Faan Rossouw
@faanross
| threat hunting researcher @ActiveCmeasures + educator @Antisy_Training | building aionsec.ai | panta rhei |
ID: 2001684784377196544
http://www.faanross.com 18-12-2025 16:03:51
104 Tweet
46 Takipçi
233 Takip Edilen







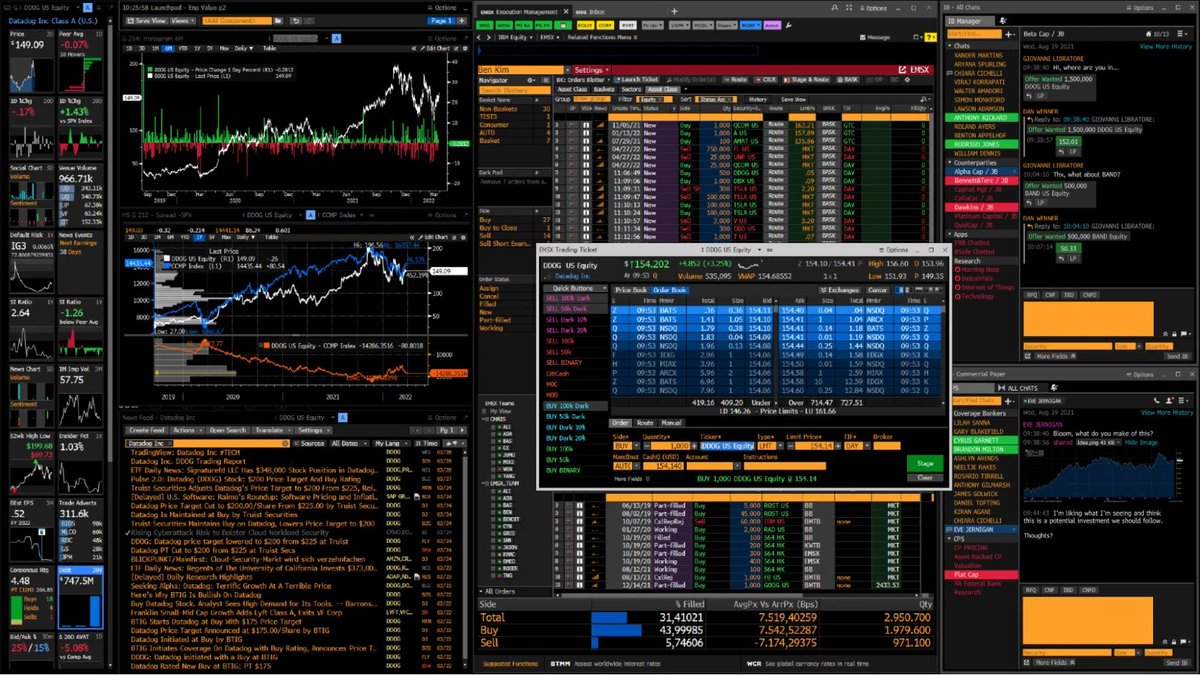
Malware doesn't scream; it whispers in a rhythm. Faan Rossouw simulated and analyzed C2 traffic to decode these hidden heartbeats. Recognizing the pattern is how you find the breach. Read here: activecountermeasures.com/malware-of-the…

Just ran my first ever scheduled Upgrade Skill this Saturday, truly a baller idea thanks ᴅᴀɴɪᴇʟ ᴍɪᴇssʟᴇʀ 🛡️


Join me this Friday for an awesome hands-on 4-hour workshop hosted by Antisyphon Training where we'll be creating a modular command handling system for a C2 system in Golang. It all culminates in implementation of a reflective shellcode loader and popping calc.exe on a hapless


The adversary hides in the encryption you provide. When DNS goes dark, defenders go blind. Faan Rossouw simulated and analyzed the traffic to find the signal. activecountermeasures.com/malware-of-the…