Mateusz Olejarka
@molejarka
OSWE, HTTP requests forger, Head of Web Security @SecuRingPL
ID: 2995537431
24-01-2015 10:05:37
1,1K Tweet
786 Takipçi
259 Takip Edilen





🌪️Broken isolation - draining your credentials from popular macOS password managers by Wojciech Reguła at #TyphoonCon24! You still have a few more hours to submit your talk and join Wojciech in Seoul! Submit your talk at: typhooncon.com/call-for-paper…







Join us at @TyphoonCon in Seoul on May 27-31! Wojciech Reguła will talk about broken isolation and draining credentials from popular macOS password managers. #typhooncon #itsec #cybersec typhooncon.com/blog/conitems/…


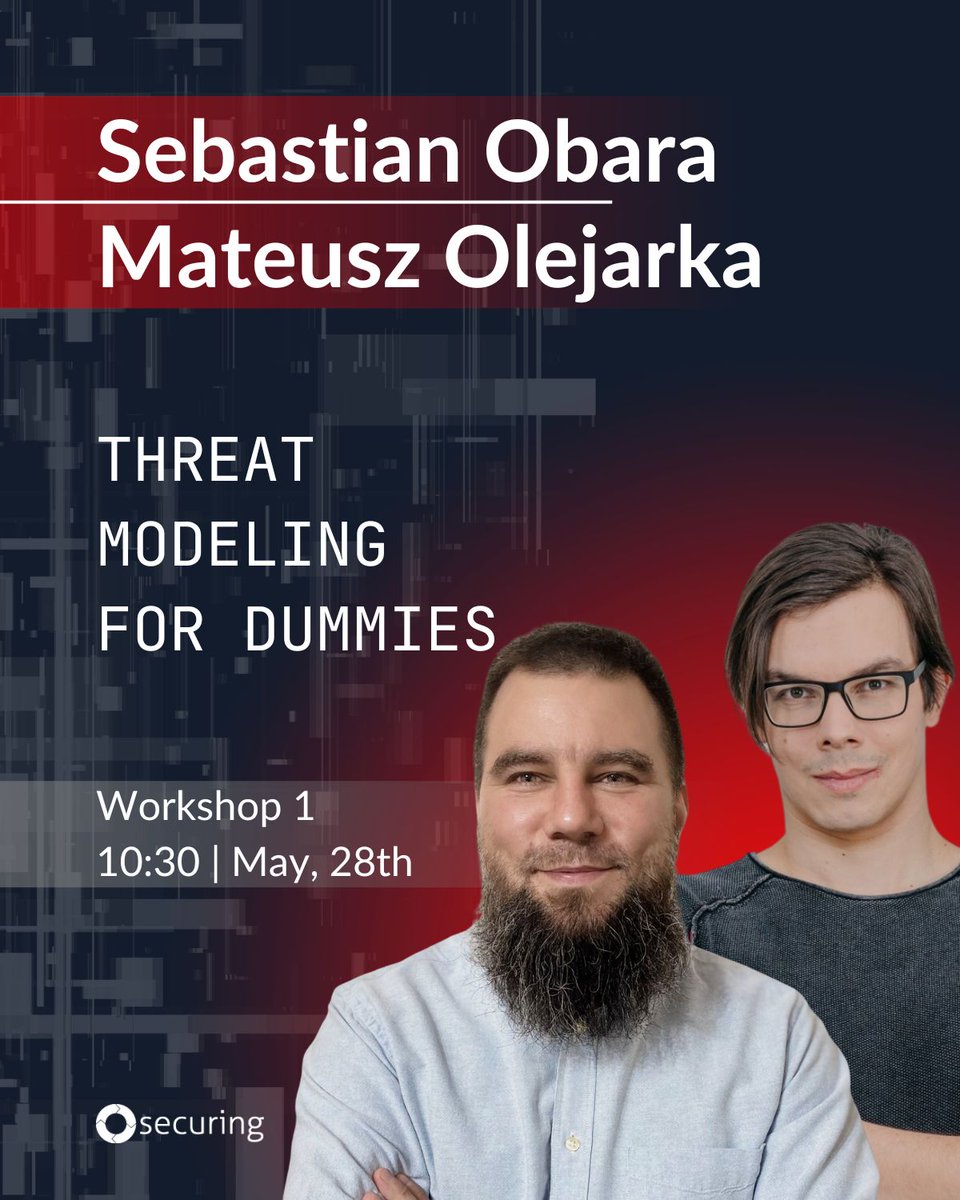
Ever wondered how experts tackle real-world security issues? 💡 Join us at confidenceconf and bridge the gap between theory and practice!


Uwierzytelnienie użytkownika to sprawa trudna. Ostatnie lata przyniosły nam wysyp i coraz większą adopcję rozwiązań Single Sign On. 🔒 To i dobrze, i źle. Dlaczego? O tym dokładniej opowie Mateusz Mateusz Olejarka! Jego wykład zobaczycie już 26 listopada 🔜 omhconf.pl