MAD Security
@madsecurityllc
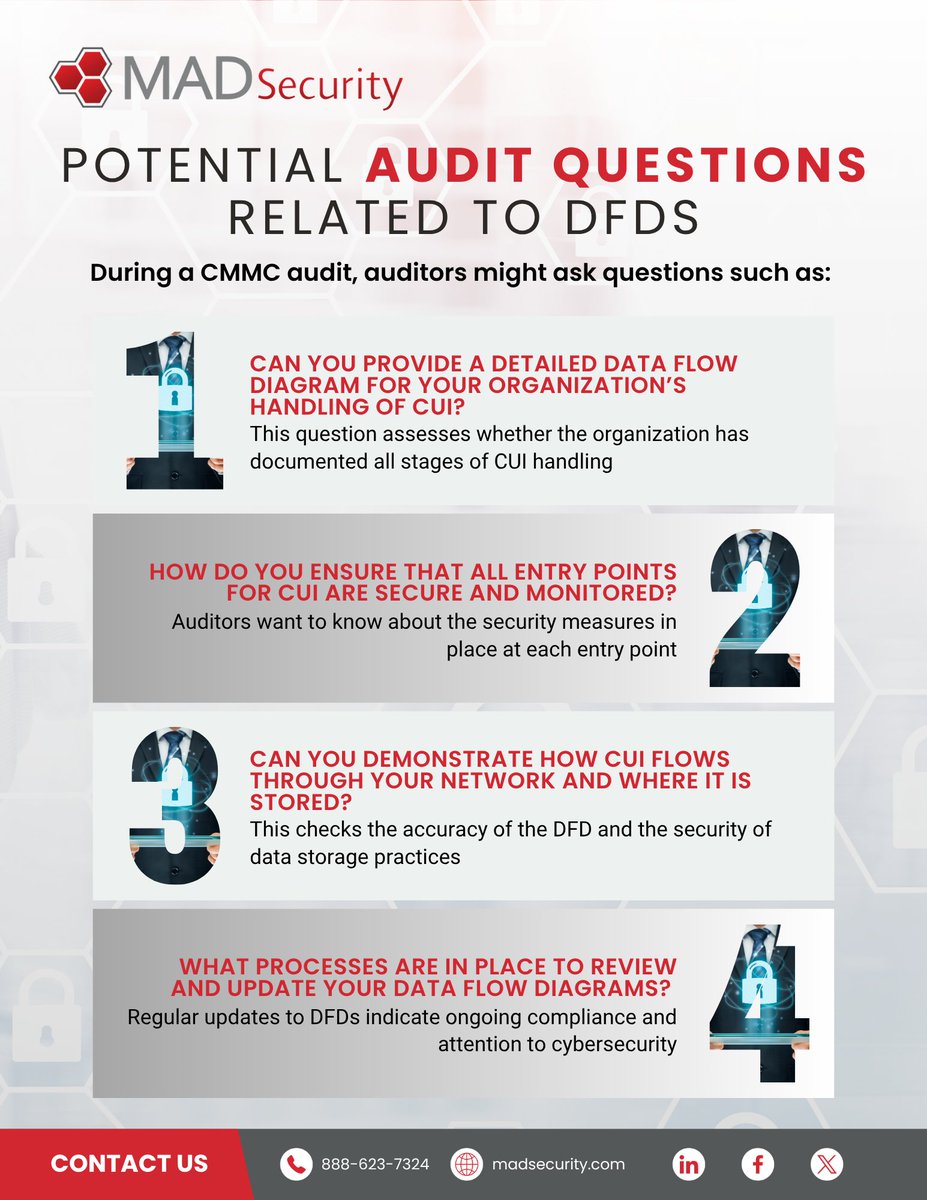
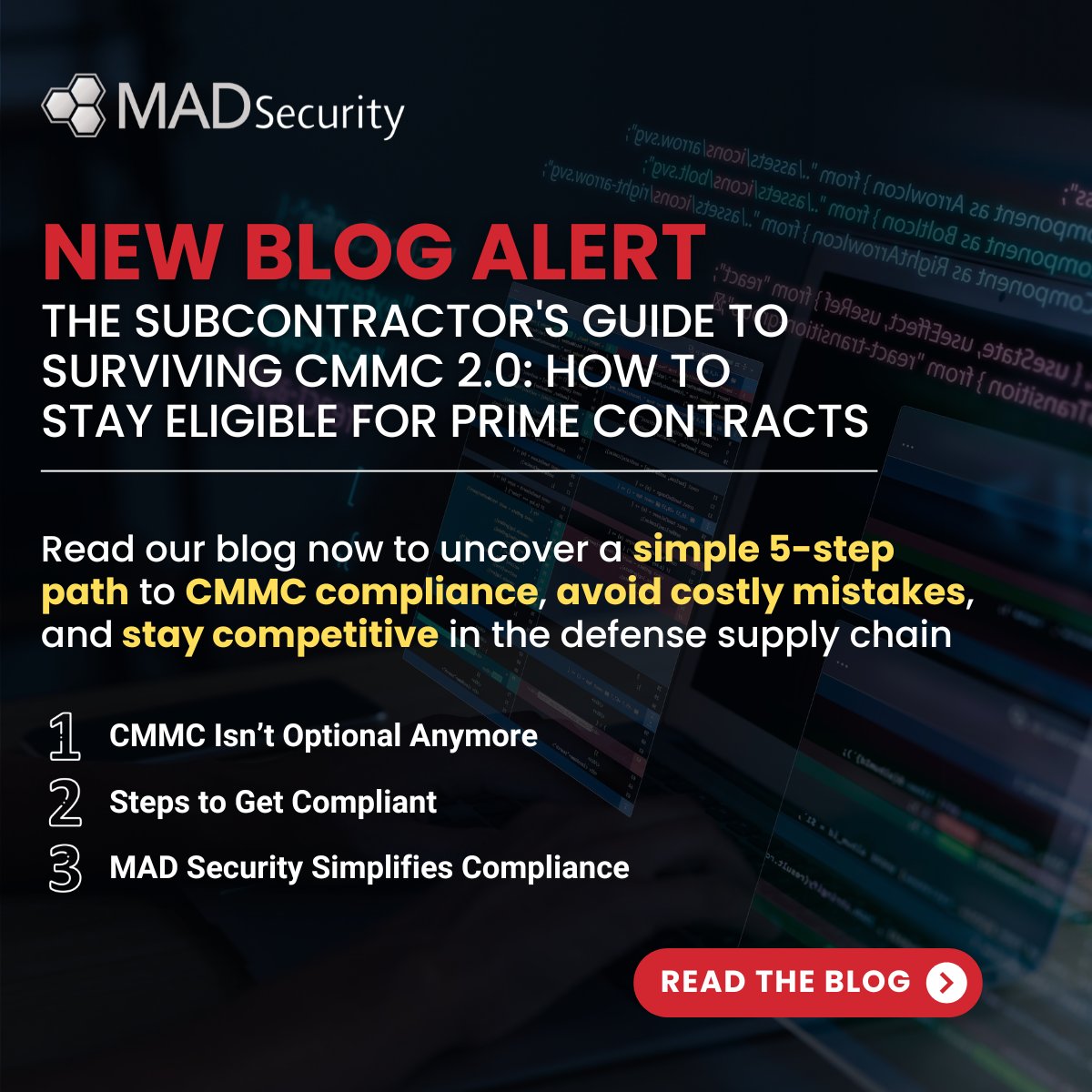
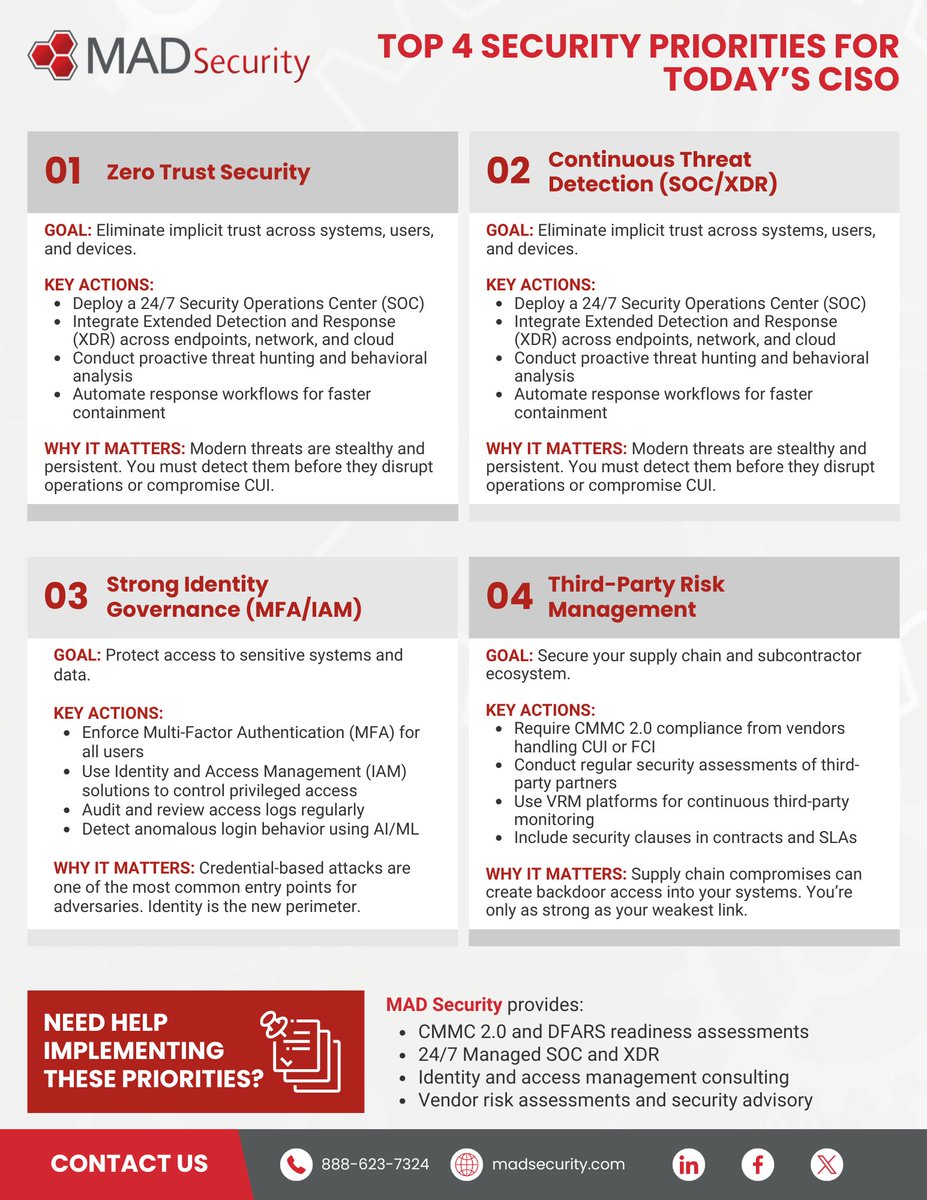
MAD Security is a premier provider of information and cybersecurity solutions that combine technology, managed security services, support, and training.
ID: 215016600
http://www.madsecurity.com 12-11-2010 20:09:20
3,3K Tweet
1,1K Followers
2,2K Following