
vikas@hacker-team
@00xneo
Cyber security deep learner
ID: 1582295405337149440
https://discord.gg/w4bXtaZubZ 18-10-2022 09:00:20
1,1K Tweet
59 Followers
1,1K Following


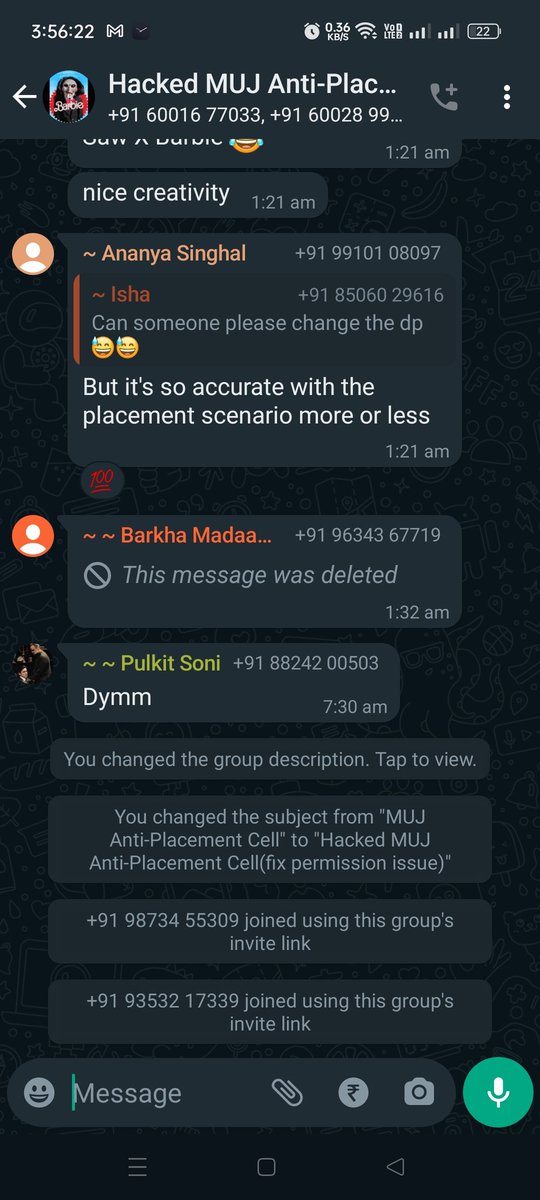
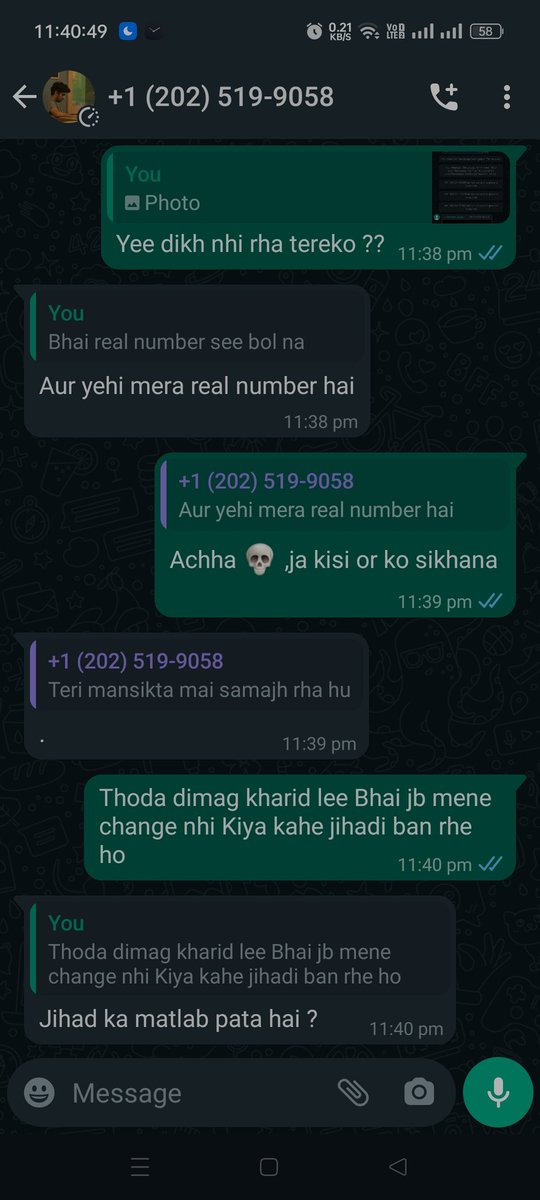
No one is safe in rajasthan fooling person's/people's spamming and acting as threat actor(just studens). Without any reason. Please look into the matter and take strict action else we need to take and you will be responsible Government of Rajasthan CMO Rajasthan Rajasthan Police








Google Dork - File Upload 📁 (site:example[.]com | site:example[.]org) & intext:"choose file” credit: Mike Takahashi #bugbountytips #BugBounty #bugbountytip #bugbounty
![RootMoksha Labs (@rootmoksha) on Twitter photo Google Dork - File Upload 📁
(site:example[.]com | site:example[.]org) & intext:"choose file”
credit: <a href="/TakSec/">Mike Takahashi</a>
#bugbountytips #BugBounty #bugbountytip #bugbounty Google Dork - File Upload 📁
(site:example[.]com | site:example[.]org) & intext:"choose file”
credit: <a href="/TakSec/">Mike Takahashi</a>
#bugbountytips #BugBounty #bugbountytip #bugbounty](https://pbs.twimg.com/media/GB4H7gCbQAAwXpc.jpg)




Dear airtel India Airtel Cares , Thanks for the amazing frustrating experience, thanks for the reminder at night after 9 pm



Request Smuggling ? Here are 10 blogs to learn more about them 1. medium.com/@StealthyBugs/… 2. infosecwriteups.com/exploiting-htt… 3. ricardoiramar.medium.com/the-powerful-h… 4. gupta-bless.medium.com/exploiting-htt… 5. medium.com/cyberverse/ear… 6. medium.com/@knownsec404te… 7. osintteam.blog/slip-in-unnoti… 8.



![Stephan Berger (@malmoeb) on Twitter photo We see a lot of threat actors in our Incident Response cases who disable or tamper with the local AV.
The website privacy.sexy has a copy & paste script to turn off most of Defenders features. [1] How many of these modifications (or deactivations) will trigger an We see a lot of threat actors in our Incident Response cases who disable or tamper with the local AV.
The website privacy.sexy has a copy & paste script to turn off most of Defenders features. [1] How many of these modifications (or deactivations) will trigger an](https://pbs.twimg.com/media/GC75J_uaAAI-w0O.jpg)

