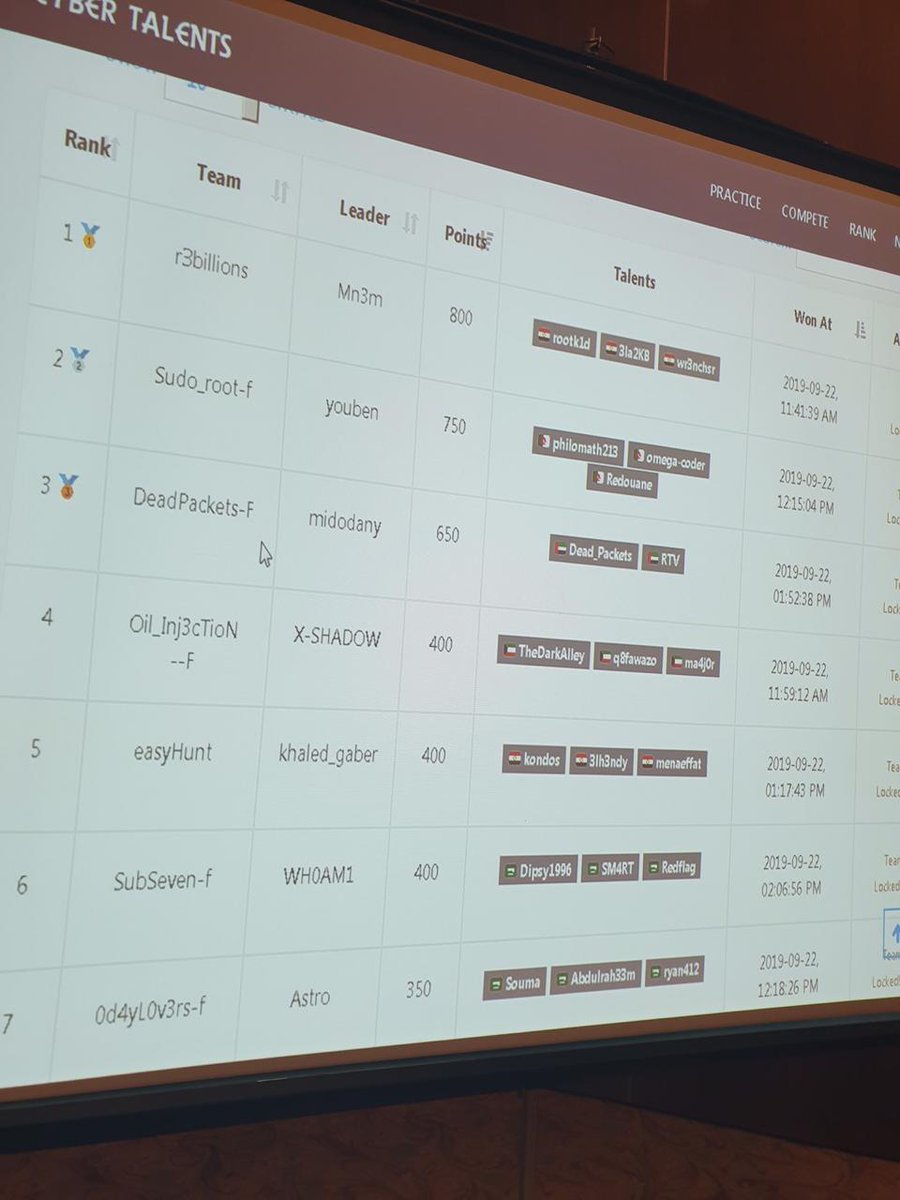
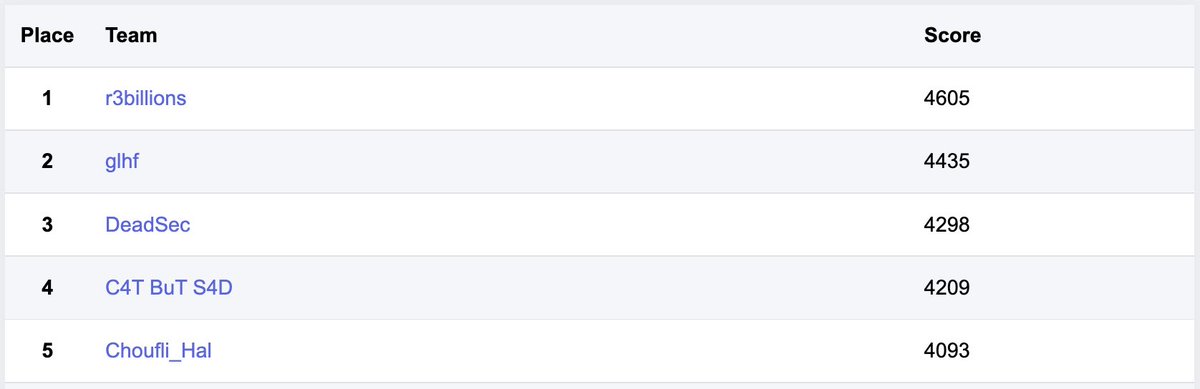
r3billions
@r3billions
A CTF team
ID: 1091343588603113474
https://r3billions.com/ 01-02-2019 14:32:42
22 Tweet
994 Takipçi
6 Takip Edilen













Writeup for a pwn challenge from Dragon CTF by Dragon Sector. The challenge mmaps a 4096 bytes with RWX permissions, takes input into the allocated memory then does some operations on it. 2 bytes of our input gets executed before the program terminates. r3billions.com/writeup-no-eee…



I honestly think r3billions is one of the best CTF teams in the middle east. This is great! but this is also an opportunity to be one of the best in the world :) Don't miss that opportunity ;)


I solved this challenge with worst tweep eune from ADDA CTF. Check our writeup for this one it was an interesting challenge \o/ r3billions.com/writeup-intrus…

Writeup for a pwn challenge from BackdoorCTF by InfoSecIITR. The challenge performs CRUD operations on chucks managed by a custom allocator. r3billions.com/writeup-susall…