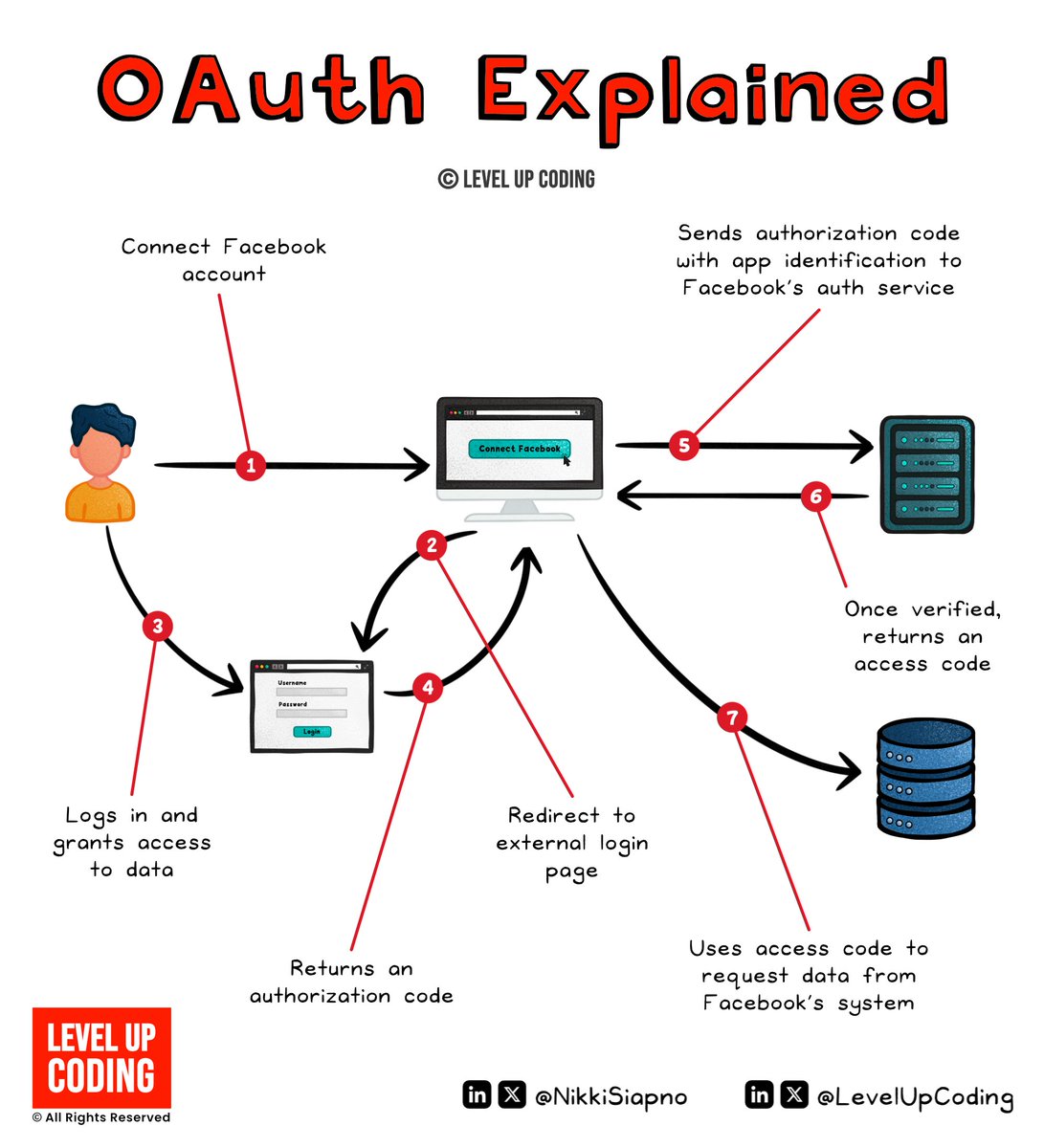
Level Up Coding
@levelupcoding_
Level up your engineering & system design skills.
Complex topics simplified.
Thank you to our partner @getpostman who keep our content free to the community
ID: 1776205974971486208
https://blog.levelupcoding.com 05-04-2024 11:13:40
309 Tweet
7,7K Takipçi
2 Takip Edilen