sh0ck @ DEFCON 33
@sh0cksec
Red Teamer | RFID hacking + Physical Intrusions | 4x DEFCON Speaker | When you find out how simple it is to bypass your security, it can be quite shocking.
ID: 1519367167145394183
https://github.com/sh0ckSec 27-04-2022 17:25:40
89 Tweet
130 Followers
220 Following


Day 2 just got started at Ekoparty | Hacking everything! Learn how to open locks at the physical security stand with the Physical Security Village crew! 🔏 #ekoparty2022




Found my outfit for my next red team engagement at a mattress factory with sh0ck @ DEFCON 33



Attending #DEFCON31? Add Langston Clement and Daniel Goga's presentations to your schedule! They'll talk company-branded gear at the Social Engineering Community village and RFID cloning at the Physical Security Village village. Conference details and event schedule here >> bit.ly/3OtKWJ8


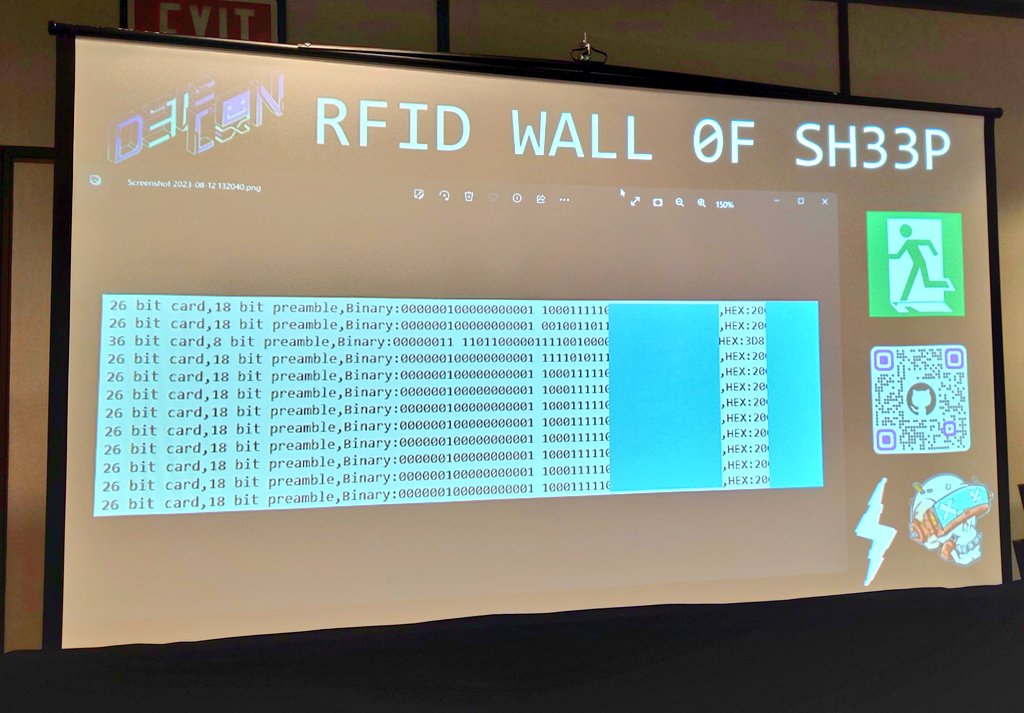
Did we mention we have some super cool external displays and guests this year? sh0ck @ DEFCON 33 and jcache will be making a return with their RFID Gooseneck display, so make sure you hide your RFID credentials! Brian Halbach ☕️ will be bringing door access systems with a (1/3)


(Friday DEFCON31 Schedule Continued) 1:30-2:30 Access Control Vulnerabilities: Breaking Into Buildings With Computers with Chad Spensky from Allthenticate 2:30-3:30 Flipping Locks: Remote Badge Cloning with the Flipper Zero with sh0ck @ DEFCON 33 and jcache (2/3)

Ready to rock these 2 presentations at DEF CON 31. jcache and I brought goodies for each. Come find the kicks and get a sticker! Friday Aug 11 | 2:30-3:30PM | Physical Security Village Remote Badge Cloning with the Flipper Zero Sat Aug 12 | 9:30-10AM l Social Engineering Community Your Swag is my Swag



Don't forget get to check out the new RFID Wall of Sh33P in the Physical Security Village! We caught a quite a few badges so far with the RFID Gooseneck! 😅 #DEFCON31