B3ndik
@vmptrst
ID: 1641045068
02-08-2013 18:22:15
30 Tweet
110 Takipçi
492 Takip Edilen

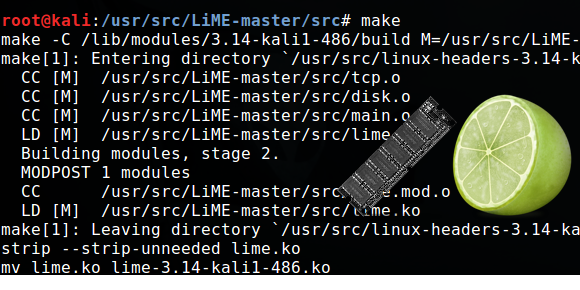
We found the full CARBANAK source code & previously unseen plugins. Our #FLARE team spent 500 hours analyzing the 100,000+ lines of code. 𝕸𝓎𝖐𝖎𝖑𝖑 ☠️ & James T. Bennett just dropped day 1 of their 4-part blog series: fireeye.com/blog/threat-re… Source code linked in blog. #CarbanakWeek 🦈💳