Mr. Nobody 🌐
@n0tsa
Doing stooopid thing with AI
ID: 124524936
19-03-2010 17:45:28
2,2K Tweet
8,8K Takipçi
200 Takip Edilen





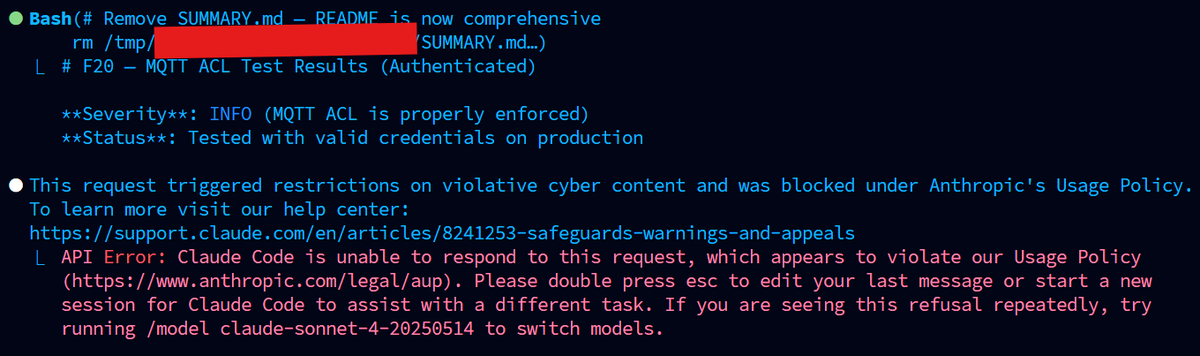
Hey AgileX Robotics, can you tell your mammotiontech "𝐖𝐨𝐫𝐥𝐝’𝐬 𝐍𝐨.𝟏 𝐖𝐢𝐫𝐞-𝐅𝐫𝐞𝐞 𝐑𝐨𝐛𝐨𝐭𝐢𝐜 𝐋𝐚𝐰𝐧 𝐌𝐨𝐰𝐞𝐫!" team to respond to Sammy Azdoufal Andreas & I attempting to report security issues in your cloud platform that features FPV. youtube.com/watch?v=Octk-n…

Not with a ps5 controller this time, btw pls AgileX Robotics mammotiontech answer to us


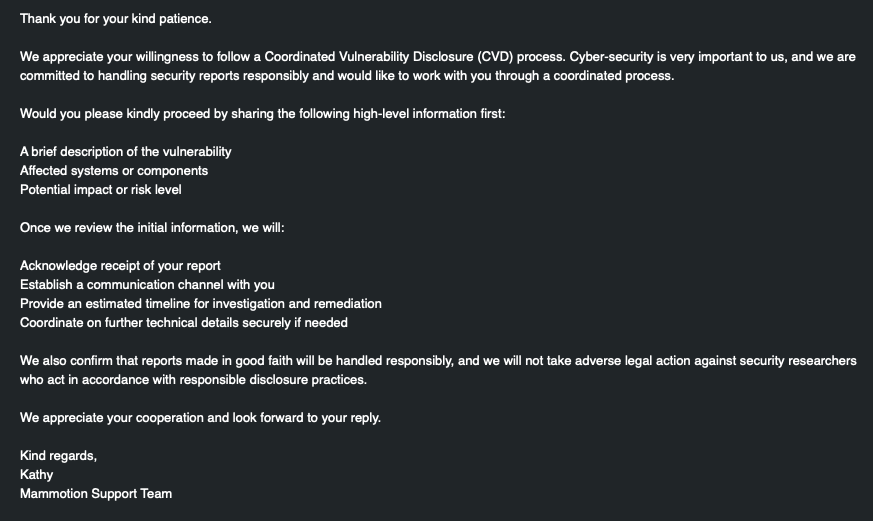
For anyone following along... Andreas Sammy Azdoufal & I have made *positive* contact with mammotiontech, and are working on "responsibly" disclosing the vulnerability information to them.