Miguel Méndez Zúñiga
@s1kr10s
Researcher, Reverser, Pentester, and Speaker. Hacking is my profession and passion. Holder of Offensive security certs: OSCP, OSWP, OSCE, OSWE, OSED.
ID: 76567289
https://s1kr10s.github.io 23-09-2009 05:22:56
3,3K Tweet
1,1K Takipçi
125 Takip Edilen


Reverse engineering the runtime code integrity protection of Call of Duty: Black Ops 3 Blog post by Maurice Heumann buff.ly/3Xwv5N #reverseengineering







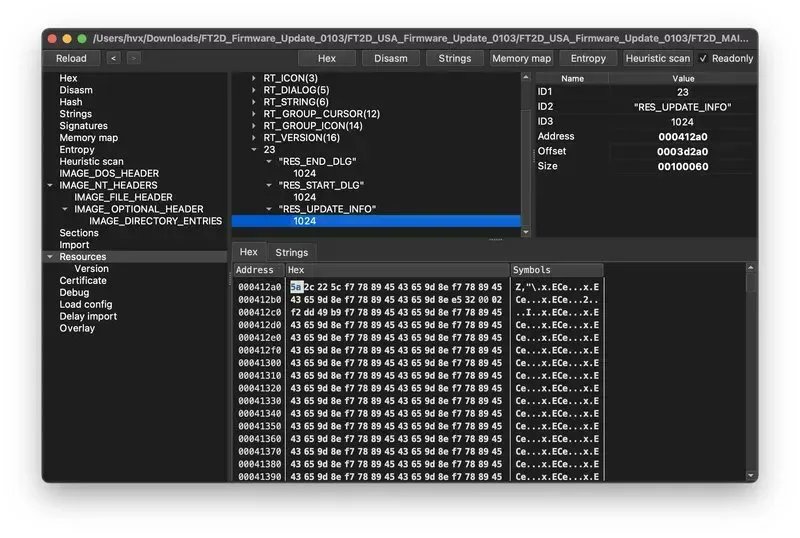
Analysis of Mekotio Malware that affects Chile @CSIRTGOB Curated Intelligence #malware #reversing #research medium.com/@s1kr10s/malwa…


Here, I am sharing a new article in which my friend dplastico (pwn) 🤜 🤛 and I conducted research on specific antivirus binaries. As a result of our investigation, we successfully secured the assignment of CVE-2024-23940 from @TrendMicro. #cve #research medium.com/@s1kr10s/av-wh…






US Government registró el dominio aliens․gov. Lo puedes verificar en: dnschecker.org/#NS/aliens.gov VM Granmisterio