Vaibhav
@stackslash
Team Red @Mandiant @Google
ID: 820314883602477057
http://badbit.vc 14-01-2017 17:01:23
122 Tweet
120 Takipçi
491 Takip Edilen




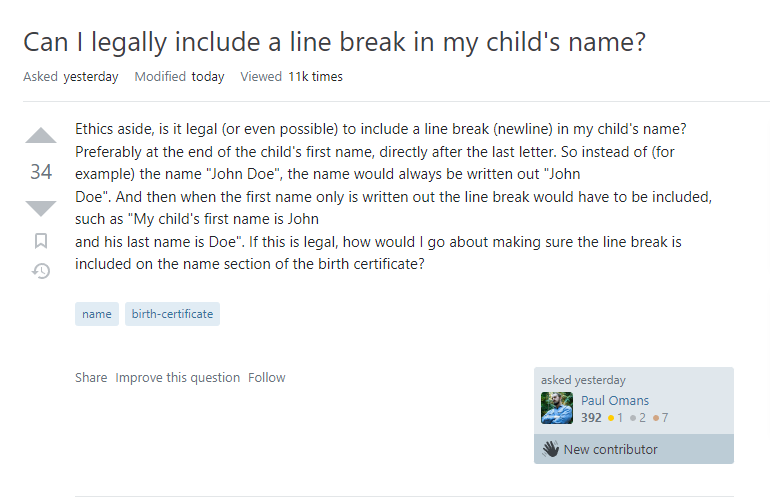
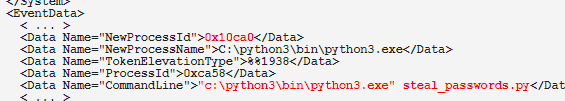
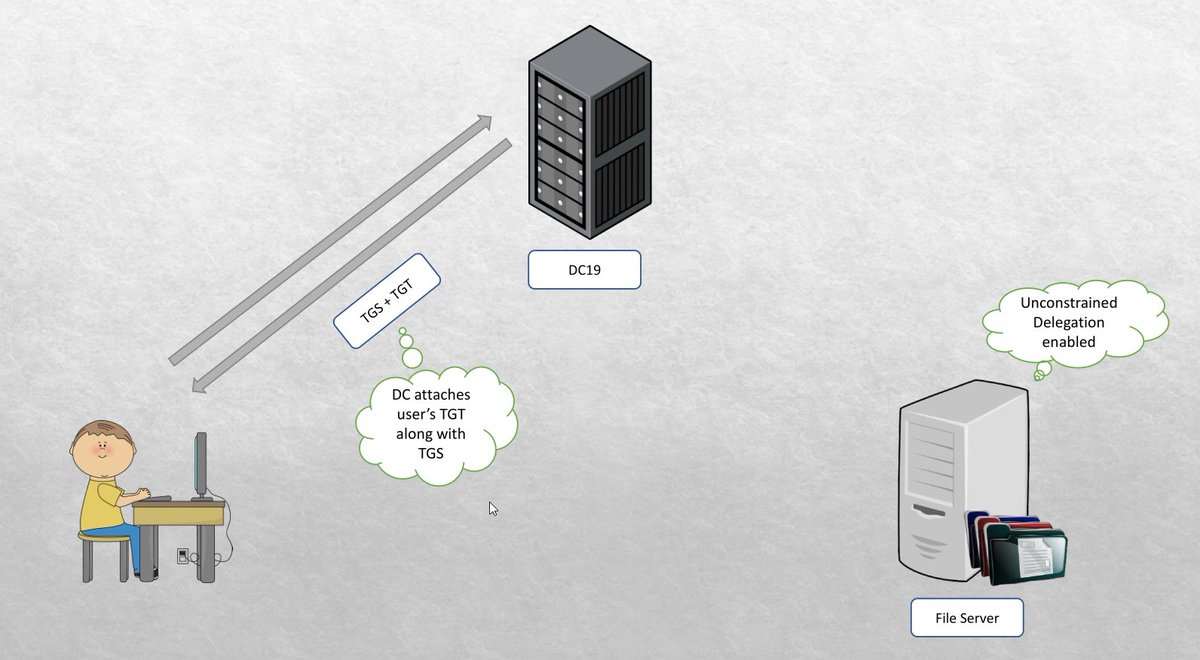
Announcement: Me and Soumyadeep Basu will be giving a free workshop on Offensive Lateral Movement in Windows Environment. Attached is the small glimpse of the content. You can find more details at github.com/dazzyddos/dazz… (1/2).








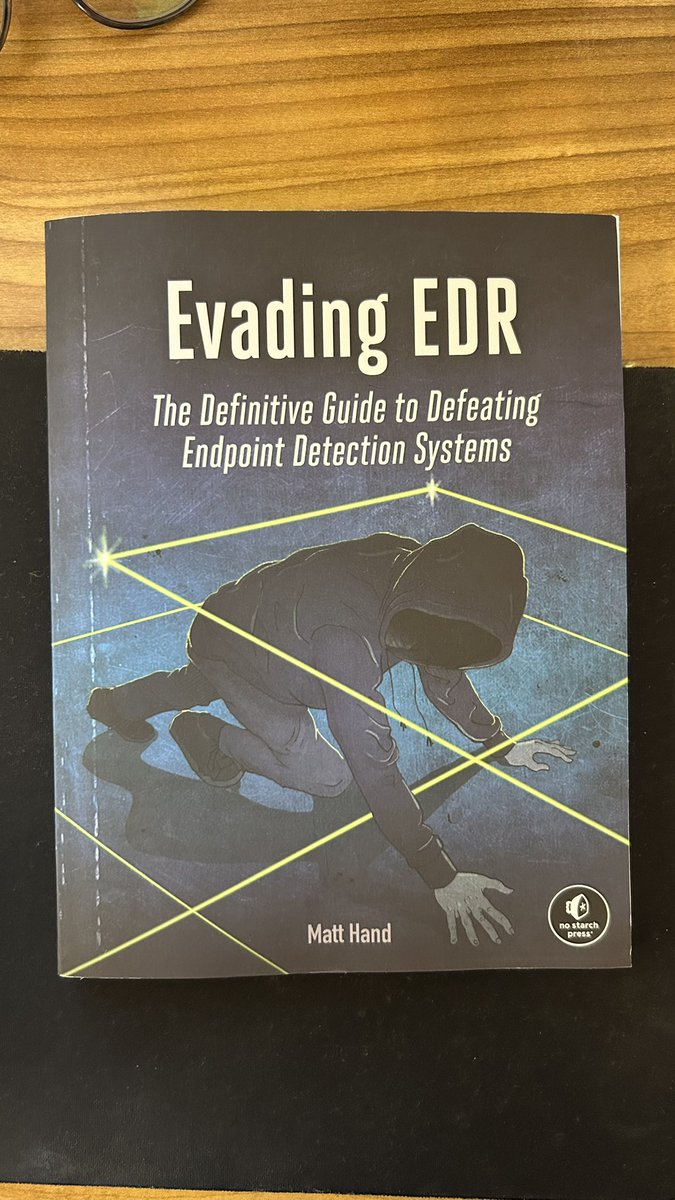
I've long been interested in how EDRs work under the hood and how we can apply a more evidence-based approach to evasion. I'm happy to announce that I've written a book covering these topics with No Starch Press which is now available for preorder 🎉 nostarch.com/book-edr




Some of you were asking for my /ˈziːf-kɒn/ 2024 presentation. I cover: > current state of offsec > why red needs to up its game to stay relevant > entrepreneurship in the offsec world using my past experience. Thanks #x33fcon for having me again!