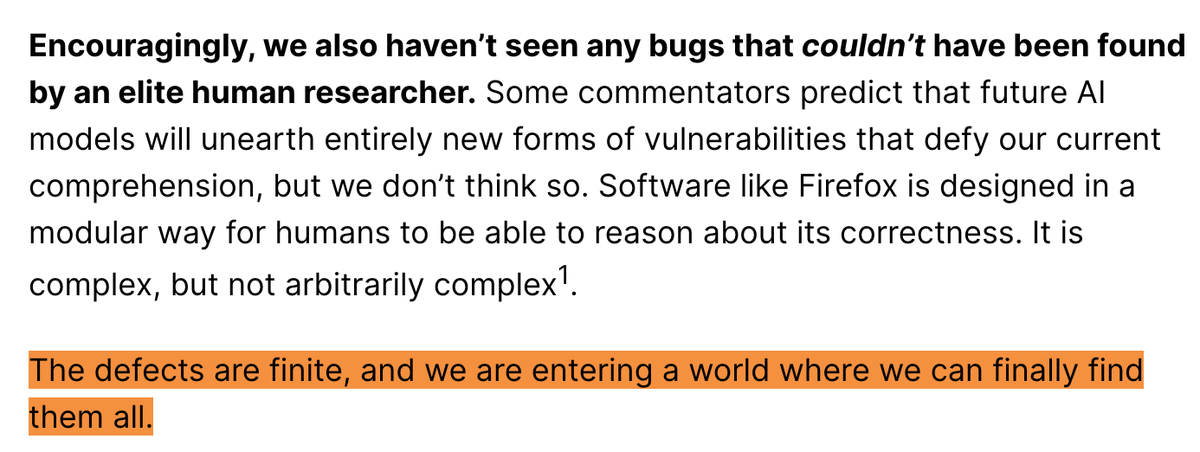
We tried to hook Promon Shield's native layer. 3 attempts. 3 crashes. Every hook detected in real time. So we stopped hooking and changed the data instead. Part 2 is live: djini.ai/a-look-at-a-pr… Shoutout to Ken Gannon (伊藤 剣) for the amazing research. All driven by AI. 🤖 #infosec