mithrandir
@rerednawyerg
Malware Analyst
ID: 1506360879721455624
https://rerednawyerg.github.io/ 22-03-2022 20:03:30
84 Tweet
65 Takipçi
102 Takip Edilen



Raccoons are cute but not the stealers 🦝 Check out my latest writeup on Raccoon Stealer esentire.com/blog/esentire-… eSentire Threat Intel








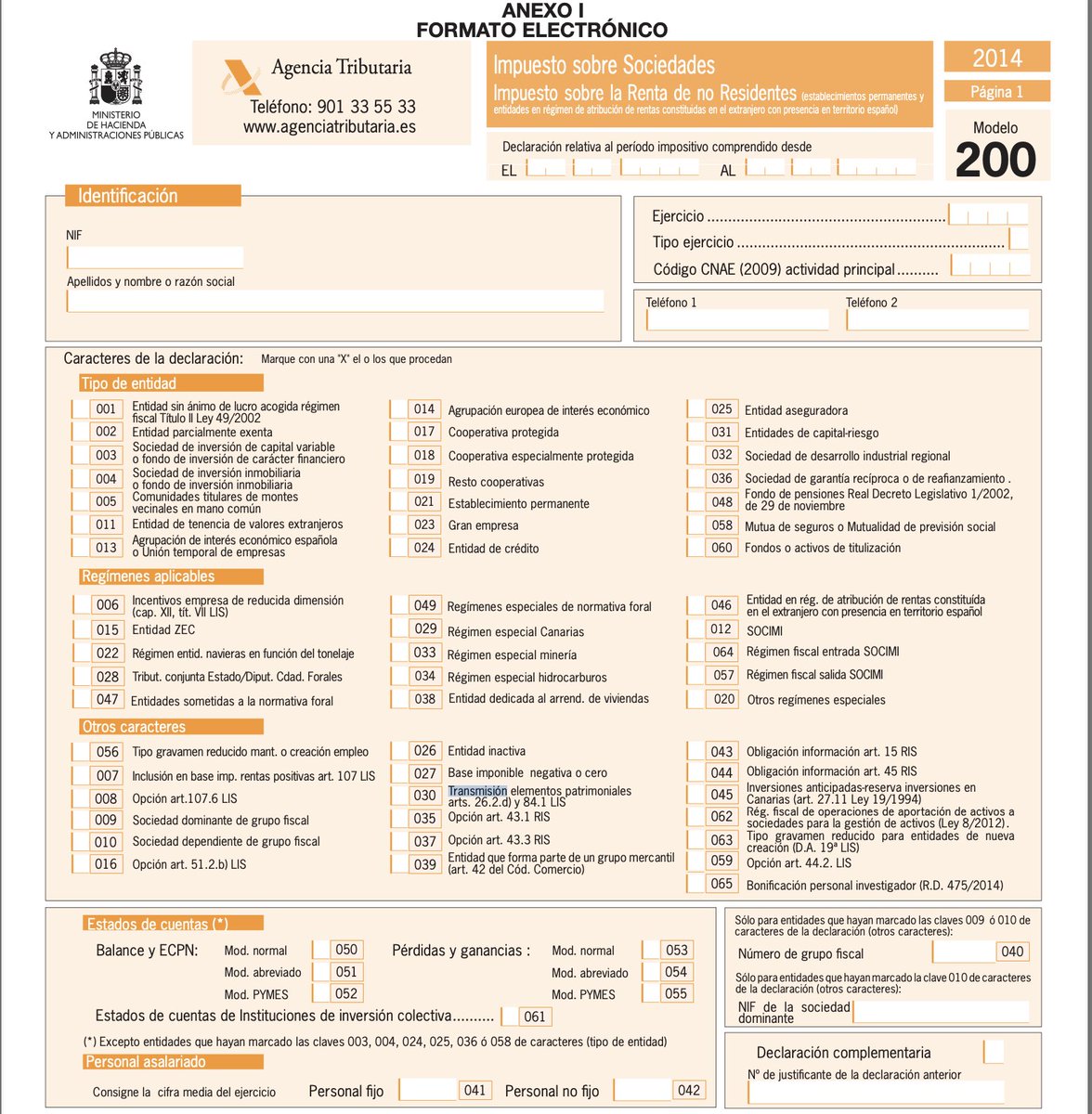
The #xworm campaign targets users in Spain 🇪🇸. 📂 #opendir: 209.126.87[.35:8888 🔗 iz.ps1 - tria.ge/240402-p8r1baa… 🌐 C2: freshinxworm.ddns[.net:7000 CC: Who said what? Germán Fernández





![Unit 42 (@unit42_intel) on Twitter photo 2023-07-12 (Wednesday) - #Gozi/#ISFB infection in an AD environment led to #CobaltStrike C2: 170.130.55[.]162:443 - iamupdate[.]com. List of IOCs at bit.ly/3XO2p3c 2023-07-12 (Wednesday) - #Gozi/#ISFB infection in an AD environment led to #CobaltStrike C2: 170.130.55[.]162:443 - iamupdate[.]com. List of IOCs at bit.ly/3XO2p3c](https://pbs.twimg.com/media/F07JB4MWAAA1vrA.jpg)
![Germán Fernández (@1zrr4h) on Twitter photo Another TryCloudflare domain in this campaign:
dial-posters-corporations-des.trycloudflare[.]com
🔥 FUD "update.cmd": 43feb4c81e9e5be7b22c542dd0d54725075a67dbf592bb65b3b625c04256af55 leads to #AsyncRAT.
C2: mkys[.]duckdns[.]org Another TryCloudflare domain in this campaign:
dial-posters-corporations-des.trycloudflare[.]com
🔥 FUD "update.cmd": 43feb4c81e9e5be7b22c542dd0d54725075a67dbf592bb65b3b625c04256af55 leads to #AsyncRAT.
C2: mkys[.]duckdns[.]org](https://pbs.twimg.com/media/GIVyyYWWkAAH_8r.jpg)