PatchRequest
@patchrequest
Offsec | Reptiles and other fun stuff
ID: 1154492235737686029
25-07-2019 20:42:53
128 Tweet
85 Takipçi
401 Takip Edilen















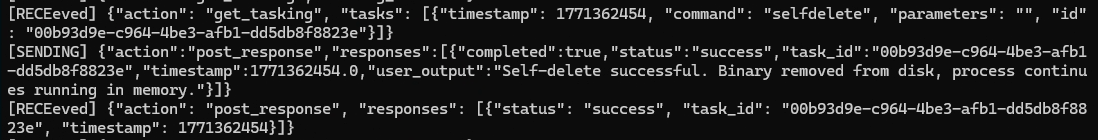
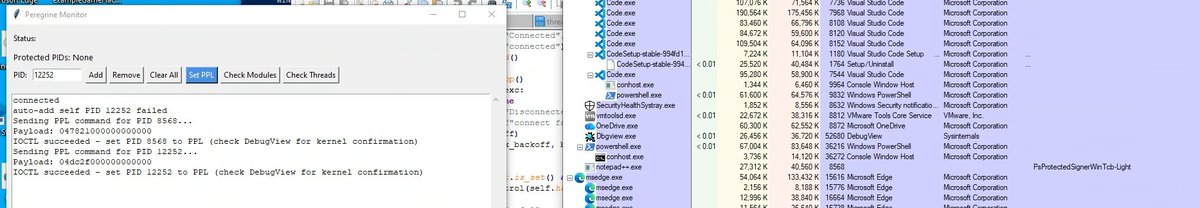
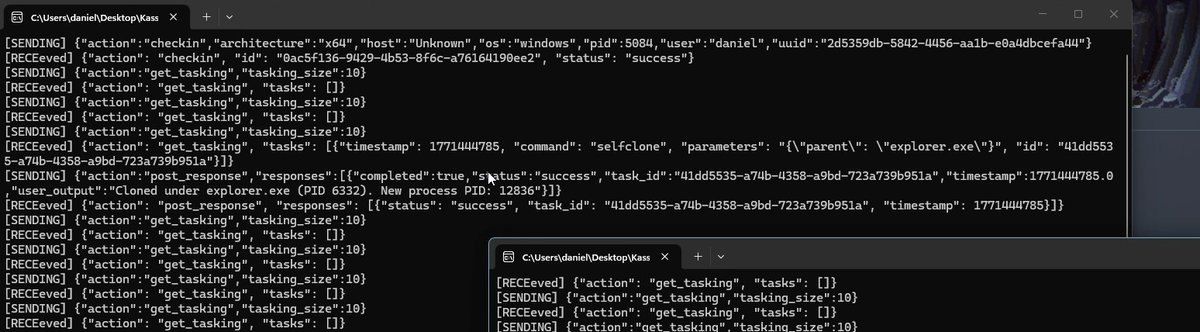
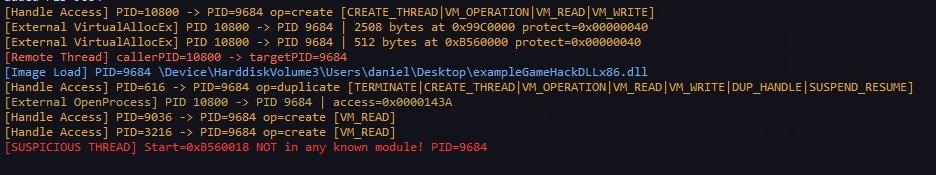
Just implemented self-deletion in my Mythic agent while the process keeps running smoothly. Big thanks to MalDev Academy for the inspiration 🔥 github.com/PatchRequest/K…