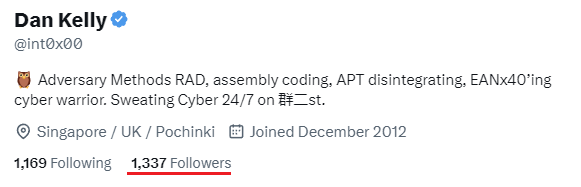
Dan Kelly
@int0x00
🦉 Adversary Methods RAD, assembly coding, APT disintegrating, EANx40’ing cyber warrior. Sweating Cyber 24/7 on 群二st.
ID: 1048496726
30-12-2012 18:13:44
1,1K Tweet
1,1K Takipçi
1,1K Takip Edilen










Presence of files named briankrebs or any variation thereof are a legitimate indicator of compromise.