Paul MARTY
@0xpaulm
AppSec and bug bounty @doctolib
ID: 35809490
https://yeswehack.com/programs/doctolib-public-bug-bounty-program 27-04-2009 18:00:14
106 Tweet
384 Takipçi
3,3K Takip Edilen



💰 How to make cyber crime more profitable thaddeus e. grugq describes how FIN7's operational innovations (resources/personnel), not technical ones, made them more 💸 * Scaling your attacks across many targets * JIRA used to track victims * and more sec.okta.com/articles/2020/…



ReconNote - Modern target recon automation for bug-bounty hunters 🤩 github.com/0xdekster/Reco… - by Prasoon Gupta #AttackSurface #InfoSec #hacking #bugbounty #bugbountytips



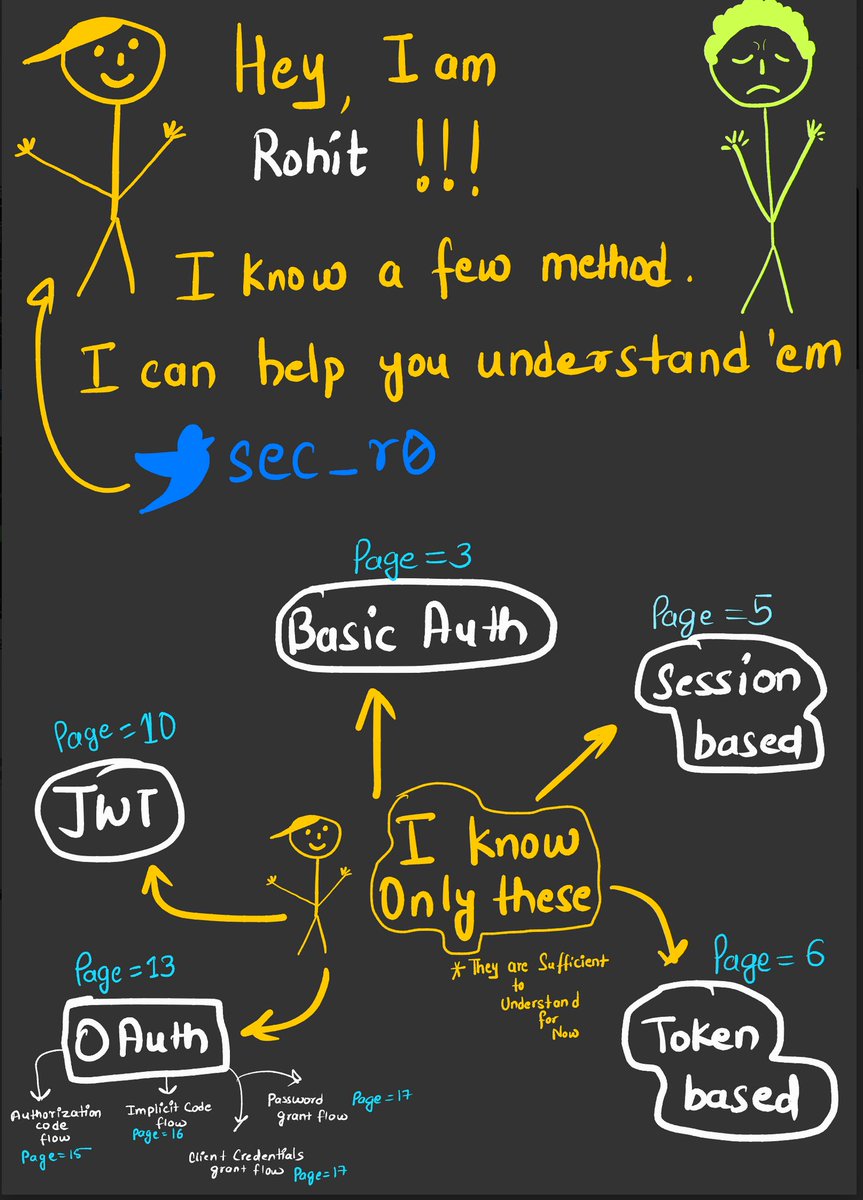
Biscuit, the foundation for your authorization systems clever-cloud.com/blog/engineeri… // This is the future of authentication and authorization at Clever Cloud and we open source everything around it :-)

In 2011, RSA was hacked by Chinese spies, who stole the "seed" values used to generate codes on SecurID 2fa tokens, shocking the security world. Now, after 10 years, the NDAs of the staff involved have expired. This is the untold story they shared with me: wired.com/story/the-full…





Have you noticed? Doctolib has doubled the max reward for its public #BugBounty program to €50K in October! Perfect timing to share our must-watch interview with CISO Cedric Voisin & Senior Product Security Engineer Paul MARTY on #Doctolib’s five-year Bug Bounty journey ⤵