xiaopao
@kangxiaopao
Focus on ransomware,like cat
ID: 1148077012986187777
http://lesuobingdu.360.cn 08-07-2019 03:51:04
706 Tweet
644 Takipçi
137 Takip Edilen







Last article in March #Vovabol #Ransomware, probably fake encryptor. id-ransomware.blogspot.com/2022/03/vovabo… Uses UA and LV mail accounts, but asks for a ransom on Qiwi wallet. Thank MalwareHunterTeam

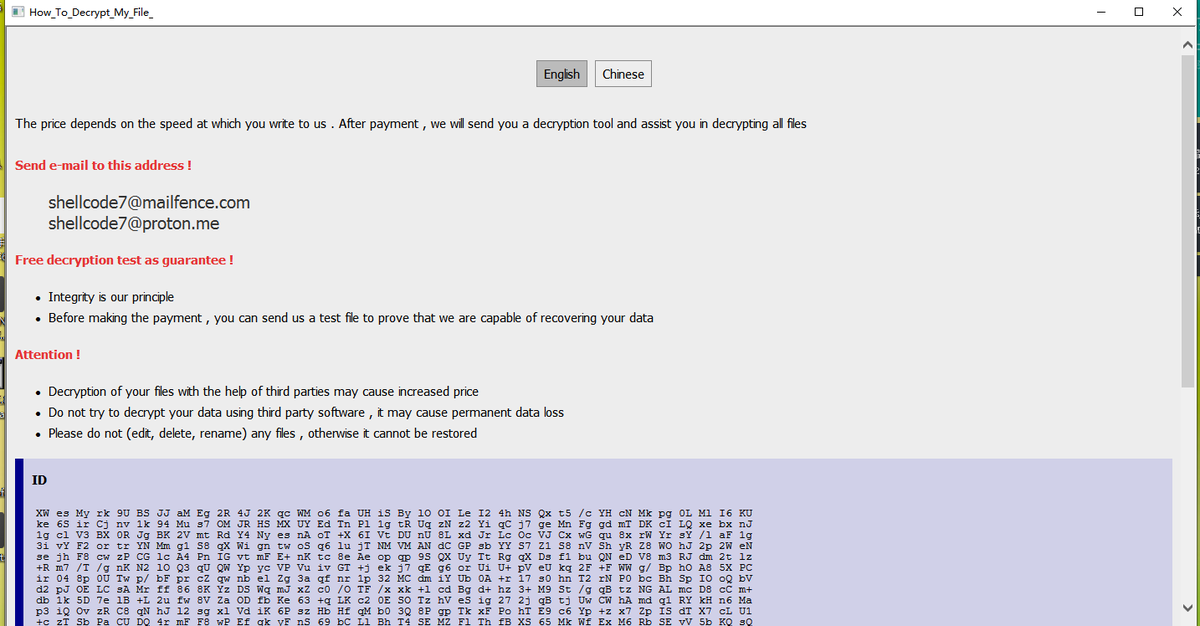
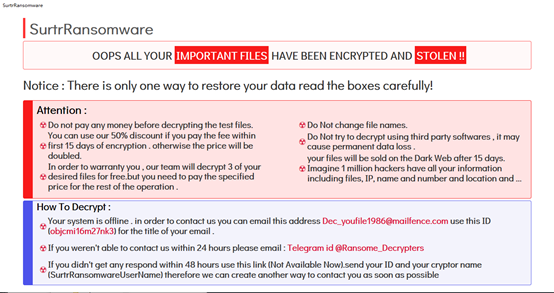
#Ransom maybe this belong to phantom family? mail:[email protected] [email protected] info:README.id.hta ext:id Amigo-A



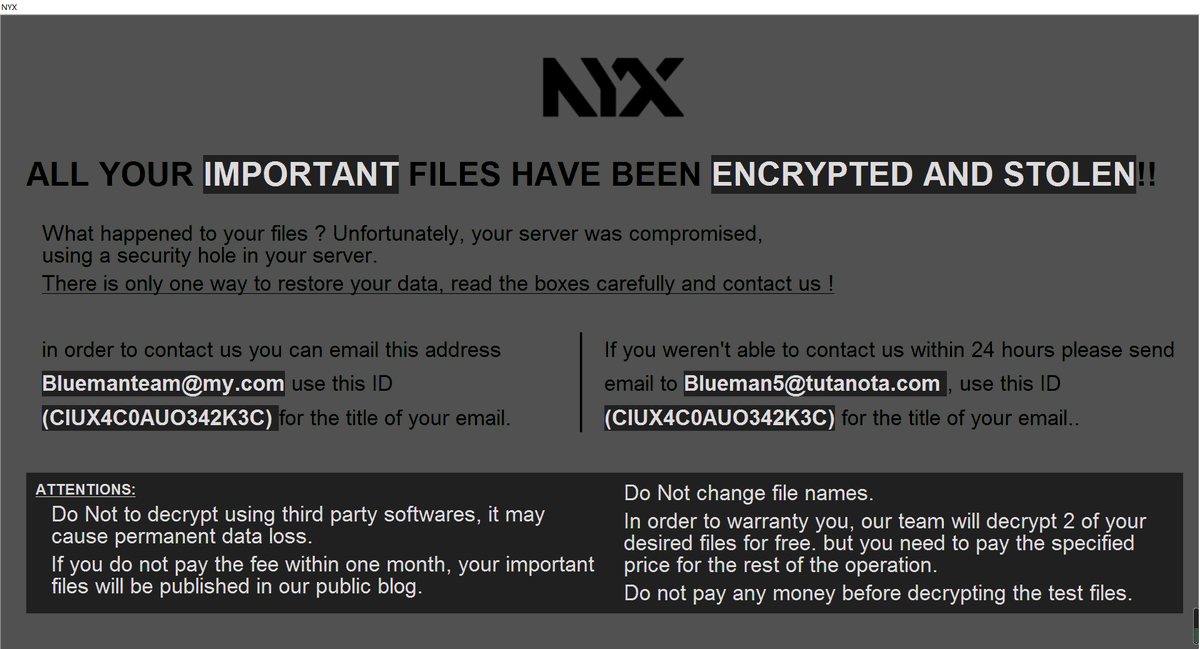
#NYX #ransom ext:NYX mail:[email protected] and [email protected] info:000_NYX_READ_ME3.hta sample:virustotal.com/gui/file/b4ed2… Amigo-A


#Ransomware Wuibei ransom ioc: mai:[email protected] info: 0a___Hello_ReadMe___.TXT notice.txt BTC Wallets: 1Abim6rh3uRkDmxriYY91EaqYXvDdtfcpN 1NYXFKZ2Cgc1765NyDxkLAqdBzyw3VYKQj md5: ca13c0b6043ae7171330c513135b8ce5 a57ce5e81cd9eb3456c8d021101cbbc0 360.cn/n/12481.html



Fusion Intelligence Center @ StealthMole Behind the #DragonRaaS (and the "Stormous" copy-cat's) are two Yemeni Individuals. They "redesigned" the old Logo and also came up with a "#StormCry" Ransomware back in March




![Zscaler ThreatLabz (@threatlabz) on Twitter photo 💰ThreatLabz has discovered a new #ransomware group named Money Message performing double extortion attacks.
Sample hash: bbdac308d2b15a4724de7919bf8e9ffa713dea60ae3a482417c44c60012a654b
Data leak site: blogvl7tjyjvsfthobttze52w36wwiz34hrfcmorgvdzb6hikucb7aqd[.]onion 💰ThreatLabz has discovered a new #ransomware group named Money Message performing double extortion attacks.
Sample hash: bbdac308d2b15a4724de7919bf8e9ffa713dea60ae3a482417c44c60012a654b
Data leak site: blogvl7tjyjvsfthobttze52w36wwiz34hrfcmorgvdzb6hikucb7aqd[.]onion](https://pbs.twimg.com/media/FsZn5OQaAAI0Pw6.jpg)