Gwaby
@pwissenlit
Sick sad world & caramel
ID: 2919429759
13-12-2014 11:25:45
416 Tweet
1,1K Takipçi
149 Takip Edilen

After lunch, Eloïse Brocas and Forgette Benoît will present at Sthack their adventure at Pwn2Own and how they tried to break randomness with statistics in less than 5minutes #Sthack23




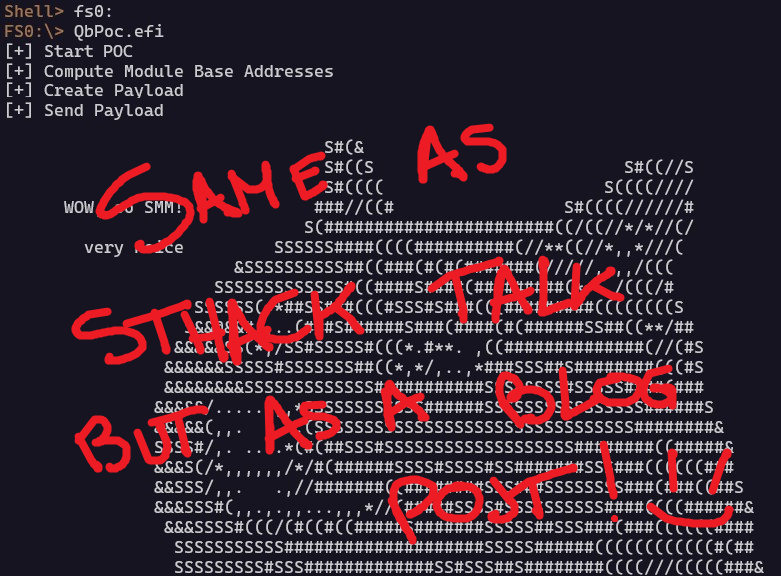
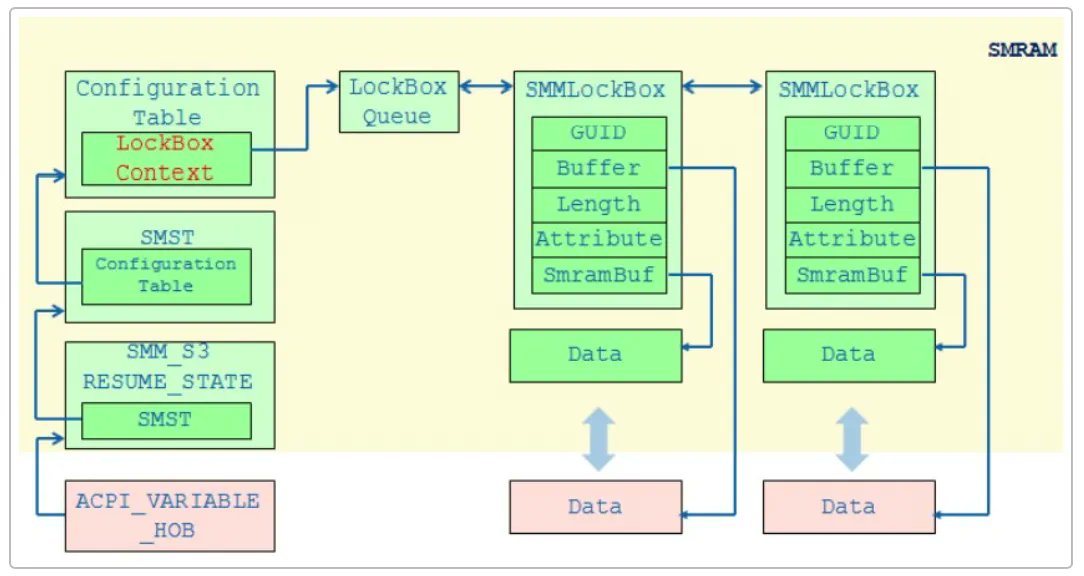
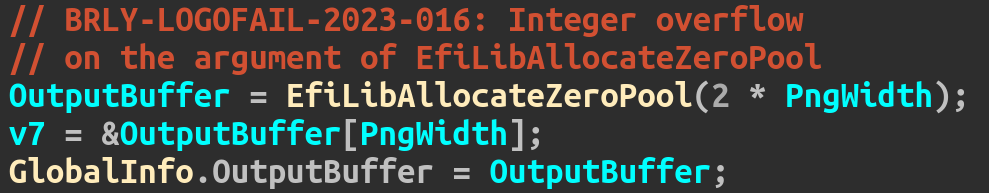
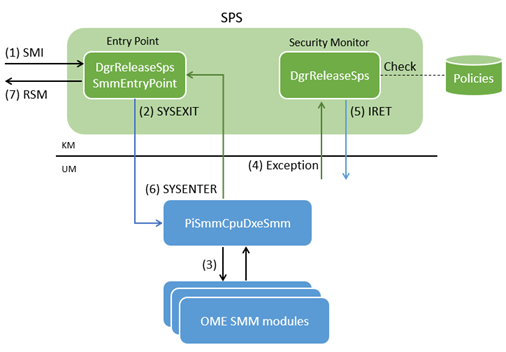
Is remote code execution in UEFI firmware possible? Yes it is. Meet #PixieFAIL: 9 vulnerabilities in the IPv6 stack of EDK II, the open source UEFI implementation used by billions of computers. Full details by Francisco Falcon and iarce in our new blog post: blog.quarkslab.com/pixiefail-nine…


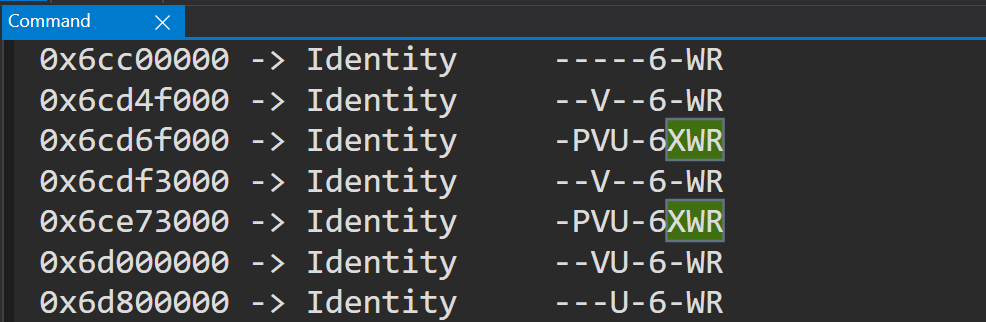
Write up of the HVCI bypass vuln (CVE-2024-21305) with Andrea Allievi ! tandasat.github.io/blog/2024/01/1…



Interested in navigation of source code, binaries and other artifacts? Let a marsupial and goddess help you. Here Eloïse Brocas and Fenrisfulsur introduce Numbat, a new Python API for Sourcetrail, and Pyrrha, a mapper collection for firmware cartography. blog.quarkslab.com/leveraging-sou…


Better late than never! The slides of our talk "Attacking Samsung Galaxy A* Boot Chain" at offensivecon can be found here: github.com/quarkslab/conf… The video is also available: youtube.com/watch?v=WJ7wkJ…


Finding and chaining 4 vulns to exfiltrate encryption keys from the Android Keystore on Samsung series A* devices. Did you miss the "Attacking the Samsung Galaxy A* Boot Chain" talk by Maxime Rossi Bellom and Raphaël Neveu earlier this year ? Talk && PoC || GTFO: blog.quarkslab.com/attacking-the-…