Powerpointken
@powerpointken
ID: 1481519720503431172
https://powerseb.github.io 13-01-2022 06:53:50
219 Tweet
103 Followers
380 Following
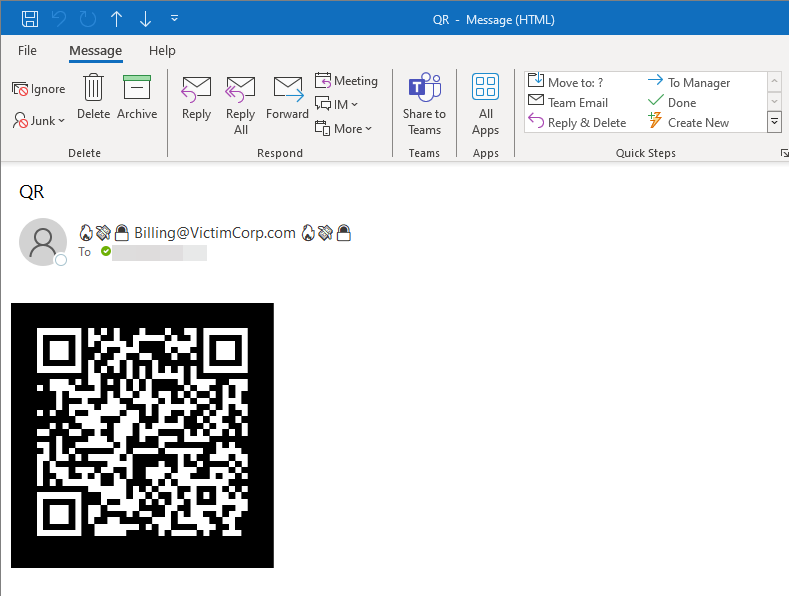
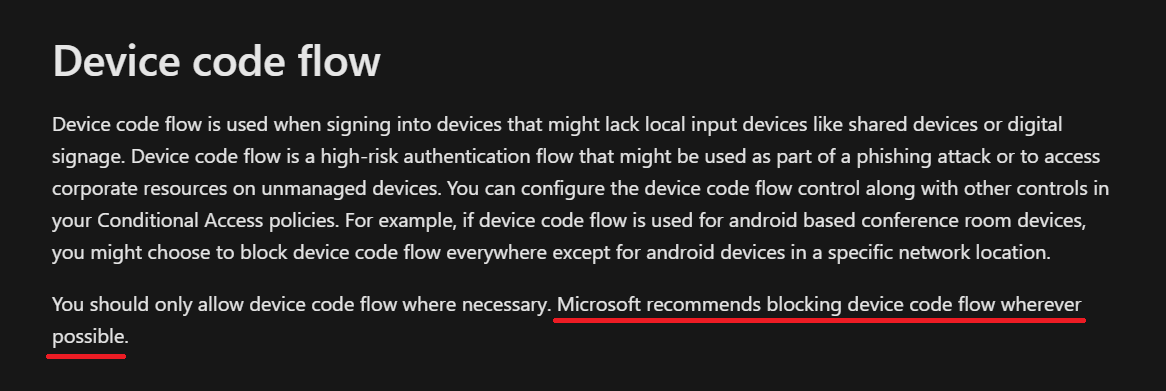
Not sure how I missed this! Luke Kavanagh (Luke Kavanagh) has exhausted the topic on all the mitigations you can implement to protect your users from reverse proxy phishing 🔥🎣 Recommended reading not only if you are on the defense. bleekseeks.com/blog/how-to-pr…