James Condon
@jameswcondon
Aspiring for a future where cloud security is simple and easy. @laceworklabs
ID: 156148411
https://www.lacework.com/labs/ 16-06-2010 04:12:24
502 Tweet
509 Followers
308 Following


Codecov Bash Uploader hack - attackers stole credentials, tokens and keys from victims. 💥 104.248.94[.]23 💥 6e63a4a1946e81fb07c08e62fd36e1d2 H/T Florian Roth ⚡️ bleepingcomputer.com/news/security/…












the team Lacework Labs just released their latest cloud threat report. full report at bit.ly/lw-ctr-vol2 highlights 👇 ☁️ #cloud #devops #cybersecurity





Episode 69 "Cloud Threats and How to Observe Them" of Cloud Security Podcast where hosts Dr. Anton Chuvakin and Timothy Peacock interview James Condon (James Condon) Lacework about cloud threats cloud.withgoogle.com/cloudsecurity/…


Don't get stuck playing whack-a-mole with your vulnerabilities. ❌ Lacework Labs research shows how #cybercriminals are getting craftier in their attacks—and how to stay steps ahead of them. More from our own James Condon in TechBeacon: laceworkinc.net/3ih4Wmh
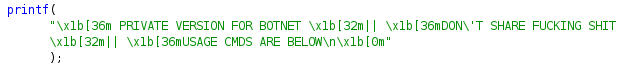
![Lacework Labs (@laceworklabs) on Twitter photo TeamTNT Leveraging Diamorphine to Hide XMRig:
💥 oracle.zzhreceive[.]top
💥 45.9.148.85
💥 45.9.148.35
💥 199.19.226.117
(Diamorphine is a LKM #rootkit for #Linux Kernels 2.6.x/3.x/4.x/5.x and ARM64) TeamTNT Leveraging Diamorphine to Hide XMRig:
💥 oracle.zzhreceive[.]top
💥 45.9.148.85
💥 45.9.148.35
💥 199.19.226.117
(Diamorphine is a LKM #rootkit for #Linux Kernels 2.6.x/3.x/4.x/5.x and ARM64)](https://pbs.twimg.com/media/Ey8RCrgVkAQguvS.png)
![Lacework Labs (@laceworklabs) on Twitter photo 📢 [New TTP] Sysrv evolves and adds persistence to its #PowerShell dropper.
💥 Run location: $env:AppData\sysrv013.exe
💥 Scheduled Task (T1053.005) - "Browser Update"
💥 Run Key (T1547.001) to trigger sysrv013 on boot
#malware #botnet #threatintel 📢 [New TTP] Sysrv evolves and adds persistence to its #PowerShell dropper.
💥 Run location: $env:AppData\sysrv013.exe
💥 Scheduled Task (T1053.005) - "Browser Update"
💥 Run Key (T1547.001) to trigger sysrv013 on boot
#malware #botnet #threatintel](https://pbs.twimg.com/media/Ez63BBhXIAAiJh1.png)