🌃Zerophage🌌
@zerophage1337
Independent researcher focusing on threat intelligence and exploit kits. 😉
ID: 736664966980308992
https://zerophagemalware.com/ 28-05-2016 21:06:29
406 Tweet
3,3K Takipçi
339 Takip Edilen



Pretty cool #highjacker targeting Barclays Bank ; thanks to 🌃Zerophage🌌 for the vbs: 1st stage: app.any.run/tasks/97c94b9e… 2nd stage: app.any.run/tasks/4f6da57f… c2: casaconceitoltda[.]info
![James (@james_inthe_box) on Twitter photo Pretty cool #highjacker targeting <a href="/Barclays/">Barclays Bank</a> ; thanks to <a href="/Zerophage1337/">🌃Zerophage🌌</a> for the vbs:
1st stage:
app.any.run/tasks/97c94b9e…
2nd stage:
app.any.run/tasks/4f6da57f…
c2: casaconceitoltda[.]info Pretty cool #highjacker targeting <a href="/Barclays/">Barclays Bank</a> ; thanks to <a href="/Zerophage1337/">🌃Zerophage🌌</a> for the vbs:
1st stage:
app.any.run/tasks/97c94b9e…
2nd stage:
app.any.run/tasks/4f6da57f…
c2: casaconceitoltda[.]info](https://pbs.twimg.com/media/EShInTPUUAAeCjP.jpg)

⚠️#TA505 #malware as #COVID2019 #COVID19 #COVIDー19 ☣️ hxxp://www.0202.com.tw/~miki/9dwjrv/1mumq.html POST: hxxps://dysoool.]com/casemd Vitali Kremez KW AdamTheAnalyst stoerchl merlos JAMESWT_MHT Matteo Lodi Bl4ng3l #infosec #CyberSecurity #ThreatIntelligence
![reecDeep (@reecdeep) on Twitter photo ⚠️#TA505 #malware as #COVID2019 #COVID19 #COVIDー19 ☣️
hxxp://www.0202.com.tw/~miki/9dwjrv/1mumq.html
POST: hxxps://dysoool.]com/casemd
<a href="/VK_Intel/">Vitali Kremez</a> <a href="/Nzc2ZjZjNjY/">KW</a> <a href="/AdamTheAnalyst/">AdamTheAnalyst</a> <a href="/stoerchl/">stoerchl</a> <a href="/merlos1977/">merlos</a> <a href="/JAMESWT_MHT/">JAMESWT_MHT</a> <a href="/matte_lodi/">Matteo Lodi</a> <a href="/Bl4ng3l/">Bl4ng3l</a>
#infosec #CyberSecurity #ThreatIntelligence ⚠️#TA505 #malware as #COVID2019 #COVID19 #COVIDー19 ☣️
hxxp://www.0202.com.tw/~miki/9dwjrv/1mumq.html
POST: hxxps://dysoool.]com/casemd
<a href="/VK_Intel/">Vitali Kremez</a> <a href="/Nzc2ZjZjNjY/">KW</a> <a href="/AdamTheAnalyst/">AdamTheAnalyst</a> <a href="/stoerchl/">stoerchl</a> <a href="/merlos1977/">merlos</a> <a href="/JAMESWT_MHT/">JAMESWT_MHT</a> <a href="/matte_lodi/">Matteo Lodi</a> <a href="/Bl4ng3l/">Bl4ng3l</a>
#infosec #CyberSecurity #ThreatIntelligence](https://pbs.twimg.com/media/ESwLUaoXgAAYJqO.png)

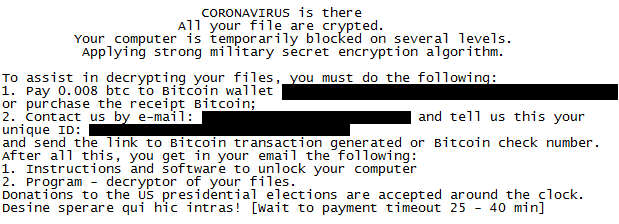
There's a Coronavirus themed ransomware, that actually encrypts. Encrypted files gets name: %email address%___%original filename & ext% Note: CoronaVirus.txt "Donations to the US presidential elections are accepted around the clock." 🤔 Michael Gillespie cc Vitali Kremez







2020-05-26:🎇I am beyond thrilled to 🗣️present on top-tier current #cybercrime group🇷🇺#TrickBot & state-sponsored for-profit #APT operations nexus🇰🇵#Lazarus @ personal favorite European conference 🇵🇱confidenceconf now online format "CONFidenceONline2020" confidence-conference.org/confi_online.h…


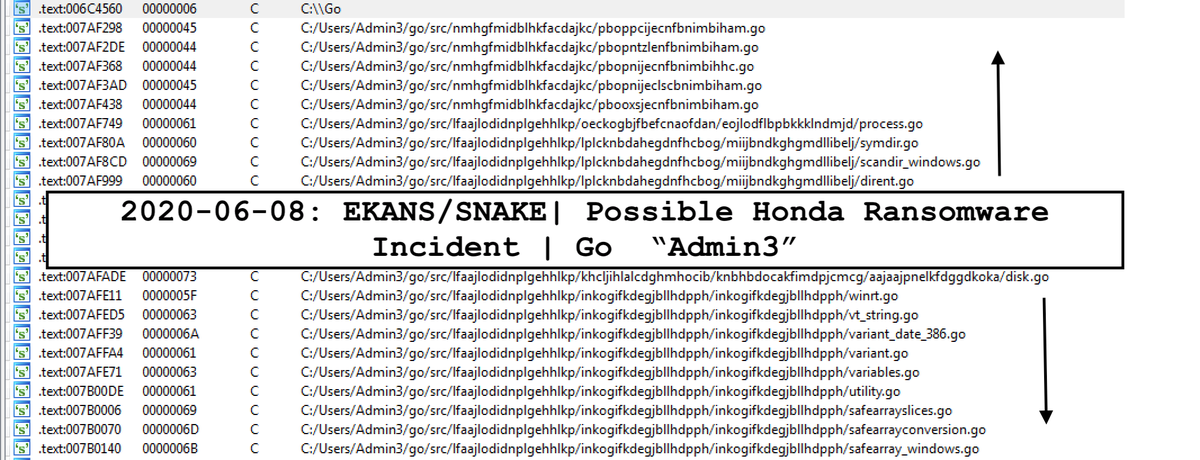
2020-06-08: 🆕🐍#SNAKE/#EKANS #Ransomware | Possible Honda Lockdown Incident RW References to Honda: 1⃣Honda ISP ("AHMC") 🇺🇸IP "170.108.71. 153" 2⃣"MDS. HONDA. COM" Check Source: C:/Users/Admin3/go/src/.../<RAND>.go MalwareHunterTeam BleepingComputer



2020-07-08:🎇[Exciting] Introducing VK Intel: Digital Forensics & Incident Response: "VK Intel: Digital Forensics & Incident Response" due to multiple requests & business demand😉 ✅Immediate & efficient incident response focusing on breaches & #ransomware Contact & file DFIR/malware ticket👇 vk-intel.com
![Vitali Kremez (@vk_intel) on Twitter photo 2020-07-08:🎇[Exciting] Introducing <a href="/vk_dfir/">VK Intel: Digital Forensics & Incident Response</a>: "VK Intel: Digital Forensics & Incident Response" due to multiple requests & business demand😉
✅Immediate & efficient incident response focusing on breaches & #ransomware
Contact & file DFIR/malware ticket👇
vk-intel.com 2020-07-08:🎇[Exciting] Introducing <a href="/vk_dfir/">VK Intel: Digital Forensics & Incident Response</a>: "VK Intel: Digital Forensics & Incident Response" due to multiple requests & business demand😉
✅Immediate & efficient incident response focusing on breaches & #ransomware
Contact & file DFIR/malware ticket👇
vk-intel.com](https://pbs.twimg.com/media/EcbeWQSX0AIWcrS.jpg)