MENASecurity
@menasec1
Applied Security Research | Threat Hunting | DFIR | [email protected] 👁🗨
ID: 1102255788251324417
https://blog.menasec.net 03-03-2019 17:13:53
81 Tweet
2,2K Takipçi
40 Takip Edilen














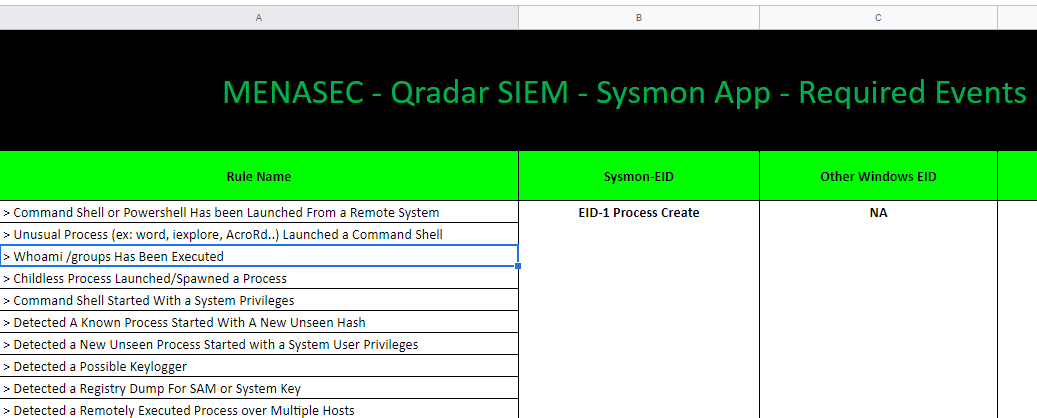
📌How to Design Abnormal Child Processes Rules without Telemetry by MENASecurity [BLOG]➡️ blog.menasec.net/2021/01/how-to… #ThreatHunting #BlueTeam #security #DFIR
![Ring3API 🇺🇦 (@ntlmrelay) on Twitter photo 📌How to Design Abnormal Child Processes Rules without Telemetry by <a href="/menasec1/">MENASecurity</a>
[BLOG]➡️ blog.menasec.net/2021/01/how-to…
#ThreatHunting #BlueTeam #security #DFIR 📌How to Design Abnormal Child Processes Rules without Telemetry by <a href="/menasec1/">MENASecurity</a>
[BLOG]➡️ blog.menasec.net/2021/01/how-to…
#ThreatHunting #BlueTeam #security #DFIR](https://pbs.twimg.com/media/Eq6wl2gXIAMP7O_.jpg)


Integrating process protection level information into all #EDR #Sysmon events. As suggested by MENASecurity in blog.menasec.net/2022/04/auditi… using Win API instead of checking RunAsPPL registry key (which seem to apply only to lsass) #dfir #threathunting github.com/0xrawsec/whids

Just pushed the code to embed process protection level in severa events of our #opensource #EDR #dfir #threathunting github.com/0xrawsec/whids thanks to MENASecurity for the idea


![MENASecurity (@menasec1) on Twitter photo [Credential Access] - short write-up explaining one way to detect malicious programs dumping browser's saved credentials or permanent cookies 👉 blog.menasec.net/2019/04/creden… … #ThreatHunting #DFIR [Credential Access] - short write-up explaining one way to detect malicious programs dumping browser's saved credentials or permanent cookies 👉 blog.menasec.net/2019/04/creden… … #ThreatHunting #DFIR](https://pbs.twimg.com/media/D3KRTdyW4AIn3G1.png)
![MENASecurity (@menasec1) on Twitter photo [Credential Access] - KeePass.exe credential dumping using KeeFarce.exe can be detected using the following SIGMA rule #ThreatHunting #DFIR #SIGMA [Credential Access] - KeePass.exe credential dumping using KeeFarce.exe can be detected using the following SIGMA rule #ThreatHunting #DFIR #SIGMA](https://pbs.twimg.com/media/D3UxWpsW0AELiFj.png)