Role Of #ArtificialIntelligence In #Cybersecurity
bit.ly/2FjGtcM
#Cybersecurity AI #AI #CyberAttacks #AI Cybersecurity


#ArtificialIntelligence #Trends2023
1. #PredictiveAnalytics #ERP
2. #Hyperautomation
3. #CybersecurityAI
4. Augmented Process
5. #AIOps
6. Automated #MachineLearning
7. NLP-based systems
8. #VoiceCommands
9. Quantum AI
10. #EdgeAI
Read more: bit.ly/3Ycx21t
#TechTrends


Empowering defenses against evolving threats!
Know More - ariespro.com
#AICybersecurity
#AIinSecurity
#CyberDefenseAI
#AIforCyber
#CybersecurityTech
#AIProtection
#CyberThreatDetection
#AIvsCyberThreats
#SecureAI
#CyberSecurityAI
#AIinInfoSec
#CyberAI


Innovation flourishes in places like Silicon Valley, where risk-taking is part of the culture.
In tech hubs around the world, the right environment is key. Now, we ask: Are we creating the ideal ecosystem for #AI in cybersecurity?
#Innovation #CybersecurityAI



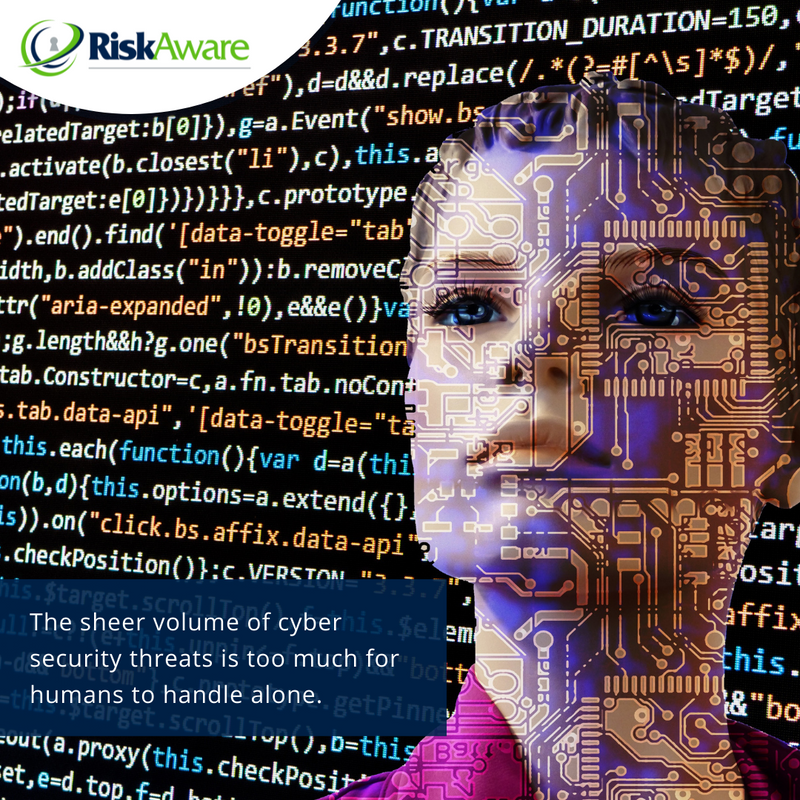
🤖 As a result, enterprises rely on artificial intelligence (AI) and machine learning to fine-tune their security infrastructure.
#VCISO #RiskAwareCo #InfoSec #CyberSecurity #CanadaCiso #Breach #AI #CybersecurityAI

6 Things to Do After Implementing #Cybersecurity #AI for Alert Management ......
#Cybersecurity AI #IBMSecurity #SecurityIntelligence
IBM Security securityintelligence.com/articles/6-thi…



The Confluence of Cybersecurity and AI: Shaping the Future of Digital Defense
Read More: ideaspark.co.in/discuss/the-co…
#CybersecurityAI #DigitalDefense #AIInnovation #FutureOfSecurity #CyberThreats #AIIntegration #DataProtection #AdaptiveSecurity #EthicalAI #PredictiveInsights


Want to know what cyber security thinks about AI? Is it beneficial or detrimental?
#cybersecurityindonesia #cybersecurityprofessional #cybersecuritychallenge #cybersecurityai #aicybersecurity #xapiensteknologiindonesia #itconsultant #itindonesia #programmerindonesia


AI-driven cybersecurity systems protect digital infrastructure, mitigating cyber threats and attacks. ��️ #CybersecurityAI #ThreatMitigation

Where's the next big AI leap happening? Follow the innovation map!
Reach us : ariespro.com
#AI #ArtificialIntelligence #GlobalInnovation #TechnologyTrends #FutureOfWork #CybersecurityAI #SustainableDevelopment #DataScience #MachineLearning #DeepLearning #BigData


Rising AI Cybersecurity Threats
A UK report highlights the potential surge in cyber threats due to AI advancements. #CybersecurityAI #AIinCyberthreat


Businesses are spending on establishing and enhancing their presence through AI.
Read More: montdigital.com/news/ai-based-…
#cybersecurityai #aisecurity #artificialintelligenceforcybersecurity #aicybersecurity montdigital.com/news/ai-based-…

From deepfakes to social engineering, here's what to know about elections, cybersecurity and AI
weforum.org/agenda/2023/11…
#ElectionSecurity #CybersecurityAI #SocialEngineering #DigitalThreats #CybersecurityChallenges #DigitalManipulation #ElectionIntegrity #PelionCyberSecurity

Discover Binare's mission through the lens of #Binare Projects 👇
'CySAI', CyberSecurityAI) automating cybersecurity ( #vulnerability discovery, correlation, defense) by applying #AI solutions'
lnkd.in/dBzPJBYC
#StairwAI #CySAI #Binare Projects #Binare #Binare Team #AI #ML



If there was ever a need to talk about integrating cybersecurity AI into your enterprise, it’s now.
#Cybersecurity #AI #Cybersecurity AI
buff.ly/30mVnUM

6 Things to Do After Implementing #Cybersecurity #AI for Alert Management
#Cybersecurity AI #IBMSecurity #SecurityIntelligence
IBM Security securityintelligence.com/articles/6-thi…