Nicolas D
@_homeostasie_
Security Researcher. Reversing for finding and exploiting various bugs. Mainly focused on Windows both user and kernel. Combining security improvement with fun.
ID: 1078241275378352128
27-12-2018 10:48:47
265 Tweet
531 Takipçi
77 Takip Edilen






[Tool] Ghidralligator: Emulate and fuzz code running on various CPU architectures (ARM, MIPS, PPC, x86, Apple Silicon M1/M2...) Based on #GHIDRA (libsla C++). #AFLplusplus, snapshot fuzzing, code coverage, ASAN cyber.airbus.com/17300/ github.com/airbus-cyber/g… GuillaumeOrlando


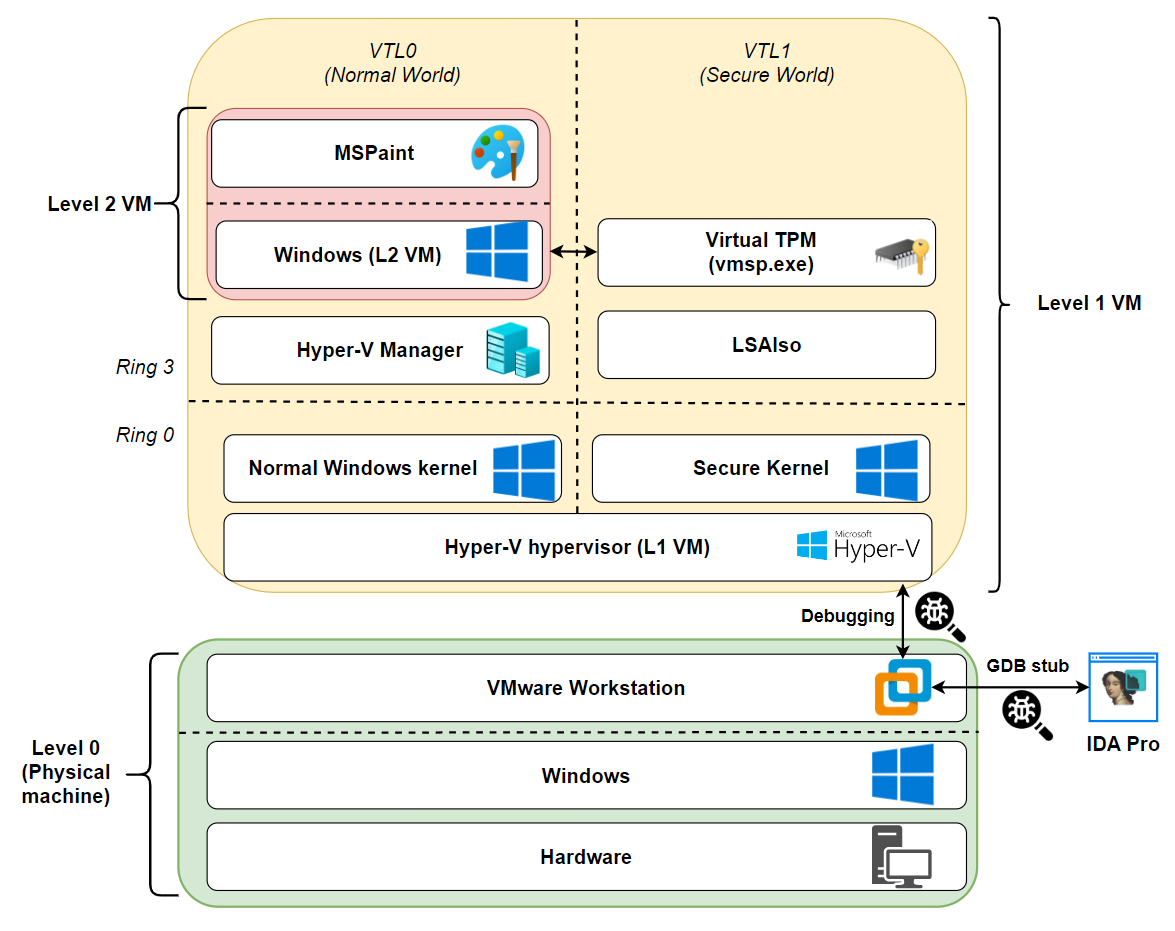
Did you know that Windows processes fundamental to Operating System security run in Isolated User Mode and can not be debugged ? Well that's true except when it isn't. Here Francisco Falcon provides a step by step guide to do it blog.quarkslab.com/debugging-wind… #Windows #ReverseEngineering







This is an excellent series on virtualization and internals of various solutions (QEMU, Xen and VMWare) Credits @LordNoteworthy Intro: docs.saferwall.com/blog/virtualiz… VMWare: docs.saferwall.com/blog/virtualiz… Xen: docs.saferwall.com/blog/virtualiz… QEMU: docs.saferwall.com/blog/virtualiz… #infosec


Exploiting the NT Kernel in 24H2: New Bugs in Old Code & Side Channels Against KASLR by @[email protected] exploits.forsale/24h2-nt-exploi…